mirror of
https://github.com/prowler-cloud/prowler.git
synced 2026-05-16 09:12:47 +00:00
Compare commits
217 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| 6dee12450e | |||
| eecb1dd8c3 | |||
| 74add0c151 | |||
| 1cf86350bc | |||
| e9b09790da | |||
| c74b4adf27 | |||
| a769bb86d3 | |||
| f8a2527429 | |||
| ae645718ad | |||
| a0625dff2f | |||
| 37e9cbbabd | |||
| 8818f47333 | |||
| 3cffe72273 | |||
| 135aaca851 | |||
| cf8df051de | |||
| bef42f3f2d | |||
| 3d86bf1705 | |||
| 5a43ec951a | |||
| b0e6ab6e31 | |||
| b7fb38cc9e | |||
| f29f7fc239 | |||
| 2997ff0f1c | |||
| 11dc0aa5b2 | |||
| 8bddb9b265 | |||
| 689e292585 | |||
| bff2aabda6 | |||
| 4b29293362 | |||
| 4e24103dc6 | |||
| 3b90347849 | |||
| 6a7a037cec | |||
| 927c13b9c6 | |||
| 11cc8e998b | |||
| 4a71739c56 | |||
| aedc5cd0ad | |||
| 3d81307e56 | |||
| 918661bd7a | |||
| 99f9abe3f6 | |||
| f2950764f0 | |||
| d9777a68c7 | |||
| 2a4cc9a5f8 | |||
| 1f0c210926 | |||
| dd64c7d226 | |||
| 865f79f5b3 | |||
| 1f8a4c1022 | |||
| 1e422f20aa | |||
| 29eda28bf3 | |||
| f67f0cc66d | |||
| 721cafa0cd | |||
| c1d60054e9 | |||
| b95b3f68d3 | |||
| 81b6e27eb8 | |||
| d69678424b | |||
| a43c1aceec | |||
| f70cf8d81e | |||
| 83b6c79203 | |||
| 1192c038b2 | |||
| 4ebbf6553e | |||
| c501d63382 | |||
| 72d6d3f535 | |||
| ddd34dc9cc | |||
| 03b1c10d13 | |||
| 4cd5b8fd04 | |||
| f0ce17182b | |||
| 2a8a7d844b | |||
| ff33f426e5 | |||
| f691046c1f | |||
| 9fad8735b8 | |||
| c632055517 | |||
| fd850790d5 | |||
| 912d5d7f8c | |||
| d88a136ac3 | |||
| 172484cf08 | |||
| 821083639a | |||
| e4f0f3ec87 | |||
| cc6302f7b8 | |||
| c89fd82856 | |||
| 0e29a92d42 | |||
| 835d8ffe5d | |||
| 21ee2068a6 | |||
| 0ad149942b | |||
| 66305768c0 | |||
| 05f98fe993 | |||
| 89416f37af | |||
| 7285ddcb4e | |||
| 8993a4f707 | |||
| 633d7bd8a8 | |||
| 3944ea2055 | |||
| d85d0f5877 | |||
| d32a7986a5 | |||
| 71813425bd | |||
| da000b54ca | |||
| 74a9b42d9f | |||
| f9322ab3aa | |||
| 5becaca2c4 | |||
| 50a670fbc4 | |||
| 48f405a696 | |||
| bc56c4242e | |||
| 1b63256b9c | |||
| 7930b449b3 | |||
| e5cd42da55 | |||
| 2a54bbf901 | |||
| 2e134ed947 | |||
| ba727391db | |||
| d4346149fa | |||
| 2637fc5132 | |||
| ac5135470b | |||
| 613966aecf | |||
| 83ddcb9c39 | |||
| 957c2433cf | |||
| c10b367070 | |||
| 432416d09e | |||
| dd7d25dc10 | |||
| 24c60a0ef6 | |||
| f616c17bd2 | |||
| 5628200bd4 | |||
| ae93527a6f | |||
| 2939d5cadd | |||
| e2c7bc2d6d | |||
| f4bae78730 | |||
| d307898289 | |||
| 879ac3ccb1 | |||
| cd41e73cbe | |||
| 47f1ca646e | |||
| a18b18e530 | |||
| 4d1ffbb652 | |||
| 13423b137e | |||
| d60eea5e2f | |||
| 39c7d3b69f | |||
| 2de04f1374 | |||
| 5fb39ea316 | |||
| 55640ecad2 | |||
| 69d3867895 | |||
| 210f44f66f | |||
| b78e4ad6a1 | |||
| 4146566f92 | |||
| 4e46dfb068 | |||
| 13c96a80db | |||
| de77a33341 | |||
| 295bb74acf | |||
| 59abd2bd5b | |||
| ecbfbfb960 | |||
| 04e5804665 | |||
| 681d0d9538 | |||
| 8bfd9c0e62 | |||
| 95df9bc316 | |||
| d08576f672 | |||
| aa16bf4084 | |||
| 432632d981 | |||
| d6ade7694e | |||
| c9e282f236 | |||
| 5b902a1329 | |||
| fc7c932169 | |||
| 819b52687c | |||
| 28fff104a1 | |||
| 07b2b0de5a | |||
| 4287b7ac61 | |||
| 734331d5bc | |||
| 5de2bf7a83 | |||
| 1744921a0a | |||
| d4da64582c | |||
| d94acfeb17 | |||
| fcc14012da | |||
| cc8cbc89fd | |||
| 8582e40edf | |||
| 1e87ef12ee | |||
| 565200529f | |||
| 198c7f48ca | |||
| 8105e63b79 | |||
| 3932296fcf | |||
| cb0d9d3392 | |||
| 4b90eca21e | |||
| 365b396f9a | |||
| c526c61d5e | |||
| c4aff56f23 | |||
| d9e0ed1cc9 | |||
| e77cd6b2b2 | |||
| f04b174e67 | |||
| 0c1c641765 | |||
| d44f6bf20f | |||
| 1fa62cf417 | |||
| d8d2ddd9e7 | |||
| f3ff8369c3 | |||
| 99d1868827 | |||
| 31cefa5b3c | |||
| 2d5ac8238b | |||
| 248cc9d68b | |||
| 5f0a5b57f9 | |||
| 86367fca3f | |||
| 07be3c21bf | |||
| 3097ba6c66 | |||
| b4669a2a72 | |||
| e8848ca261 | |||
| 5c6902b459 | |||
| 9b772a70a1 | |||
| 6c12a3e1e0 | |||
| c6f0351e9c | |||
| 7e90389dab | |||
| 30ce25300f | |||
| 26caf51619 | |||
| 3ecb5dbce6 | |||
| 1d409d04f2 | |||
| 679414418e | |||
| b26370d508 | |||
| 72b30aa45f | |||
| d9561d5d22 | |||
| 3d0ab4684f | |||
| 29a071c98e | |||
| 0ac7064d80 | |||
| dcd55dbb8f | |||
| 441dc11963 | |||
| 21a8193510 | |||
| 3b9a3ff6be | |||
| c5f12f0a6c | |||
| 90565099bd | |||
| 2b2814723f | |||
| 42e54c42cf | |||
| f0c12bbf93 |
@@ -1,4 +1,16 @@
|
||||
# Ignore git files
|
||||
.git/
|
||||
.github/
|
||||
|
||||
# Ignore Dodckerfile
|
||||
Dockerfile
|
||||
|
||||
# Ignore hidden files
|
||||
.pre-commit-config.yaml
|
||||
.dockerignore
|
||||
.gitignore
|
||||
.pytest*
|
||||
.DS_Store
|
||||
|
||||
# Ignore output directories
|
||||
output/
|
||||
|
||||
@@ -0,0 +1 @@
|
||||
* @prowler-cloud/prowler-team
|
||||
@@ -0,0 +1,50 @@
|
||||
---
|
||||
name: Bug report
|
||||
about: Create a report to help us improve
|
||||
title: "[Bug]: "
|
||||
labels: bug, status/needs-triage
|
||||
assignees: ''
|
||||
|
||||
---
|
||||
|
||||
<!--
|
||||
Please use this template to create your bug report. By providing as much info as possible you help us understand the issue, reproduce it and resolve it for you quicker. Therefore, take a couple of extra minutes to make sure you have provided all info needed.
|
||||
|
||||
PROTIP: record your screen and attach it as a gif to showcase the issue.
|
||||
|
||||
- How to record and attach gif: https://bit.ly/2Mi8T6K
|
||||
-->
|
||||
|
||||
**What happened?**
|
||||
A clear and concise description of what the bug is or what is not working as expected
|
||||
|
||||
|
||||
**How to reproduce it**
|
||||
Steps to reproduce the behavior:
|
||||
1. What command are you running?
|
||||
2. Environment you have, like single account, multi-account, organizations, etc.
|
||||
3. See error
|
||||
|
||||
|
||||
**Expected behavior**
|
||||
A clear and concise description of what you expected to happen.
|
||||
|
||||
|
||||
**Screenshots or Logs**
|
||||
If applicable, add screenshots to help explain your problem.
|
||||
Also, you can add logs (anonymize them first!). Here a command that may help to share a log
|
||||
`bash -x ./prowler -options > debug.log 2>&1` then attach here `debug.log`
|
||||
|
||||
|
||||
**From where are you running Prowler?**
|
||||
Please, complete the following information:
|
||||
- Resource: [e.g. EC2 instance, Fargate task, Docker container manually, EKS, Cloud9, CodeBuild, workstation, etc.)
|
||||
- OS: [e.g. Amazon Linux 2, Mac, Alpine, Windows, etc. ]
|
||||
- AWS-CLI Version [`aws --version`]:
|
||||
- Prowler Version [`./prowler -V`]:
|
||||
- Shell and version:
|
||||
- Others:
|
||||
|
||||
|
||||
**Additional context**
|
||||
Add any other context about the problem here.
|
||||
@@ -0,0 +1,5 @@
|
||||
blank_issues_enabled: false
|
||||
contact_links:
|
||||
- name: Questions & Help
|
||||
url: https://github.com/prowler-cloud/prowler/discussions/categories/q-a
|
||||
about: Please ask and answer questions here.
|
||||
@@ -0,0 +1,20 @@
|
||||
---
|
||||
name: Feature request
|
||||
about: Suggest an idea for this project
|
||||
title: ''
|
||||
labels: enhancement, status/needs-triage
|
||||
assignees: ''
|
||||
|
||||
---
|
||||
|
||||
**Is your feature request related to a problem? Please describe.**
|
||||
A clear and concise description of what the problem is. Ex. I'm always frustrated when [...]
|
||||
|
||||
**Describe the solution you'd like**
|
||||
A clear and concise description of what you want to happen.
|
||||
|
||||
**Describe alternatives you've considered**
|
||||
A clear and concise description of any alternative solutions or features you've considered.
|
||||
|
||||
**Additional context**
|
||||
Add any other context or screenshots about the feature request here.
|
||||
@@ -1 +1,13 @@
|
||||
### Context
|
||||
|
||||
Please include relevant motivation and context for this PR.
|
||||
|
||||
|
||||
### Description
|
||||
|
||||
Please include a summary of the change and which issue is fixed. List any dependencies that are required for this change.
|
||||
|
||||
|
||||
### License
|
||||
|
||||
By submitting this pull request, I confirm that my contribution is made under the terms of the Apache 2.0 license.
|
||||
|
||||
@@ -0,0 +1,209 @@
|
||||
name: build-lint-push-containers
|
||||
|
||||
on:
|
||||
push:
|
||||
branches:
|
||||
- 'master'
|
||||
paths-ignore:
|
||||
- '.github/**'
|
||||
- 'README.md'
|
||||
|
||||
release:
|
||||
types: [published, edited]
|
||||
|
||||
env:
|
||||
AWS_REGION_STG: eu-west-1
|
||||
AWS_REGION_PLATFORM: eu-west-1
|
||||
AWS_REGION_PRO: us-east-1
|
||||
IMAGE_NAME: prowler
|
||||
LATEST_TAG: latest
|
||||
STABLE_TAG: stable
|
||||
TEMPORARY_TAG: temporary
|
||||
DOCKERFILE_PATH: ./Dockerfile
|
||||
|
||||
jobs:
|
||||
# Lint Dockerfile using Hadolint
|
||||
# dockerfile-linter:
|
||||
# runs-on: ubuntu-latest
|
||||
# steps:
|
||||
# -
|
||||
# name: Checkout
|
||||
# uses: actions/checkout@v3
|
||||
# -
|
||||
# name: Install Hadolint
|
||||
# run: |
|
||||
# VERSION=$(curl --silent "https://api.github.com/repos/hadolint/hadolint/releases/latest" | \
|
||||
# grep '"tag_name":' | \
|
||||
# sed -E 's/.*"v([^"]+)".*/\1/' \
|
||||
# ) && curl -L -o /tmp/hadolint https://github.com/hadolint/hadolint/releases/download/v${VERSION}/hadolint-Linux-x86_64 \
|
||||
# && chmod +x /tmp/hadolint
|
||||
# -
|
||||
# name: Run Hadolint
|
||||
# run: |
|
||||
# /tmp/hadolint util/Dockerfile
|
||||
|
||||
# Build Prowler OSS container
|
||||
container-build:
|
||||
# needs: dockerfile-linter
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
-
|
||||
name: Checkout
|
||||
uses: actions/checkout@v3
|
||||
-
|
||||
name: Set up Docker Buildx
|
||||
uses: docker/setup-buildx-action@v2
|
||||
-
|
||||
name: Build
|
||||
uses: docker/build-push-action@v2
|
||||
with:
|
||||
# Without pushing to registries
|
||||
push: false
|
||||
tags: ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }}
|
||||
file: ${{ env.DOCKERFILE_PATH }}
|
||||
outputs: type=docker,dest=/tmp/${{ env.IMAGE_NAME }}.tar
|
||||
-
|
||||
name: Share image between jobs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: ${{ env.IMAGE_NAME }}.tar
|
||||
path: /tmp/${{ env.IMAGE_NAME }}.tar
|
||||
|
||||
# Lint Prowler OSS container using Dockle
|
||||
# container-linter:
|
||||
# needs: container-build
|
||||
# runs-on: ubuntu-latest
|
||||
# steps:
|
||||
# -
|
||||
# name: Get container image from shared
|
||||
# uses: actions/download-artifact@v2
|
||||
# with:
|
||||
# name: ${{ env.IMAGE_NAME }}.tar
|
||||
# path: /tmp
|
||||
# -
|
||||
# name: Load Docker image
|
||||
# run: |
|
||||
# docker load --input /tmp/${{ env.IMAGE_NAME }}.tar
|
||||
# docker image ls -a
|
||||
# -
|
||||
# name: Install Dockle
|
||||
# run: |
|
||||
# VERSION=$(curl --silent "https://api.github.com/repos/goodwithtech/dockle/releases/latest" | \
|
||||
# grep '"tag_name":' | \
|
||||
# sed -E 's/.*"v([^"]+)".*/\1/' \
|
||||
# ) && curl -L -o dockle.deb https://github.com/goodwithtech/dockle/releases/download/v${VERSION}/dockle_${VERSION}_Linux-64bit.deb \
|
||||
# && sudo dpkg -i dockle.deb && rm dockle.deb
|
||||
# -
|
||||
# name: Run Dockle
|
||||
# run: dockle ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }}
|
||||
|
||||
# Push Prowler OSS container to registries
|
||||
container-push:
|
||||
# needs: container-linter
|
||||
needs: container-build
|
||||
runs-on: ubuntu-latest
|
||||
permissions:
|
||||
id-token: write
|
||||
contents: read # This is required for actions/checkout
|
||||
steps:
|
||||
-
|
||||
name: Get container image from shared
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: ${{ env.IMAGE_NAME }}.tar
|
||||
path: /tmp
|
||||
-
|
||||
name: Load Docker image
|
||||
run: |
|
||||
docker load --input /tmp/${{ env.IMAGE_NAME }}.tar
|
||||
docker image ls -a
|
||||
-
|
||||
name: Login to DockerHub
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
username: ${{ secrets.DOCKERHUB_USERNAME }}
|
||||
password: ${{ secrets.DOCKERHUB_TOKEN }}
|
||||
-
|
||||
name: Login to Public ECR
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
registry: public.ecr.aws
|
||||
username: ${{ secrets.PUBLIC_ECR_AWS_ACCESS_KEY_ID }}
|
||||
password: ${{ secrets.PUBLIC_ECR_AWS_SECRET_ACCESS_KEY }}
|
||||
env:
|
||||
AWS_REGION: ${{ env.AWS_REGION_PRO }}
|
||||
-
|
||||
name: Configure AWS Credentials -- STG
|
||||
if: github.event_name == 'push'
|
||||
uses: aws-actions/configure-aws-credentials@v1
|
||||
with:
|
||||
aws-region: ${{ env.AWS_REGION_STG }}
|
||||
role-to-assume: ${{ secrets.STG_IAM_ROLE_ARN }}
|
||||
role-session-name: build-lint-containers-stg
|
||||
-
|
||||
name: Login to ECR -- STG
|
||||
if: github.event_name == 'push'
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
registry: ${{ secrets.STG_ECR }}
|
||||
-
|
||||
name: Configure AWS Credentials -- PLATFORM
|
||||
if: github.event_name == 'release'
|
||||
uses: aws-actions/configure-aws-credentials@v1
|
||||
with:
|
||||
aws-region: ${{ env.AWS_REGION_PLATFORM }}
|
||||
role-to-assume: ${{ secrets.STG_IAM_ROLE_ARN }}
|
||||
role-session-name: build-lint-containers-pro
|
||||
-
|
||||
name: Login to ECR -- PLATFORM
|
||||
if: github.event_name == 'release'
|
||||
uses: docker/login-action@v2
|
||||
with:
|
||||
registry: ${{ secrets.PLATFORM_ECR }}
|
||||
-
|
||||
# Push to master branch - push "latest" tag
|
||||
name: Tag (latest)
|
||||
if: github.event_name == 'push'
|
||||
run: |
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ env.LATEST_TAG }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.LATEST_TAG }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.LATEST_TAG }}
|
||||
-
|
||||
# Push to master branch - push "latest" tag
|
||||
name: Push (latest)
|
||||
if: github.event_name == 'push'
|
||||
run: |
|
||||
docker push ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ env.LATEST_TAG }}
|
||||
docker push ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.LATEST_TAG }}
|
||||
docker push ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.LATEST_TAG }}
|
||||
-
|
||||
# Tag the new release (stable and release tag)
|
||||
name: Tag (release)
|
||||
if: github.event_name == 'release'
|
||||
run: |
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ github.event.release.tag_name }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ github.event.release.tag_name }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ github.event.release.tag_name }}
|
||||
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ env.STABLE_TAG }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.STABLE_TAG }}
|
||||
docker tag ${{ env.IMAGE_NAME }}:${{ env.TEMPORARY_TAG }} ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.STABLE_TAG }}
|
||||
|
||||
-
|
||||
# Push the new release (stable and release tag)
|
||||
name: Push (release)
|
||||
if: github.event_name == 'release'
|
||||
run: |
|
||||
docker push ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ github.event.release.tag_name }}
|
||||
docker push ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ github.event.release.tag_name }}
|
||||
docker push ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ github.event.release.tag_name }}
|
||||
|
||||
docker push ${{ secrets.PLATFORM_ECR }}/${{ secrets.PLATFORM_ECR_REPOSITORY }}:${{ env.STABLE_TAG }}
|
||||
docker push ${{ secrets.DOCKER_HUB_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.STABLE_TAG }}
|
||||
docker push ${{ secrets.PUBLIC_ECR_REPOSITORY }}/${{ env.IMAGE_NAME }}:${{ env.STABLE_TAG }}
|
||||
-
|
||||
name: Delete artifacts
|
||||
if: always()
|
||||
uses: geekyeggo/delete-artifact@v1
|
||||
with:
|
||||
name: ${{ env.IMAGE_NAME }}.tar
|
||||
@@ -0,0 +1,18 @@
|
||||
name: find-secrets
|
||||
|
||||
on: pull_request
|
||||
|
||||
jobs:
|
||||
trufflehog:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@v3
|
||||
with:
|
||||
fetch-depth: 0
|
||||
- name: TruffleHog OSS
|
||||
uses: trufflesecurity/trufflehog@v3.13.0
|
||||
with:
|
||||
path: ./
|
||||
base: ${{ github.event.repository.default_branch }}
|
||||
head: HEAD
|
||||
@@ -0,0 +1,41 @@
|
||||
name: Lint & Test
|
||||
|
||||
on:
|
||||
push:
|
||||
branches:
|
||||
- 'prowler-3.0-dev'
|
||||
pull_request:
|
||||
branches:
|
||||
- 'prowler-3.0-dev'
|
||||
|
||||
jobs:
|
||||
build:
|
||||
|
||||
runs-on: ubuntu-latest
|
||||
strategy:
|
||||
matrix:
|
||||
python-version: ["3.9"]
|
||||
|
||||
steps:
|
||||
- uses: actions/checkout@v3
|
||||
- name: Set up Python ${{ matrix.python-version }}
|
||||
uses: actions/setup-python@v4
|
||||
with:
|
||||
python-version: ${{ matrix.python-version }}
|
||||
- name: Install dependencies
|
||||
run: |
|
||||
python -m pip install --upgrade pip
|
||||
pip install pipenv
|
||||
pipenv install
|
||||
- name: Bandit
|
||||
run: |
|
||||
pipenv run bandit -q -lll -x '*_test.py,./contrib/' -r .
|
||||
- name: Safety
|
||||
run: |
|
||||
pipenv run safety check
|
||||
- name: Vulture
|
||||
run: |
|
||||
pipenv run vulture --exclude "contrib" --min-confidence 100 .
|
||||
- name: Test with pytest
|
||||
run: |
|
||||
pipenv run pytest -n auto
|
||||
@@ -0,0 +1,50 @@
|
||||
# This is a basic workflow to help you get started with Actions
|
||||
|
||||
name: Refresh regions of AWS services
|
||||
|
||||
on:
|
||||
schedule:
|
||||
- cron: "0 9 * * *" #runs at 09:00 UTC everyday
|
||||
|
||||
env:
|
||||
GITHUB_BRANCH: "prowler-3.0-dev"
|
||||
|
||||
# A workflow run is made up of one or more jobs that can run sequentially or in parallel
|
||||
jobs:
|
||||
# This workflow contains a single job called "build"
|
||||
build:
|
||||
# The type of runner that the job will run on
|
||||
runs-on: ubuntu-latest
|
||||
# Steps represent a sequence of tasks that will be executed as part of the job
|
||||
steps:
|
||||
# Checks-out your repository under $GITHUB_WORKSPACE, so your job can access it
|
||||
- uses: actions/checkout@v3
|
||||
with:
|
||||
ref: ${{ env.GITHUB_BRANCH }}
|
||||
|
||||
- name: setup python
|
||||
uses: actions/setup-python@v2
|
||||
with:
|
||||
python-version: 3.9 #install the python needed
|
||||
|
||||
# Runs a single command using the runners shell
|
||||
- name: Run a one-line script
|
||||
run: python3 util/update_aws_services_regions.py
|
||||
|
||||
# Create pull request
|
||||
- name: Create Pull Request
|
||||
uses: peter-evans/create-pull-request@v4
|
||||
with:
|
||||
token: ${{ secrets.GITHUB_TOKEN }}
|
||||
commit-message: "feat(regions_update): Update regions for AWS services."
|
||||
branch: "aws-services-regions-updated"
|
||||
labels: "status/waiting-for-revision, severity/low"
|
||||
title: "feat(regions_update): Changes in regions for AWS services."
|
||||
body: |
|
||||
### Description
|
||||
|
||||
This PR updates the regions for AWS services.
|
||||
|
||||
### License
|
||||
|
||||
By submitting this pull request, I confirm that my contribution is made under the terms of the Apache 2.0 license.
|
||||
@@ -0,0 +1,29 @@
|
||||
repos:
|
||||
- repo: https://github.com/pre-commit/pre-commit-hooks
|
||||
rev: v3.3.0
|
||||
hooks:
|
||||
- id: check-merge-conflict
|
||||
- id: check-yaml
|
||||
args: ['--unsafe']
|
||||
- id: check-json
|
||||
- id: end-of-file-fixer
|
||||
- id: trailing-whitespace
|
||||
exclude: 'README.md'
|
||||
- id: no-commit-to-branch
|
||||
- id: pretty-format-json
|
||||
args: ['--autofix']
|
||||
|
||||
- repo: https://github.com/koalaman/shellcheck-precommit
|
||||
rev: v0.8.0
|
||||
hooks:
|
||||
- id: shellcheck
|
||||
|
||||
- repo: https://github.com/hadolint/hadolint
|
||||
rev: v2.10.0
|
||||
hooks:
|
||||
- id: hadolint
|
||||
name: Lint Dockerfiles
|
||||
description: Runs hadolint to lint Dockerfiles
|
||||
language: system
|
||||
types: ["dockerfile"]
|
||||
entry: hadolint
|
||||
+64
@@ -0,0 +1,64 @@
|
||||
# Build command
|
||||
# docker build --platform=linux/amd64 --no-cache -t prowler:latest -f ./Dockerfile .
|
||||
|
||||
# hadolint ignore=DL3007
|
||||
FROM public.ecr.aws/amazonlinux/amazonlinux:latest
|
||||
|
||||
LABEL maintainer="https://github.com/prowler-cloud/prowler"
|
||||
|
||||
ARG USERNAME=prowler
|
||||
ARG USERID=34000
|
||||
|
||||
# Prepare image as root
|
||||
USER 0
|
||||
# System dependencies
|
||||
# hadolint ignore=DL3006,DL3013,DL3033
|
||||
RUN yum upgrade -y && \
|
||||
yum install -y python3 bash curl jq coreutils py3-pip which unzip shadow-utils && \
|
||||
yum clean all && \
|
||||
rm -rf /var/cache/yum
|
||||
|
||||
RUN amazon-linux-extras install -y epel postgresql14 && \
|
||||
yum clean all && \
|
||||
rm -rf /var/cache/yum
|
||||
|
||||
# Create non-root user
|
||||
RUN useradd -l -s /bin/bash -U -u ${USERID} ${USERNAME}
|
||||
|
||||
USER ${USERNAME}
|
||||
|
||||
# Python dependencies
|
||||
# hadolint ignore=DL3006,DL3013,DL3042
|
||||
RUN pip3 install --upgrade pip && \
|
||||
pip3 install --no-cache-dir boto3 detect-secrets==1.0.3 && \
|
||||
pip3 cache purge
|
||||
# Set Python PATH
|
||||
ENV PATH="/home/${USERNAME}/.local/bin:${PATH}"
|
||||
|
||||
USER 0
|
||||
|
||||
# Install AWS CLI
|
||||
RUN curl https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip -o awscliv2.zip && \
|
||||
unzip -q awscliv2.zip && \
|
||||
aws/install && \
|
||||
rm -rf aws awscliv2.zip
|
||||
|
||||
# Keep Python2 for yum
|
||||
RUN sed -i '1 s/python/python2.7/' /usr/bin/yum
|
||||
|
||||
# Set Python3
|
||||
RUN rm /usr/bin/python && \
|
||||
ln -s /usr/bin/python3 /usr/bin/python
|
||||
|
||||
# Set working directory
|
||||
WORKDIR /prowler
|
||||
|
||||
# Copy all files
|
||||
COPY . ./
|
||||
|
||||
# Set files ownership
|
||||
RUN chown -R prowler .
|
||||
|
||||
USER ${USERNAME}
|
||||
|
||||
ENTRYPOINT ["./prowler"]
|
||||
@@ -1,17 +1,38 @@
|
||||
<p align="center">
|
||||
<img align="center" src="docs/images/prowler-pro-dark.png#gh-dark-mode-only" width="150" height="36">
|
||||
<img align="center" src="docs/images/prowler-pro-light.png#gh-light-mode-only" width="15%" height="15%">
|
||||
</p>
|
||||
<p align="center">
|
||||
<b><i>    See all the things you and your team can do with ProwlerPro at <a href="https://prowler.pro">prowler.pro</a></i></b>
|
||||
</p>
|
||||
<hr>
|
||||
<p align="center">
|
||||
<img src="https://user-images.githubusercontent.com/3985464/113734260-7ba06900-96fb-11eb-82bc-d4f68a1e2710.png" />
|
||||
</p>
|
||||
<p align="center">
|
||||
<a href="https://join.slack.com/t/prowler-workspace/shared_invite/zt-1hix76xsl-2uq222JIXrC7Q8It~9ZNog"><img alt="Slack Shield" src="https://img.shields.io/badge/slack-prowler-brightgreen.svg?logo=slack"></a>
|
||||
<a href="https://hub.docker.com/r/toniblyx/prowler"><img alt="Docker Pulls" src="https://img.shields.io/docker/pulls/toniblyx/prowler"></a>
|
||||
<a href="https://hub.docker.com/r/toniblyx/prowler"><img alt="Docker" src="https://img.shields.io/docker/cloud/build/toniblyx/prowler"></a>
|
||||
<a href="https://hub.docker.com/r/toniblyx/prowler"><img alt="Docker" src="https://img.shields.io/docker/image-size/toniblyx/prowler"></a>
|
||||
<a href="https://gallery.ecr.aws/o4g1s5r6/prowler"><img width="120" height=19" alt="AWS ECR Gallery" src="https://user-images.githubusercontent.com/3985464/151531396-b6535a68-c907-44eb-95a1-a09508178616.png"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler"><img alt="Repo size" src="https://img.shields.io/github/repo-size/prowler-cloud/prowler"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler"><img alt="Lines" src="https://img.shields.io/tokei/lines/github/prowler-cloud/prowler"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler/issues"><img alt="Issues" src="https://img.shields.io/github/issues/prowler-cloud/prowler"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler/releases"><img alt="Version" src="https://img.shields.io/github/v/release/prowler-cloud/prowler?include_prereleases"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler/releases"><img alt="Version" src="https://img.shields.io/github/release-date/prowler-cloud/prowler"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler"><img alt="Contributors" src="https://img.shields.io/github/contributors-anon/prowler-cloud/prowler"></a>
|
||||
<a href="https://github.com/prowler-cloud/prowler"><img alt="License" src="https://img.shields.io/github/license/prowler-cloud/prowler"></a>
|
||||
<a href="https://twitter.com/ToniBlyx"><img alt="Twitter" src="https://img.shields.io/twitter/follow/toniblyx?style=social"></a>
|
||||
</p>
|
||||
|
||||
# Prowler - AWS Security Tool
|
||||
<p align="center">
|
||||
<i>Prowler</i> is an Open Source security tool to perform AWS security best practices assessments, audits, incident response, continuous monitoring, hardening and forensics readiness. It contains more than 240 controls covering CIS, PCI-DSS, ISO27001, GDPR, HIPAA, FFIEC, SOC2, AWS FTR, ENS and custom security frameworks.
|
||||
</p>
|
||||
|
||||
[](https://discord.gg/UjSMCVnxSB)
|
||||
[](https://hub.docker.com/r/toniblyx/prowler)
|
||||
[](https://gallery.ecr.aws/o4g1s5r6/prowler)
|
||||
|
||||
|
||||
## Table of Contents
|
||||
|
||||
- [Description](#description)
|
||||
- [Prowler Container Versions](#prowler-container-versions)
|
||||
- [Features](#features)
|
||||
- [High level architecture](#high-level-architecture)
|
||||
- [Requirements and Installation](#requirements-and-installation)
|
||||
@@ -20,7 +41,8 @@
|
||||
- [Advanced Usage](#advanced-usage)
|
||||
- [Security Hub integration](#security-hub-integration)
|
||||
- [CodeBuild deployment](#codebuild-deployment)
|
||||
- [Whitelist/allowlist or remove FAIL from resources](#whitelist-or-allowlist-or-remove-a-fail-from-resources)
|
||||
- [Allowlist](#allowlist-or-remove-a-fail-from-resources)
|
||||
- [Inventory](#inventory)
|
||||
- [Fix](#how-to-fix-every-fail)
|
||||
- [Troubleshooting](#troubleshooting)
|
||||
- [Extras](#extras)
|
||||
@@ -29,7 +51,7 @@
|
||||
- [HIPAA Checks](#hipaa-checks)
|
||||
- [Trust Boundaries Checks](#trust-boundaries-checks)
|
||||
- [Multi Account and Continuous Monitoring](util/org-multi-account/README.md)
|
||||
- [Add Custom Checks](#add-custom-checks)
|
||||
- [Custom Checks](#custom-checks)
|
||||
- [Third Party Integrations](#third-party-integrations)
|
||||
- [Full list of checks and groups](/LIST_OF_CHECKS_AND_GROUPS.md)
|
||||
- [License](#license)
|
||||
@@ -38,21 +60,32 @@
|
||||
|
||||
Prowler is a command line tool that helps you with AWS security assessment, auditing, hardening and incident response.
|
||||
|
||||
It follows guidelines of the CIS Amazon Web Services Foundations Benchmark (49 checks) and has more than 100 additional checks including related to GDPR, HIPAA, PCI-DSS, ISO-27001, FFIEC, SOC2 and others.
|
||||
It follows guidelines of the CIS Amazon Web Services Foundations Benchmark (49 checks) and has more than 190 additional checks including related to GDPR, HIPAA, PCI-DSS, ISO-27001, FFIEC, SOC2 and others.
|
||||
|
||||
Read more about [CIS Amazon Web Services Foundations Benchmark v1.2.0 - 05-23-2018](https://d0.awsstatic.com/whitepapers/compliance/AWS_CIS_Foundations_Benchmark.pdf)
|
||||
|
||||
## Prowler container versions
|
||||
|
||||
The available versions of Prowler are the following:
|
||||
- latest: in sync with master branch (bear in mind that it is not a stable version)
|
||||
- <x.y.z> (release): you can find the releases [here](https://github.com/prowler-cloud/prowler/releases), those are stable releases.
|
||||
- stable: this tag always point to the latest release.
|
||||
|
||||
The container images are available here:
|
||||
- [DockerHub](https://hub.docker.com/r/toniblyx/prowler/tags)
|
||||
- [AWS Public ECR](https://gallery.ecr.aws/o4g1s5r6/prowler)
|
||||
|
||||
## Features
|
||||
|
||||
+200 checks covering security best practices across all AWS regions and most of AWS services and related to the next groups:
|
||||
+240 checks covering security best practices across all AWS regions and most of AWS services and related to the next groups:
|
||||
|
||||
- Identity and Access Management [group1]
|
||||
- Logging [group2]
|
||||
- Logging [group2]
|
||||
- Monitoring [group3]
|
||||
- Networking [group4]
|
||||
- CIS Level 1 [cislevel1]
|
||||
- CIS Level 2 [cislevel2]
|
||||
- Extras *see Extras section* [extras]
|
||||
- Extras _see Extras section_ [extras]
|
||||
- Forensics related group of checks [forensics-ready]
|
||||
- GDPR [gdpr] Read more [here](#gdpr-checks)
|
||||
- HIPAA [hipaa] Read more [here](#hipaa-checks)
|
||||
@@ -66,10 +99,11 @@ Read more about [CIS Amazon Web Services Foundations Benchmark v1.2.0 - 05-23-20
|
||||
With Prowler you can:
|
||||
|
||||
- Get a direct colorful or monochrome report
|
||||
- A HTML, CSV, JUNIT, JSON or JSON ASFF format report
|
||||
- Send findings directly to Security Hub
|
||||
- A HTML, CSV, JUNIT, JSON or JSON ASFF (Security Hub) format report
|
||||
- Send findings directly to the Security Hub
|
||||
- Run specific checks and groups or create your own
|
||||
- Check multiple AWS accounts in parallel or sequentially
|
||||
- Get an inventory of your AWS resources
|
||||
- And more! Read examples below
|
||||
|
||||
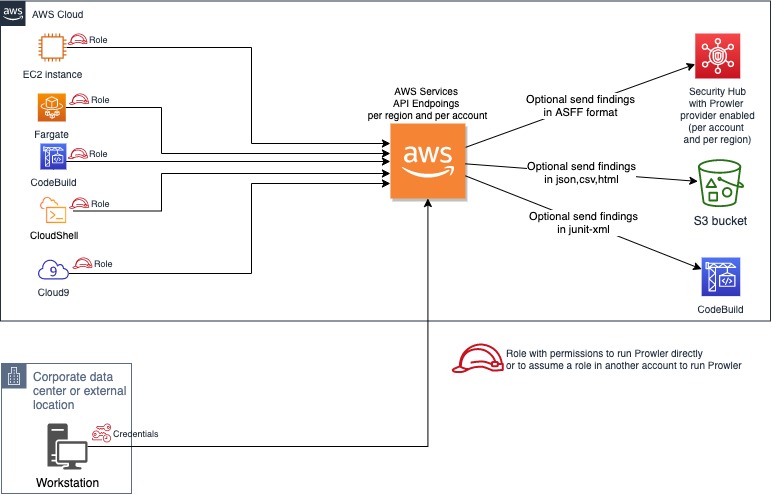
## High level architecture
|
||||
@@ -77,134 +111,151 @@ With Prowler you can:
|
||||
You can run Prowler from your workstation, an EC2 instance, Fargate or any other container, Codebuild, CloudShell and Cloud9.
|
||||
|
||||
|
||||
|
||||
## Requirements and Installation
|
||||
|
||||
Prowler has been written in bash using AWS-CLI and it works in Linux and OSX.
|
||||
Prowler has been written in bash using AWS-CLI underneath and it works in Linux, Mac OS or Windows with cygwin or virtualization. Also requires `jq` and `detect-secrets` to work properly.
|
||||
|
||||
- Make sure the latest version of AWS-CLI is installed on your workstation (it works with either v1 or v2), and other components needed, with Python pip already installed:
|
||||
- Make sure the latest version of AWS-CLI is installed. It works with either v1 or v2, however _latest v2 is recommended if using new regions since they require STS v2 token_, and other components needed, with Python pip already installed.
|
||||
|
||||
```sh
|
||||
pip install awscli
|
||||
```
|
||||
- For Amazon Linux (`yum` based Linux distributions and AWS CLI v2):
|
||||
```
|
||||
sudo yum update -y
|
||||
sudo yum remove -y awscli
|
||||
curl "https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"
|
||||
unzip awscliv2.zip
|
||||
sudo ./aws/install
|
||||
sudo yum install -y python3 jq git
|
||||
sudo pip3 install detect-secrets==1.0.3
|
||||
git clone https://github.com/prowler-cloud/prowler
|
||||
```
|
||||
- For Ubuntu Linux (`apt` based Linux distributions and AWS CLI v2):
|
||||
|
||||
> NOTE: detect-secrets Yelp version is no longer supported the one from IBM is mantained now. Use the one mentioned below or the specific Yelp version 1.0.3 to make sure it works as expected (`pip install detect-secrets==1.0.3`):
|
||||
```sh
|
||||
pip install "git+https://github.com/ibm/detect-secrets.git@master#egg=detect-secrets"
|
||||
```
|
||||
```
|
||||
sudo apt update
|
||||
sudo apt install python3 python3-pip jq git zip
|
||||
pip install detect-secrets==1.0.3
|
||||
curl "https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"
|
||||
unzip awscliv2.zip
|
||||
sudo ./aws/install
|
||||
git clone https://github.com/prowler-cloud/prowler
|
||||
```
|
||||
|
||||
AWS-CLI can be also installed it using "brew", "apt", "yum" or manually from <https://aws.amazon.com/cli/>, but `detect-secrets` has to be installed using `pip` or `pip3`. You will need to install `jq` to get the most from Prowler.
|
||||
> NOTE: detect-secrets Yelp version is no longer supported, the one from IBM is mantained now. Use the one mentioned below or the specific Yelp version 1.0.3 to make sure it works as expected (`pip install detect-secrets==1.0.3`):
|
||||
|
||||
- Make sure jq is installed: examples below with "apt" for Debian alike and "yum" for RedHat alike distros (like Amazon Linux):
|
||||
```sh
|
||||
pip install "git+https://github.com/ibm/detect-secrets.git@master#egg=detect-secrets"
|
||||
```
|
||||
|
||||
```sh
|
||||
sudo apt install jq
|
||||
```
|
||||
AWS-CLI can be also installed it using other methods, refer to official documentation for more details: <https://aws.amazon.com/cli/>, but `detect-secrets` has to be installed using `pip` or `pip3`.
|
||||
|
||||
```sh
|
||||
sudo yum install jq
|
||||
```
|
||||
- Once Prowler repository is cloned, get into the folder and you can run it:
|
||||
|
||||
- Previous steps, from your workstation:
|
||||
```sh
|
||||
cd prowler
|
||||
./prowler
|
||||
```
|
||||
|
||||
```sh
|
||||
git clone https://github.com/toniblyx/prowler
|
||||
cd prowler
|
||||
```
|
||||
- Since Prowler users AWS CLI under the hood, you can follow any authentication method as described [here](https://docs.aws.amazon.com/cli/latest/userguide/cli-configure-quickstart.html#cli-configure-quickstart-precedence). Make sure you have properly configured your AWS-CLI with a valid Access Key and Region or declare AWS variables properly (or instance profile/role):
|
||||
|
||||
- Since Prowler users AWS CLI under the hood, you can follow any authentication method as described [here](https://docs.aws.amazon.com/cli/latest/userguide/cli-configure-quickstart.html#cli-configure-quickstart-precedence). Make sure you have properly configured your AWS-CLI with a valid Access Key and Region or declare AWS variables properly (or intance profile):
|
||||
```sh
|
||||
aws configure
|
||||
```
|
||||
|
||||
```sh
|
||||
aws configure
|
||||
```
|
||||
or
|
||||
|
||||
or
|
||||
```sh
|
||||
export AWS_ACCESS_KEY_ID="ASXXXXXXX"
|
||||
export AWS_SECRET_ACCESS_KEY="XXXXXXXXX"
|
||||
export AWS_SESSION_TOKEN="XXXXXXXXX"
|
||||
```
|
||||
|
||||
```sh
|
||||
export AWS_ACCESS_KEY_ID="ASXXXXXXX"
|
||||
export AWS_SECRET_ACCESS_KEY="XXXXXXXXX"
|
||||
export AWS_SESSION_TOKEN="XXXXXXXXX"
|
||||
```
|
||||
- Those credentials must be associated to a user or role with proper permissions to do all checks. To make sure, add the AWS managed policies, SecurityAudit and ViewOnlyAccess, to the user or role being used. Policy ARNs are:
|
||||
|
||||
- Those credentials must be associated to a user or role with proper permissions to do all checks. To make sure, add the AWS managed policies, SecurityAudit and ViewOnlyAccess, to the user or role being used. Policy ARNs are:
|
||||
```sh
|
||||
arn:aws:iam::aws:policy/SecurityAudit
|
||||
arn:aws:iam::aws:policy/job-function/ViewOnlyAccess
|
||||
```
|
||||
|
||||
```sh
|
||||
arn:aws:iam::aws:policy/SecurityAudit
|
||||
arn:aws:iam::aws:policy/job-function/ViewOnlyAccess
|
||||
```
|
||||
|
||||
> Additional permissions needed: to make sure Prowler can scan all services included in the group *Extras*, make sure you attach also the custom policy [prowler-additions-policy.json](https://github.com/toniblyx/prowler/blob/master/iam/prowler-additions-policy.json) to the role you are using. If you want Prowler to send findings to [AWS Security Hub](https://aws.amazon.com/security-hub), make sure you also attach the custom policy [prowler-security-hub.json](https://github.com/toniblyx/prowler/blob/master/iam/prowler-security-hub.json).
|
||||
> Additional permissions needed: to make sure Prowler can scan all services included in the group _Extras_, make sure you attach also the custom policy [prowler-additions-policy.json](https://github.com/prowler-cloud/prowler/blob/master/iam/prowler-additions-policy.json) to the role you are using. If you want Prowler to send findings to [AWS Security Hub](https://aws.amazon.com/security-hub), make sure you also attach the custom policy [prowler-security-hub.json](https://github.com/prowler-cloud/prowler/blob/master/iam/prowler-security-hub.json).
|
||||
|
||||
## Usage
|
||||
|
||||
1. Run the `prowler` command without options (it will use your environment variable credentials if they exist or will default to using the `~/.aws/credentials` file and run checks over all regions when needed. The default region is us-east-1):
|
||||
|
||||
```sh
|
||||
./prowler
|
||||
```
|
||||
```sh
|
||||
./prowler
|
||||
```
|
||||
|
||||
Use `-l` to list all available checks and the groups (sections) that reference them. To list all groups use `-L` and to list content of a group use `-l -g <groupname>`.
|
||||
Use `-l` to list all available checks and the groups (sections) that reference them. To list all groups use `-L` and to list content of a group use `-l -g <groupname>`.
|
||||
|
||||
If you want to avoid installing dependencies run it using Docker:
|
||||
If you want to avoid installing dependencies run it using Docker:
|
||||
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest
|
||||
```
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest
|
||||
```
|
||||
|
||||
In case you want to get reports created by Prowler use docker volume option like in the example below:
|
||||
|
||||
```sh
|
||||
docker run -ti --rm -v /your/local/output:/prowler/output --name prowler --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest -g hipaa -M csv,json,html
|
||||
```
|
||||
|
||||
1. For custom AWS-CLI profile and region, use the following: (it will use your custom profile and run checks over all regions when needed):
|
||||
|
||||
```sh
|
||||
./prowler -p custom-profile -r us-east-1
|
||||
```
|
||||
```sh
|
||||
./prowler -p custom-profile -r us-east-1
|
||||
```
|
||||
|
||||
1. For a single check use option `-c`:
|
||||
|
||||
```sh
|
||||
./prowler -c check310
|
||||
```
|
||||
```sh
|
||||
./prowler -c check310
|
||||
```
|
||||
|
||||
With Docker:
|
||||
With Docker:
|
||||
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest "-c check310"
|
||||
```
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest "-c check310"
|
||||
```
|
||||
|
||||
or multiple checks separated by comma:
|
||||
or multiple checks separated by comma:
|
||||
|
||||
```sh
|
||||
./prowler -c check310,check722
|
||||
```
|
||||
```sh
|
||||
./prowler -c check310,check722
|
||||
```
|
||||
|
||||
or all checks but some of them:
|
||||
or all checks but some of them:
|
||||
|
||||
```sh
|
||||
./prowler -E check42,check43
|
||||
```
|
||||
```sh
|
||||
./prowler -E check42,check43
|
||||
```
|
||||
|
||||
or for custom profile and region:
|
||||
or for custom profile and region:
|
||||
|
||||
```sh
|
||||
./prowler -p custom-profile -r us-east-1 -c check11
|
||||
```
|
||||
```sh
|
||||
./prowler -p custom-profile -r us-east-1 -c check11
|
||||
```
|
||||
|
||||
or for a group of checks use group name:
|
||||
or for a group of checks use group name:
|
||||
|
||||
```sh
|
||||
./prowler -g group1 # for iam related checks
|
||||
```
|
||||
```sh
|
||||
./prowler -g group1 # for iam related checks
|
||||
```
|
||||
|
||||
or exclude some checks in the group:
|
||||
or exclude some checks in the group:
|
||||
|
||||
```sh
|
||||
./prowler -g group4 -E check42,check43
|
||||
```
|
||||
```sh
|
||||
./prowler -g group4 -E check42,check43
|
||||
```
|
||||
|
||||
Valid check numbers are based on the AWS CIS Benchmark guide, so 1.1 is check11 and 3.10 is check310
|
||||
Valid check numbers are based on the AWS CIS Benchmark guide, so 1.1 is check11 and 3.10 is check310
|
||||
|
||||
### Regions
|
||||
|
||||
By default, Prowler scans all opt-in regions available, that might take a long execution time depending on the number of resources and regions used. Same applies for GovCloud or China regions. See below Advance usage for examples.
|
||||
|
||||
Prowler has two parameters related to regions: `-r` that is used query AWS services API endpoints (it uses `us-east-1` by default and required for GovCloud or China) and the option `-f` that is to filter those regions you only want to scan. For example if you want to scan Dublin only use `-f eu-west-1` and if you want to scan Dublin and Ohio `-f 'eu-west-1 us-east-s'`, note the single quotes and space between regions.
|
||||
Prowler has two parameters related to regions: `-r` that is used query AWS services API endpoints (it uses `us-east-1` by default and required for GovCloud or China) and the option `-f` that is to filter those regions you only want to scan. For example if you want to scan Dublin only use `-f eu-west-1` and if you want to scan Dublin and Ohio `-f eu-west-1,us-east-1`, note the regions are separated by a comma delimiter (it can be used as before with `-f 'eu-west-1,us-east-1'`).
|
||||
|
||||
## Screenshots
|
||||
|
||||
@@ -216,7 +267,7 @@ Prowler has two parameters related to regions: `-r` that is used query AWS servi
|
||||
|
||||
<img width="900" alt="Prowler html" src="https://user-images.githubusercontent.com/3985464/141443976-41d32cc2-533d-405a-92cb-affc3995d6ec.png">
|
||||
|
||||
- Sample screenshot of the Quicksight dashboard, see [https://quicksight-security-dashboard.workshop.aws](quicksight-security-dashboard.workshop.aws/):
|
||||
- Sample screenshot of the Quicksight dashboard, see [quicksight-security-dashboard.workshop.aws](https://quicksight-security-dashboard.workshop.aws/):
|
||||
|
||||
<img width="900" alt="Prowler with Quicksight" src="https://user-images.githubusercontent.com/3985464/128932819-0156e838-286d-483c-b953-fda68a325a3d.png">
|
||||
|
||||
@@ -228,80 +279,260 @@ Prowler has two parameters related to regions: `-r` that is used query AWS servi
|
||||
|
||||
1. If you want to save your report for later analysis thare are different ways, natively (supported text, mono, csv, json, json-asff, junit-xml and html, see note below for more info):
|
||||
|
||||
```sh
|
||||
./prowler -M csv
|
||||
```
|
||||
```sh
|
||||
./prowler -M csv
|
||||
```
|
||||
|
||||
or with multiple formats at the same time:
|
||||
or with multiple formats at the same time:
|
||||
|
||||
```sh
|
||||
./prowler -M csv,json,json-asff,html
|
||||
```
|
||||
```sh
|
||||
./prowler -M csv,json,json-asff,html
|
||||
```
|
||||
|
||||
or just a group of checks in multiple formats:
|
||||
or just a group of checks in multiple formats:
|
||||
|
||||
```sh
|
||||
./prowler -g gdpr -M csv,json,json-asff
|
||||
```
|
||||
```sh
|
||||
./prowler -g gdpr -M csv,json,json-asff
|
||||
```
|
||||
|
||||
or if you want a sorted and dynamic HTML report do:
|
||||
or if you want a sorted and dynamic HTML report do:
|
||||
|
||||
```sh
|
||||
./prowler -M html
|
||||
```
|
||||
```sh
|
||||
./prowler -M html
|
||||
```
|
||||
|
||||
Now `-M` creates a file inside the prowler `output` directory named `prowler-output-AWSACCOUNTID-YYYYMMDDHHMMSS.format`. You don't have to specify anything else, no pipes, no redirects.
|
||||
Now `-M` creates a file inside the prowler `output` directory named `prowler-output-AWSACCOUNTID-YYYYMMDDHHMMSS.format`. You don't have to specify anything else, no pipes, no redirects.
|
||||
|
||||
or just saving the output to a file like below:
|
||||
or just saving the output to a file like below:
|
||||
|
||||
```sh
|
||||
./prowler -M mono > prowler-report.txt
|
||||
```
|
||||
```sh
|
||||
./prowler -M mono > prowler-report.txt
|
||||
```
|
||||
|
||||
To generate JUnit report files, include the junit-xml format. This can be combined with any other format. Files are written inside a prowler root directory named `junit-reports`:
|
||||
To generate JUnit report files, include the junit-xml format. This can be combined with any other format. Files are written inside a prowler root directory named `junit-reports`:
|
||||
|
||||
```sh
|
||||
./prowler -M text,junit-xml
|
||||
```
|
||||
```sh
|
||||
./prowler -M text,junit-xml
|
||||
```
|
||||
|
||||
>Note about output formats to use with `-M`: "text" is the default one with colors, "mono" is like default one but monochrome, "csv" is comma separated values, "json" plain basic json (without comma between lines) and "json-asff" is also json with Amazon Security Finding Format that you can ship to Security Hub using `-S`.
|
||||
> Note about output formats to use with `-M`: "text" is the default one with colors, "mono" is like default one but monochrome, "csv" is comma separated values, "json" plain basic json (without comma between lines) and "json-asff" is also json with Amazon Security Finding Format that you can ship to Security Hub using `-S`.
|
||||
|
||||
or save your report in an S3 bucket (this only works for text or mono. For csv, json or json-asff it has to be copied afterwards):
|
||||
To save your report in an S3 bucket, use `-B` to define a custom output bucket along with `-M` to define the output format that is going to be uploaded to S3:
|
||||
|
||||
```sh
|
||||
./prowler -M mono | aws s3 cp - s3://bucket-name/prowler-report.txt
|
||||
```
|
||||
```sh
|
||||
./prowler -M csv -B my-bucket/folder/
|
||||
```
|
||||
|
||||
When generating multiple formats and running using Docker, to retrieve the reports, bind a local directory to the container, e.g.:
|
||||
> In the case you do not want to use the assumed role credentials but the initial credentials to put the reports into the S3 bucket, use `-D` instead of `-B`. Make sure that the used credentials have s3:PutObject permissions in the S3 path where the reports are going to be uploaded.
|
||||
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --volume "$(pwd)":/prowler/output --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest -M csv,json
|
||||
```
|
||||
When generating multiple formats and running using Docker, to retrieve the reports, bind a local directory to the container, e.g.:
|
||||
|
||||
```sh
|
||||
docker run -ti --rm --name prowler --volume "$(pwd)":/prowler/output --env AWS_ACCESS_KEY_ID --env AWS_SECRET_ACCESS_KEY --env AWS_SESSION_TOKEN toniblyx/prowler:latest -M csv,json
|
||||
```
|
||||
|
||||
1. To perform an assessment based on CIS Profile Definitions you can use cislevel1 or cislevel2 with `-g` flag, more information about this [here, page 8](https://d0.awsstatic.com/whitepapers/compliance/AWS_CIS_Foundations_Benchmark.pdf):
|
||||
|
||||
```sh
|
||||
./prowler -g cislevel1
|
||||
```
|
||||
```sh
|
||||
./prowler -g cislevel1
|
||||
```
|
||||
|
||||
1. If you want to run Prowler to check multiple AWS accounts in parallel (runs up to 4 simultaneously `-P 4`) but you may want to read below in Advanced Usage section to do so assuming a role:
|
||||
|
||||
```sh
|
||||
grep -E '^\[([0-9A-Aa-z_-]+)\]' ~/.aws/credentials | tr -d '][' | shuf | \
|
||||
xargs -n 1 -L 1 -I @ -r -P 4 ./prowler -p @ -M csv 2> /dev/null >> all-accounts.csv
|
||||
```
|
||||
```sh
|
||||
grep -E '^\[([0-9A-Aa-z_-]+)\]' ~/.aws/credentials | tr -d '][' | shuf | \
|
||||
xargs -n 1 -L 1 -I @ -r -P 4 ./prowler -p @ -M csv 2> /dev/null >> all-accounts.csv
|
||||
```
|
||||
|
||||
1. For help about usage run:
|
||||
|
||||
```
|
||||
./prowler -h
|
||||
```
|
||||
```
|
||||
./prowler -h
|
||||
```
|
||||
|
||||
## Database providers connector
|
||||
|
||||
You can send the Prowler's output to different databases (right now only PostgreSQL is supported).
|
||||
|
||||
Jump into the section for the database provider you want to use and follow the required steps to configure it.
|
||||
|
||||
### PostgreSQL
|
||||
|
||||
Install psql
|
||||
|
||||
- Mac -> `brew install libpq`
|
||||
- Ubuntu -> `sudo apt-get install postgresql-client `
|
||||
- RHEL/Centos -> `sudo yum install postgresql10`
|
||||
|
||||
#### Audit ID Field
|
||||
|
||||
To use Prowler postgres connector it is needed to set the -u flag to include `audit_id` field into the query. This field helps to identify each audit that has been made in the database. This field needs to be an UUID V4 to match the table schema.
|
||||
For example:
|
||||
```
|
||||
./prowler -M csv -d postgresql -u e5a0f214-8bf9-4600-a0c3-ff659b30e6c0
|
||||
```
|
||||
|
||||
#### Credentials
|
||||
|
||||
There are two options to pass the PostgreSQL credentials to Prowler:
|
||||
|
||||
##### Using a .pgpass file
|
||||
|
||||
Configure a `~/.pgpass` file into the root folder of the user that is going to launch Prowler ([pgpass file doc](https://www.postgresql.org/docs/current/libpq-pgpass.html)), including an extra field at the end of the line, separated by `:`, to name the table, using the following format:
|
||||
`hostname:port:database:username:password:table`
|
||||
|
||||
##### Using environment variables
|
||||
|
||||
- Configure the following environment variables:
|
||||
- `POSTGRES_HOST`
|
||||
- `POSTGRES_PORT`
|
||||
- `POSTGRES_USER`
|
||||
- `POSTGRES_PASSWORD`
|
||||
- `POSTGRES_DB`
|
||||
- `POSTGRES_TABLE`
|
||||
> _Note_: If you are using a schema different than postgres please include it at the beginning of the `POSTGRES_TABLE` variable, like: `export POSTGRES_TABLE=prowler.findings`
|
||||
|
||||
Also you need to have enabled the `uuid` postgresql extension, to enable it:
|
||||
|
||||
`CREATE EXTENSION IF NOT EXISTS "uuid-ossp";`
|
||||
|
||||
Create a table in your PostgreSQL database to store the Prowler's data. You can use the following SQL statement to create the table:
|
||||
|
||||
```
|
||||
CREATE TABLE IF NOT EXISTS prowler_findings (
|
||||
id uuid,
|
||||
audit_id uuid ,
|
||||
profile text,
|
||||
account_number text,
|
||||
region text,
|
||||
check_id text,
|
||||
result text,
|
||||
item_scored text,
|
||||
item_level text,
|
||||
check_title text,
|
||||
result_extended text,
|
||||
check_asff_compliance_type text,
|
||||
severity text,
|
||||
service_name text,
|
||||
check_asff_resource_type text,
|
||||
check_asff_type text,
|
||||
risk text,
|
||||
remediation text,
|
||||
documentation text,
|
||||
check_caf_epic text,
|
||||
resource_id text,
|
||||
account_details_email text,
|
||||
account_details_name text,
|
||||
account_details_arn text,
|
||||
account_details_org text,
|
||||
account_details_tags text,
|
||||
prowler_start_time text
|
||||
);
|
||||
```
|
||||
|
||||
- Execute Prowler with `-d` flag, for example:
|
||||
`./prowler -M csv -d postgresql -u e5a0f214-8bf9-4600-a0c3-ff659b30e6c0`
|
||||
> _Note_: This command creates a `csv` output file and stores the Prowler output in the configured PostgreSQL DB. It's an example, `-d` flag **does not** require `-M` to run.
|
||||
|
||||
## Output Formats
|
||||
|
||||
Prowler supports natively the following output formats:
|
||||
|
||||
- CSV
|
||||
- JSON
|
||||
- JSON-ASFF
|
||||
- HTML
|
||||
- JUNIT-XML
|
||||
|
||||
Hereunder is the structure for each of them
|
||||
|
||||
### CSV
|
||||
|
||||
| PROFILE | ACCOUNT_NUM | REGION | TITLE_ID | CHECK_RESULT | ITEM_SCORED | ITEM_LEVEL | TITLE_TEXT | CHECK_RESULT_EXTENDED | CHECK_ASFF_COMPLIANCE_TYPE | CHECK_SEVERITY | CHECK_SERVICENAME | CHECK_ASFF_RESOURCE_TYPE | CHECK_ASFF_TYPE | CHECK_RISK | CHECK_REMEDIATION | CHECK_DOC | CHECK_CAF_EPIC | CHECK_RESOURCE_ID | PROWLER_START_TIME | ACCOUNT_DETAILS_EMAIL | ACCOUNT_DETAILS_NAME | ACCOUNT_DETAILS_ARN | ACCOUNT_DETAILS_ORG | ACCOUNT_DETAILS_TAGS |
|
||||
| ------- | ----------- | ------ | -------- | ------------ | ----------- | ---------- | ---------- | --------------------- | -------------------------- | -------------- | ----------------- | ------------------------ | --------------- | ---------- | ----------------- | --------- | -------------- | ----------------- | ------------------ | --------------------- | -------------------- | ------------------- | ------------------- | -------------------- |
|
||||
|
||||
### JSON
|
||||
|
||||
```
|
||||
{
|
||||
"Profile": "ENV",
|
||||
"Account Number": "1111111111111",
|
||||
"Control": "[check14] Ensure access keys are rotated every 90 days or less",
|
||||
"Message": "us-west-2: user has not rotated access key 2 in over 90 days",
|
||||
"Severity": "Medium",
|
||||
"Status": "FAIL",
|
||||
"Scored": "",
|
||||
"Level": "CIS Level 1",
|
||||
"Control ID": "1.4",
|
||||
"Region": "us-west-2",
|
||||
"Timestamp": "2022-05-18T10:33:48Z",
|
||||
"Compliance": "ens-op.acc.1.aws.iam.4 ens-op.acc.5.aws.iam.3",
|
||||
"Service": "iam",
|
||||
"CAF Epic": "IAM",
|
||||
"Risk": "Access keys consist of an access key ID and secret access key which are used to sign programmatic requests that you make to AWS. AWS users need their own access keys to make programmatic calls to AWS from the AWS Command Line Interface (AWS CLI)- Tools for Windows PowerShell- the AWS SDKs- or direct HTTP calls using the APIs for individual AWS services. It is recommended that all access keys be regularly rotated.",
|
||||
"Remediation": "Use the credential report to ensure access_key_X_last_rotated is less than 90 days ago.",
|
||||
"Doc link": "https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_getting-report.html",
|
||||
"Resource ID": "terraform-user",
|
||||
"Account Email": "",
|
||||
"Account Name": "",
|
||||
"Account ARN": "",
|
||||
"Account Organization": "",
|
||||
"Account tags": ""
|
||||
}
|
||||
```
|
||||
|
||||
> NOTE: Each finding is a `json` object.
|
||||
|
||||
### JSON-ASFF
|
||||
|
||||
```
|
||||
{
|
||||
"SchemaVersion": "2018-10-08",
|
||||
"Id": "prowler-1.4-1111111111111-us-west-2-us-west-2_user_has_not_rotated_access_key_2_in_over_90_days",
|
||||
"ProductArn": "arn:aws:securityhub:us-west-2::product/prowler/prowler",
|
||||
"RecordState": "ACTIVE",
|
||||
"ProductFields": {
|
||||
"ProviderName": "Prowler",
|
||||
"ProviderVersion": "2.9.0-13April2022",
|
||||
"ProwlerResourceName": "user"
|
||||
},
|
||||
"GeneratorId": "prowler-check14",
|
||||
"AwsAccountId": "1111111111111",
|
||||
"Types": [
|
||||
"ens-op.acc.1.aws.iam.4 ens-op.acc.5.aws.iam.3"
|
||||
],
|
||||
"FirstObservedAt": "2022-05-18T10:33:48Z",
|
||||
"UpdatedAt": "2022-05-18T10:33:48Z",
|
||||
"CreatedAt": "2022-05-18T10:33:48Z",
|
||||
"Severity": {
|
||||
"Label": "MEDIUM"
|
||||
},
|
||||
"Title": "iam.[check14] Ensure access keys are rotated every 90 days or less",
|
||||
"Description": "us-west-2: user has not rotated access key 2 in over 90 days",
|
||||
"Resources": [
|
||||
{
|
||||
"Type": "AwsIamUser",
|
||||
"Id": "user",
|
||||
"Partition": "aws",
|
||||
"Region": "us-west-2"
|
||||
}
|
||||
],
|
||||
"Compliance": {
|
||||
"Status": "FAILED",
|
||||
"RelatedRequirements": [
|
||||
"ens-op.acc.1.aws.iam.4 ens-op.acc.5.aws.iam.3"
|
||||
]
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
> NOTE: Each finding is a `json` object.
|
||||
|
||||
## Advanced Usage
|
||||
|
||||
### Assume Role:
|
||||
|
||||
Prowler uses the AWS CLI underneath so it uses the same authentication methods. However, there are few ways to run Prowler against multiple accounts using IAM Assume Role feature depending on eachg use case. You can just set up your custom profile inside `~/.aws/config` with all needed information about the role to assume then call it with `./prowler -p your-custom-profile`. Additionally you can use `-A 123456789012` and `-R RemoteRoleToAssume` and Prowler will get those temporary credentials using `aws sts assume-role`, set them up as environment variables and run against that given account. To create a role to assume in multiple accounts easier eather as CFN Stack or StackSet, look at [this CloudFormation template](iam/create_role_to_assume_cfn.yaml) and adapt it.
|
||||
Prowler uses the AWS CLI underneath so it uses the same authentication methods. However, there are few ways to run Prowler against multiple accounts using IAM Assume Role feature depending on eachg use case. You can just set up your custom profile inside `~/.aws/config` with all needed information about the role to assume then call it with `./prowler -p your-custom-profile`. Additionally you can use `-A 123456789012` and `-R RemoteRoleToAssume` and Prowler will get those temporary credentials using `aws sts assume-role`, set them up as environment variables and run against that given account. To create a role to assume in multiple accounts easier either as CFN Stack or StackSet, look at [this CloudFormation template](iam/create_role_to_assume_cfn.yaml) and adapt it.
|
||||
|
||||
```sh
|
||||
./prowler -A 123456789012 -R ProwlerRole
|
||||
@@ -311,16 +542,18 @@ Prowler uses the AWS CLI underneath so it uses the same authentication methods.
|
||||
./prowler -A 123456789012 -R ProwlerRole -I 123456
|
||||
```
|
||||
|
||||
> *NOTE 1 about Session Duration*: By default it gets credentials valid for 1 hour (3600 seconds). Depending on the mount of checks you run and the size of your infrastructure, Prowler may require more than 1 hour to finish. Use option `-T <seconds>` to allow up to 12h (43200 seconds). To allow more than 1h you need to modify *"Maximum CLI/API session duration"* for that particular role, read more [here](https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use.html#id_roles_use_view-role-max-session).
|
||||
> _NOTE 1 about Session Duration_: By default it gets credentials valid for 1 hour (3600 seconds). Depending on the mount of checks you run and the size of your infrastructure, Prowler may require more than 1 hour to finish. Use option `-T <seconds>` to allow up to 12h (43200 seconds). To allow more than 1h you need to modify _"Maximum CLI/API session duration"_ for that particular role, read more [here](https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use.html#id_roles_use_view-role-max-session).
|
||||
|
||||
> *NOTE 2 about Session Duration*: Bear in mind that if you are using roles assumed by role chaining there is a hard limit of 1 hour so consider not using role chaining if possible, read more about that, in foot note 1 below the table [here](https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use.html).
|
||||
> _NOTE 2 about Session Duration_: Bear in mind that if you are using roles assumed by role chaining there is a hard limit of 1 hour so consider not using role chaining if possible, read more about that, in foot note 1 below the table [here](https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use.html).
|
||||
|
||||
For example, if you want to get only the fails in CSV format from all checks regarding RDS without banner from the AWS Account 123456789012 assuming the role RemoteRoleToAssume and set a fixed session duration of 1h:
|
||||
|
||||
```sh
|
||||
./prowler -A 123456789012 -R RemoteRoleToAssume -T 3600 -b -M cvs -q -g rds
|
||||
```
|
||||
|
||||
or with a given External ID:
|
||||
|
||||
```sh
|
||||
./prowler -A 123456789012 -R RemoteRoleToAssume -T 3600 -I 123456 -b -M cvs -q -g rds
|
||||
```
|
||||
@@ -330,30 +563,67 @@ or with a given External ID:
|
||||
If you want to run Prowler or just a check or a group across all accounts of AWS Organizations you can do this:
|
||||
|
||||
First get a list of accounts that are not suspended:
|
||||
|
||||
```
|
||||
ACCOUNTS_IN_ORGS=$(aws organizations list-accounts --query Accounts[?Status==`ACTIVE`].Id --output text)
|
||||
```
|
||||
|
||||
Then run Prowler to assume a role (same in all members) per each account, in this example it is just running one particular check:
|
||||
|
||||
```
|
||||
for accountId in $ACCOUNTS_IN_ORGS; do ./prowler -A $accountId -R RemoteRoleToAssume -c extra79; done
|
||||
```
|
||||
Usig the same for loop it can be scanned a list of accounts with a variable like `ACCOUNTS_LIST='11111111111 2222222222 333333333'`
|
||||
|
||||
Using the same for loop it can be scanned a list of accounts with a variable like `ACCOUNTS_LIST='11111111111 2222222222 333333333'`
|
||||
|
||||
### Get AWS Account details from your AWS Organization:
|
||||
|
||||
From Prowler v2.8, you can get additional information of the scanned account in CSV and JSON outputs. When scanning a single account you get the Account ID as part of the output. Now, if you have AWS Organizations and are scanning multiple accounts using the assume role functionality, Prowler can get your account details like Account Name, Email, ARN, Organization ID and Tags and you will have them next to every finding in the CSV and JSON outputs.
|
||||
In order to do that you can use the new option `-O <management account id>`, requires `-R <role to assume>` and also needs permissions `organizations:ListAccounts*` and `organizations:ListTagsForResource`. See the following sample command:
|
||||
|
||||
```
|
||||
./prowler -R ProwlerScanRole -A 111111111111 -O 222222222222 -M json,csv
|
||||
```
|
||||
|
||||
In that command Prowler will scan the account `111111111111` assuming the role `ProwlerScanRole` and getting the account details from the AWS Organizatiosn management account `222222222222` assuming the same role `ProwlerScanRole` for that and creating two reports with those details in JSON and CSV.
|
||||
|
||||
In the JSON output below (redacted) you can see tags coded in base64 to prevent breaking CSV or JSON due to its format:
|
||||
|
||||
```json
|
||||
"Account Email": "my-prod-account@domain.com",
|
||||
"Account Name": "my-prod-account",
|
||||
"Account ARN": "arn:aws:organizations::222222222222:account/o-abcde1234/111111111111",
|
||||
"Account Organization": "o-abcde1234",
|
||||
"Account tags": "\"eyJUYWdzIjpasf0=\""
|
||||
```
|
||||
|
||||
The additional fields in CSV header output are as follow:
|
||||
|
||||
```csv
|
||||
ACCOUNT_DETAILS_EMAIL,ACCOUNT_DETAILS_NAME,ACCOUNT_DETAILS_ARN,ACCOUNT_DETAILS_ORG,ACCOUNT_DETAILS_TAGS
|
||||
```
|
||||
|
||||
### GovCloud
|
||||
|
||||
Prowler runs in GovCloud regions as well. To make sure it points to the right API endpoint use `-r` to either `us-gov-west-1` or `us-gov-east-1`. If not filter region is used it will look for resources in both GovCloud regions by default:
|
||||
|
||||
```sh
|
||||
./prowler -r us-gov-west-1
|
||||
```
|
||||
|
||||
> For Security Hub integration see below in Security Hub section.
|
||||
|
||||
### Custom folder for custom checks
|
||||
|
||||
Flag `-x /my/own/checks` will include any check in that particular directory. To see how to write checks see [Add Custom Checks](#add-custom-checks) section.
|
||||
Flag `-x /my/own/checks` will include any check in that particular directory (files must start by check). To see how to write checks see [Add Custom Checks](#add-custom-checks) section.
|
||||
|
||||
S3 URIs are also supported as custom folders for custom checks, e.g. `s3://bucket/prefix/checks`. Prowler will download the folder locally and run the checks as they are called with default execution,`-c` or `-g`.
|
||||
|
||||
> Make sure that the used credentials have s3:GetObject permissions in the S3 path where the custom checks are located.
|
||||
|
||||
### Show or log only FAILs
|
||||
|
||||
In order to remove noise and get only FAIL findings there is a `-q` flag that makes Prowler to show and log only FAILs.
|
||||
In order to remove noise and get only FAIL findings there is a `-q` flag that makes Prowler to show and log only FAILs.
|
||||
It can be combined with any other option.
|
||||
Will show WARNINGS when a resource is excluded, just to take into consideration.
|
||||
|
||||
@@ -371,34 +641,39 @@ Sets the entropy limit for high entropy hex strings from environment variable `H
|
||||
export BASE64_LIMIT=4.5
|
||||
export HEX_LIMIT=3.0
|
||||
```
|
||||
|
||||
### Run Prowler using AWS CloudShell
|
||||
|
||||
An easy way to run Prowler to scan your account is using AWS CloudShell. Read more and learn how to do it [here](util/cloudshell/README.md).
|
||||
|
||||
## Security Hub integration
|
||||
|
||||
Since October 30th 2020 (version v2.3RC5), Prowler supports natively and as **official integration** sending findings to [AWS Security Hub](https://aws.amazon.com/security-hub). This integration allows Prowler to import its findings to AWS Security Hub. With Security Hub, you now have a single place that aggregates, organizes, and prioritizes your security alerts, or findings, from multiple AWS services, such as Amazon GuardDuty, Amazon Inspector, Amazon Macie, AWS Identity and Access Management (IAM) Access Analyzer, and AWS Firewall Manager, as well as from AWS Partner solutions and from Prowler for free.
|
||||
Since October 30th 2020 (version v2.3RC5), Prowler supports natively and as **official integration** sending findings to [AWS Security Hub](https://aws.amazon.com/security-hub). This integration allows Prowler to import its findings to AWS Security Hub. With Security Hub, you now have a single place that aggregates, organizes, and prioritizes your security alerts, or findings, from multiple AWS services, such as Amazon GuardDuty, Amazon Inspector, Amazon Macie, AWS Identity and Access Management (IAM) Access Analyzer, and AWS Firewall Manager, as well as from AWS Partner solutions and from Prowler for free.
|
||||
|
||||
Before sending findings to Prowler, you need to perform next steps:
|
||||
1. Since Security Hub is a region based service, enable it in the region or regions you require. Use the AWS Management Console or using the AWS CLI with this command if you have enough permissions:
|
||||
- `aws securityhub enable-security-hub --region <region>`.
|
||||
2. Enable Prowler as partner integration integration. Use the AWS Management Console or using the AWS CLI with this command if you have enough permissions:
|
||||
- `aws securityhub enable-import-findings-for-product --region <region> --product-arn arn:aws:securityhub:<region>::product/prowler/prowler` (change region also inside the ARN).
|
||||
- Using the AWS Management Console:
|
||||

|
||||
|
||||
1. Since Security Hub is a region based service, enable it in the region or regions you require. Use the AWS Management Console or using the AWS CLI with this command if you have enough permissions:
|
||||
- `aws securityhub enable-security-hub --region <region>`.
|
||||
2. Enable Prowler as partner integration integration. Use the AWS Management Console or using the AWS CLI with this command if you have enough permissions:
|
||||
- `aws securityhub enable-import-findings-for-product --region <region> --product-arn arn:aws:securityhub:<region>::product/prowler/prowler` (change region also inside the ARN).
|
||||
- Using the AWS Management Console:
|
||||

|
||||
3. As mentioned in section "Custom IAM Policy", to allow Prowler to import its findings to AWS Security Hub you need to add the policy below to the role or user running Prowler:
|
||||
- [iam/prowler-security-hub.json](iam/prowler-security-hub.json)
|
||||
- [iam/prowler-security-hub.json](iam/prowler-security-hub.json)
|
||||
|
||||
Once it is enabled, it is as simple as running the command below (for all regions):
|
||||
|
||||
```sh
|
||||
./prowler -M json-asff -S
|
||||
```
|
||||
|
||||
or for only one filtered region like eu-west-1:
|
||||
|
||||
```sh
|
||||
./prowler -M json-asff -q -S -f eu-west-1
|
||||
```
|
||||
> Note 1: It is recommended to send only fails to Security Hub and that is possible adding `-q` to the command.
|
||||
|
||||
> Note 1: It is recommended to send only fails to Security Hub and that is possible adding `-q` to the command.
|
||||
|
||||
> Note 2: Since Prowler perform checks to all regions by defaults you may need to filter by region when runing Security Hub integration, as shown in the example above. Remember to enable Security Hub in the region or regions you need by calling `aws securityhub enable-security-hub --region <region>` and run Prowler with the option `-f <region>` (if no region is used it will try to push findings in all regions hubs).
|
||||
|
||||
@@ -411,6 +686,7 @@ Once you run findings for first time you will be able to see Prowler findings in
|
||||
### Security Hub in GovCloud regions
|
||||
|
||||
To use Prowler and Security Hub integration in GovCloud there is an additional requirement, usage of `-r` is needed to point the API queries to the right API endpoint. Here is a sample command that sends only failed findings to Security Hub in region `us-gov-west-1`:
|
||||
|
||||
```
|
||||
./prowler -r us-gov-west-1 -f us-gov-west-1 -S -M csv,json-asff -q
|
||||
```
|
||||
@@ -418,6 +694,7 @@ To use Prowler and Security Hub integration in GovCloud there is an additional r
|
||||
### Security Hub in China regions
|
||||
|
||||
To use Prowler and Security Hub integration in China regions there is an additional requirement, usage of `-r` is needed to point the API queries to the right API endpoint. Here is a sample command that sends only failed findings to Security Hub in region `cn-north-1`:
|
||||
|
||||
```
|
||||
./prowler -r cn-north-1 -f cn-north-1 -q -S -M csv,json-asff
|
||||
```
|
||||
@@ -426,19 +703,39 @@ To use Prowler and Security Hub integration in China regions there is an additio
|
||||
|
||||
Either to run Prowler once or based on a schedule this template makes it pretty straight forward. This template will create a CodeBuild environment and run Prowler directly leaving all reports in a bucket and creating a report also inside CodeBuild basedon the JUnit output from Prowler. Scheduling can be cron based like `cron(0 22 * * ? *)` or rate based like `rate(5 hours)` since CloudWatch Event rules (or Eventbridge) is used here.
|
||||
|
||||
The Cloud Formation template that helps you doing that is [here](https://github.com/toniblyx/prowler/blob/master/util/codebuild/codebuild-prowler-audit-account-cfn.yaml).
|
||||
The Cloud Formation template that helps you to do that is [here](https://github.com/prowler-cloud/prowler/blob/master/util/codebuild/codebuild-prowler-audit-account-cfn.yaml).
|
||||
|
||||
> This is a simple solution to monitor one account. For multiples accounts see [Multi Account and Continuous Monitoring](util/org-multi-account/README.md).
|
||||
|
||||
## Whitelist or allowlist or remove a fail from resources
|
||||
## Allowlist or remove a fail from resources
|
||||
|
||||
Sometimes you may find resources that are intentionally configured in a certain way that may be a bad practice but it is all right with it, for example an S3 bucket open to the internet hosting a web site, or a security group with an open port needed in your use case. Now you can use `-w whitelist_sample.txt` and add your resources as `checkID:resourcename` as in this command:
|
||||
Sometimes you may find resources that are intentionally configured in a certain way that may be a bad practice but it is all right with it, for example an S3 bucket open to the internet hosting a web site, or a security group with an open port needed in your use case. Now you can use `-w allowlist_sample.txt` and add your resources as `checkID:resourcename` as in this command:
|
||||
|
||||
```
|
||||
./prowler -w whitelist_sample.txt
|
||||
./prowler -w allowlist_sample.txt
|
||||
```
|
||||
|
||||
Whitelist option works along with other options and adds a `WARNING` instead of `INFO`, `PASS` or `FAIL` to any output format except for `json-asff`.
|
||||
S3 URIs are also supported as allowlist file, e.g. `s3://bucket/prefix/allowlist_sample.txt`
|
||||
|
||||
> Make sure that the used credentials have s3:GetObject permissions in the S3 path where the allowlist file is located.
|
||||
|
||||
DynamoDB table ARNs are also supported as allowlist file, e.g. `arn:aws:dynamodb:us-east-1:111111222222:table/allowlist`
|
||||
|
||||
> Make sure that the table has `account_id` as partition key and `rule` as sort key, and that the used credentials have `dynamodb:PartiQLSelect` permissions in the table.
|
||||
>
|
||||
> <p align="left"><img src="https://user-images.githubusercontent.com/38561120/165769502-296f9075-7cc8-445e-8158-4b21804bfe7e.png" alt="image" width="397" height="252" /></p>
|
||||
|
||||
> The field `account_id` can contain either an account ID or an `*` (which applies to all the accounts that use this table as a whitelist). As in the traditional allowlist file, the `rule` field must contain `checkID:resourcename` pattern.
|
||||
>
|
||||
> <p><img src="https://user-images.githubusercontent.com/38561120/165770610-ed5c2764-7538-44c2-9195-bcfdecc4ef9b.png" alt="image" width="394" /></p>
|
||||
|
||||
Allowlist option works along with other options and adds a `WARNING` instead of `INFO`, `PASS` or `FAIL` to any output format except for `json-asff`.
|
||||
|
||||
## Inventory
|
||||
|
||||
With Prowler you can get an inventory of your AWS resources. To do so, run `./prowler -i` to see what AWS resources you have deployed in your AWS account. This feature lists almost all resources in all regions based on [this](https://docs.aws.amazon.com/resourcegroupstagging/latest/APIReference/API_GetResources.html) API call. Note that it does not cover 100% of resource types.
|
||||
|
||||
The inventory will be stored in an output `csv` file by default, under common Prowler `output` folder, with the following format: `prowler-inventory-${ACCOUNT_NUM}-${OUTPUT_DATE}.csv`
|
||||
|
||||
## How to fix every FAIL
|
||||
|
||||
@@ -480,10 +777,12 @@ There are some helpfull tools to save time in this process like [aws-mfa-script]
|
||||
### AWS Managed IAM Policies
|
||||
|
||||
[ViewOnlyAccess](https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies_job-functions.html#jf_view-only-user)
|
||||
|
||||
- Use case: This user can view a list of AWS resources and basic metadata in the account across all services. The user cannot read resource content or metadata that goes beyond the quota and list information for resources.
|
||||
- Policy description: This policy grants List*, Describe*, Get*, View*, and Lookup* access to resources for most AWS services. To see what actions this policy includes for each service, see [ViewOnlyAccess Permissions](https://console.aws.amazon.com/iam/home#policies/arn:aws:iam::aws:policy/job-function/ViewOnlyAccess)
|
||||
- Policy description: This policy grants List*, Describe*, Get*, View*, and Lookup\* access to resources for most AWS services. To see what actions this policy includes for each service, see [ViewOnlyAccess Permissions](https://console.aws.amazon.com/iam/home#policies/arn:aws:iam::aws:policy/job-function/ViewOnlyAccess)
|
||||
|
||||
[SecurityAudit](https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies_job-functions.html#jf_security-auditor)
|
||||
|
||||
- Use case: This user monitors accounts for compliance with security requirements. This user can access logs and events to investigate potential security breaches or potential malicious activity.
|
||||
- Policy description: This policy grants permissions to view configuration data for many AWS services and to review their logs. To see what actions this policy includes for each service, see [SecurityAudit Permissions](https://console.aws.amazon.com/iam/home#policies/arn:aws:iam::aws:policy/SecurityAudit)
|
||||
|
||||
@@ -503,7 +802,7 @@ Allows Prowler to import its findings to [AWS Security Hub](https://aws.amazon.c
|
||||
|
||||
### Bootstrap Script
|
||||
|
||||
Quick bash script to set up a "prowler" IAM user with "SecurityAudit" and "ViewOnlyAccess" group with the required permissions (including "Prowler-Additions-Policy"). To run the script below, you need user with administrative permissions; set the `AWS_DEFAULT_PROFILE` to use that account:
|
||||
Quick bash script to set up a "prowler" IAM user with "SecurityAudit" and "ViewOnlyAccess" group with the required permissions (including "Prowler-Additions-Policy"). To run the script below, you need a user with administrative permissions; set the `AWS_DEFAULT_PROFILE` to use that account:
|
||||
|
||||
```sh
|
||||
export AWS_DEFAULT_PROFILE=default
|
||||
@@ -519,7 +818,7 @@ aws iam create-access-key --user-name prowler
|
||||
unset ACCOUNT_ID AWS_DEFAULT_PROFILE
|
||||
```
|
||||
|
||||
The `aws iam create-access-key` command will output the secret access key and the key id; keep these somewhere safe, and add them to `~/.aws/credentials` with an appropriate profile name to use them with Prowler. This is the only time they secret key will be shown. If you lose it, you will need to generate a replacement.
|
||||
The `aws iam create-access-key` command will output the secret access key and the key id; keep these somewhere safe, and add them to `~/.aws/credentials` with an appropriate profile name to use them with Prowler. This is the only time the secret key will be shown. If you lose it, you will need to generate a replacement.
|
||||
|
||||
> [This CloudFormation template](iam/create_role_to_assume_cfn.yaml) may also help you on that task.
|
||||
|
||||
@@ -535,7 +834,7 @@ To list all existing checks in the extras group run the command below:
|
||||
./prowler -l -g extras
|
||||
```
|
||||
|
||||
>There are some checks not included in that list, they are experimental or checks that takes long to run like `extra759` and `extra760` (search for secrets in Lambda function variables and code).
|
||||
> There are some checks not included in that list, they are experimental or checks that take long to run like `extra759` and `extra760` (search for secrets in Lambda function variables and code).
|
||||
|
||||
To check all extras in one command:
|
||||
|
||||
@@ -555,7 +854,6 @@ or to run multiple extras in one go:
|
||||
./prowler -c extraNumber,extraNumber
|
||||
```
|
||||
|
||||
|
||||
## Forensics Ready Checks
|
||||
|
||||
With this group of checks, Prowler looks if each service with logging or audit capabilities has them enabled to ensure all needed evidences are recorded and collected for an eventual digital forensic investigation in case of incident. List of checks part of this group (you can also see all groups with `./prowler -L`). The list of checks can be seen in the group file at:
|
||||
@@ -570,7 +868,7 @@ The `forensics-ready` group of checks uses existing and extra checks. To get a f
|
||||
|
||||
## GDPR Checks
|
||||
|
||||
With this group of checks, Prowler shows result of checks related to GDPR, more information [here](https://github.com/toniblyx/prowler/issues/189). The list of checks can be seen in the group file at:
|
||||
With this group of checks, Prowler shows result of checks related to GDPR, more information [here](https://github.com/prowler-cloud/prowler/issues/189). The list of checks can be seen in the group file at:
|
||||
|
||||
[groups/group9_gdpr](groups/group9_gdpr)
|
||||
|
||||
@@ -584,7 +882,7 @@ The `gdpr` group of checks uses existing and extra checks. To get a GDPR report,
|
||||
|
||||
With this group of checks, Prowler shows result of checks related to the AWS Foundational Technical Review, more information [here](https://apn-checklists.s3.amazonaws.com/foundational/partner-hosted/partner-hosted/CVLHEC5X7.html). The list of checks can be seen in the group file at:
|
||||
|
||||
[groups/group25_ftr](groups/group25_ftr)
|
||||
[groups/group25_ftr](groups/group25_FTR)
|
||||
|
||||
The `ftr` group of checks uses existing and extra checks. To get a AWS FTR report, run this command:
|
||||
|
||||
@@ -596,7 +894,7 @@ The `ftr` group of checks uses existing and extra checks. To get a AWS FTR repor
|
||||
|
||||
With this group of checks, Prowler shows results of controls related to the "Security Rule" of the Health Insurance Portability and Accountability Act aka [HIPAA](https://www.hhs.gov/hipaa/for-professionals/security/index.html) as defined in [45 CFR Subpart C - Security Standards for the Protection of Electronic Protected Health Information](https://www.law.cornell.edu/cfr/text/45/part-164/subpart-C) within [PART 160 - GENERAL ADMINISTRATIVE REQUIREMENTS](https://www.law.cornell.edu/cfr/text/45/part-160) and [Subpart A](https://www.law.cornell.edu/cfr/text/45/part-164/subpart-A) and [Subpart C](https://www.law.cornell.edu/cfr/text/45/part-164/subpart-C) of PART 164 - SECURITY AND PRIVACY
|
||||
|
||||
More information on the original PR is [here](https://github.com/toniblyx/prowler/issues/227).
|
||||
More information on the original PR is [here](https://github.com/prowler-cloud/prowler/issues/227).
|
||||
|
||||
### Note on Business Associate Addendum's (BAA)
|
||||
|
||||
@@ -627,6 +925,7 @@ AWS is made to be flexible for service links within and between different AWS ac
|
||||
This group of checks helps to analyse a particular AWS account (subject) on existing links to other AWS accounts across various AWS services, in order to identify untrusted links.
|
||||
|
||||
### Run
|
||||
|
||||
To give it a quick shot just call:
|
||||
|
||||
```sh
|
||||
@@ -643,12 +942,12 @@ Currently, this check group supports two different scenarios:
|
||||
### Coverage
|
||||
|
||||
Current coverage of Amazon Web Service (AWS) taken from [here](https://docs.aws.amazon.com/whitepapers/latest/aws-overview/introduction.html):
|
||||
| Topic | Service | Trust Boundary |
|
||||
| Topic | Service | Trust Boundary |
|
||||
|---------------------------------|------------|---------------------------------------------------------------------------|
|
||||
| Networking and Content Delivery | Amazon VPC | VPC endpoints connections ([extra786](checks/check_extra786)) |
|
||||
| | | VPC endpoints whitelisted principals ([extra787](checks/check_extra787)) |
|
||||
| Networking and Content Delivery | Amazon VPC | VPC endpoints connections ([extra786](checks/check_extra786)) |
|
||||
| | | VPC endpoints allowlisted principals ([extra787](checks/check_extra787)) |
|
||||
|
||||
All ideas or recommendations to extend this group are very welcome [here](https://github.com/toniblyx/prowler/issues/new/choose).
|
||||
All ideas or recommendations to extend this group are very welcome [here](https://github.com/prowler-cloud/prowler/issues/new/choose).
|
||||
|
||||
### Detailed Explanation of the Concept
|
||||
|
||||
@@ -663,7 +962,17 @@ Single Account environment assumes that only the AWS account subject to this ana
|
||||
Multi Account environments assumes a minimum of two trusted or known accounts. For this particular example all trusted and known accounts will be tested. Therefore `GROUP_TRUSTBOUNDARIES_TRUSTED_ACCOUNT_IDS` variable in [groups/group16_trustboundaries](groups/group16_trustboundaries) should include all trusted accounts Account #A, Account #B, Account #C, and Account #D in order to finally raise Account #E and Account #F for being untrusted or unknown.
|
||||

|
||||
|
||||
## Add Custom Checks
|
||||
## Custom Checks
|
||||
|
||||
Using `./prowler -c extra9999 -a` you can build your own on-the-fly custom check by specifying the AWS CLI command to execute.
|
||||
|
||||
> Omit the "aws" command and only use its parameters within quotes and do not nest quotes in the aws parameter, --output text is already included in the check.
|
||||
>
|
||||
> Here is an example of a check to find SGs with inbound port 80:
|
||||
|
||||
```sh
|
||||
./prowler -c extra9999 -a 'ec2 describe-security-groups --filters Name=ip-permission.to-port,Values=80 --query SecurityGroups[*].GroupId[]]'
|
||||
```
|
||||
|
||||
In order to add any new check feel free to create a new extra check in the extras group or other group. To do so, you will need to follow these steps:
|
||||
|
||||
@@ -698,4 +1007,4 @@ Prowler is licensed as Apache License 2.0 as specified in each file. You may obt
|
||||
|
||||
**I'm not related anyhow with CIS organization, I just write and maintain Prowler to help companies over the world to make their cloud infrastructure more secure.**
|
||||
|
||||
If you want to contact me visit <https://blyx.com/contact> or follow me on Twitter <https://twitter.com/toniblyx> my DMs are open.
|
||||
If you want to contact me visit <https://blyx.com/contact> or follow me on Twitter <https://twitter.com/prowler-cloud> my DMs are open.
|
||||
|
||||
@@ -16,6 +16,14 @@ check26:myignoredbucket
|
||||
#<checkid2>:<resource to ignore 1>
|
||||
|
||||
# REGEXES
|
||||
# This whitelist works with regexes (ERE, the same style of regex as grep -E and bash's =~ use)
|
||||
# This allowlist works with regexes (ERE, the same style of regex as grep -E and bash's =~ use)
|
||||
# therefore:
|
||||
# extra718:[[:alnum:]]+-logs # will ignore all buckets containing the terms ci-logs, qa-logs, etc.
|
||||
# extra718:[[:alnum:]]+-logs # will ignore all buckets containing the terms ci-logs, qa-logs, etc.
|
||||
|
||||
# EXAMPLE: CONTROL TOWER
|
||||
# When using Control Tower, guardrails prevent access to certain protected resources. The allowlist
|
||||
# below ensures that warnings instead of errors are reported for the affected resources.
|
||||
#extra734:aws-controltower-logs-[[:digit:]]+-[[:alpha:]\-]+
|
||||
#extra734:aws-controltower-s3-access-logs-[[:digit:]]+-[[:alpha:]\-]+
|
||||
#extra764:aws-controltower-logs-[[:digit:]]+-[[:alpha:]\-]+
|
||||
#extra764:aws-controltower-s3-access-logs-[[:digit:]]+-[[:alpha:]\-]+
|
||||
+19
-15
@@ -25,23 +25,27 @@ CHECK_DOC_check11='http://docs.aws.amazon.com/IAM/latest/UserGuide/best-practice
|
||||
CHECK_CAF_EPIC_check11='IAM'
|
||||
|
||||
check11(){
|
||||
# "Avoid the use of the root account (Scored)."
|
||||
MAX_DAYS=-1
|
||||
last_login_dates=$(cat $TEMP_REPORT_FILE | awk -F, '{ print $1,$5,$11,$16 }' | grep '<root_account>' | cut -d' ' -f2,3,4)
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks."
|
||||
else
|
||||
# "Avoid the use of the root account (Scored)."
|
||||
MAX_DAYS=-1
|
||||
last_login_dates=$(cat $TEMP_REPORT_FILE | awk -F, '{ print $1,$5,$11,$16 }' | grep '<root_account>' | cut -d' ' -f2,3,4)
|
||||
|
||||
failures=0
|
||||
for date in $last_login_dates; do
|
||||
if [[ ${date%T*} =~ ^[0-9]{4}-[0-9]{2}-[0-9]{2}$ ]];then
|
||||
days_not_in_use=$(how_many_days_from_today ${date%T*})
|
||||
if [ "$days_not_in_use" -gt "$MAX_DAYS" ];then
|
||||
failures=1
|
||||
textFail "$REGION: Root user in the account was last accessed ${MAX_DAYS#-} day ago" "$REGION" "root"
|
||||
break
|
||||
failures=0
|
||||
for date in $last_login_dates; do
|
||||
if [[ ${date%T*} =~ ^[0-9]{4}-[0-9]{2}-[0-9]{2}$ ]];then
|
||||
days_not_in_use=$(how_many_days_from_today ${date%T*})
|
||||
if [ "$days_not_in_use" -gt "$MAX_DAYS" ];then
|
||||
failures=1
|
||||
textFail "$REGION: Root user in the account was last accessed ${MAX_DAYS#-} day ago" "$REGION" "root"
|
||||
break
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done
|
||||
done
|
||||
|
||||
if [[ $failures == 0 ]]; then
|
||||
textPass "$REGION: Root user in the account wasn't accessed in the last ${MAX_DAYS#-} days" "$REGION" "root"
|
||||
if [[ $failures == 0 ]]; then
|
||||
textPass "$REGION: Root user in the account wasn't accessed in the last ${MAX_DAYS#-} days" "$REGION" "root"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
+9
-5
@@ -25,11 +25,15 @@ CHECK_DOC_check113='https://docs.aws.amazon.com/IAM/latest/UserGuide/id_root-use
|
||||
CHECK_CAF_EPIC_check113='IAM'
|
||||
|
||||
check113(){
|
||||
# "Ensure MFA is enabled for the root account (Scored)"
|
||||
COMMAND113=$($AWSCLI iam get-account-summary $PROFILE_OPT --region $REGION --output json --query 'SummaryMap.AccountMFAEnabled')
|
||||
if [ "$COMMAND113" == "1" ]; then
|
||||
textPass "$REGION: Virtual MFA is enabled for root" "$REGION" "MFA"
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks."
|
||||
else
|
||||
textFail "$REGION: MFA is not ENABLED for root account" "$REGION" "MFA"
|
||||
# "Ensure MFA is enabled for the root account (Scored)"
|
||||
COMMAND113=$($AWSCLI iam get-account-summary $PROFILE_OPT --region $REGION --output json --query 'SummaryMap.AccountMFAEnabled')
|
||||
if [ "$COMMAND113" == "1" ]; then
|
||||
textPass "$REGION: Virtual MFA is enabled for root" "$REGION" "MFA"
|
||||
else
|
||||
textFail "$REGION: MFA is not ENABLED for root account" "$REGION" "MFA"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
+14
-10
@@ -25,16 +25,20 @@ CHECK_DOC_check114='https://docs.aws.amazon.com/IAM/latest/UserGuide/id_root-use
|
||||
CHECK_CAF_EPIC_check114='IAM'
|
||||
|
||||
check114(){
|
||||
# "Ensure hardware MFA is enabled for the root account (Scored)"
|
||||
COMMAND113=$($AWSCLI iam get-account-summary $PROFILE_OPT --region $REGION --output json --query 'SummaryMap.AccountMFAEnabled')
|
||||
if [ "$COMMAND113" == "1" ]; then
|
||||
COMMAND114=$($AWSCLI iam list-virtual-mfa-devices $PROFILE_OPT --region $REGION --output text --assignment-status Assigned --query 'VirtualMFADevices[*].[SerialNumber]' | grep "^arn:${AWS_PARTITION}:iam::[0-9]\{12\}:mfa/root-account-mfa-device$")
|
||||
if [[ "$COMMAND114" ]]; then
|
||||
textFail "$REGION: Only Virtual MFA is enabled for root" "$REGION" "MFA"
|
||||
else
|
||||
textPass "$REGION: Hardware MFA is enabled for root" "$REGION" "MFA"
|
||||
fi
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks."
|
||||
else
|
||||
textFail "$REGION: MFA is not ENABLED for root account" "$REGION" "MFA"
|
||||
# "Ensure hardware MFA is enabled for the root account (Scored)"
|
||||
COMMAND113=$($AWSCLI iam get-account-summary $PROFILE_OPT --region $REGION --output json --query 'SummaryMap.AccountMFAEnabled')
|
||||
if [ "$COMMAND113" == "1" ]; then
|
||||
COMMAND114=$($AWSCLI iam list-virtual-mfa-devices $PROFILE_OPT --region $REGION --output text --assignment-status Assigned --query 'VirtualMFADevices[*].[SerialNumber]' | grep "^arn:${AWS_PARTITION}:iam::[0-9]\{12\}:mfa/root-account-mfa-device$")
|
||||
if [[ "$COMMAND114" ]]; then
|
||||
textFail "$REGION: Only Virtual MFA is enabled for root" "$REGION" "MFA"
|
||||
else
|
||||
textPass "$REGION: Hardware MFA is enabled for root" "$REGION" "MFA"
|
||||
fi
|
||||
else
|
||||
textFail "$REGION: MFA is not ENABLED for root account" "$REGION" "MFA"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
+6
-2
@@ -25,6 +25,10 @@ CHECK_DOC_check115='https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credenti
|
||||
CHECK_CAF_EPIC_check115='IAM'
|
||||
|
||||
check115(){
|
||||
# "Ensure security questions are registered in the AWS account (Not Scored)"
|
||||
textInfo "No command available for check 1.15. Login to the AWS Console as root & click on the Account. Name -> My Account -> Configure Security Challenge Questions."
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks." "$REGION" "root"
|
||||
else
|
||||
# "Ensure security questions are registered in the AWS account (Not Scored)"
|
||||
textInfo "${REGION}: No command available for check 1.15. Login to the AWS Console as root & click on the Account. Name -> My Account -> Configure Security Challenge Questions." "$REGION" "root"
|
||||
fi
|
||||
}
|
||||
|
||||
+21
-15
@@ -29,20 +29,26 @@ CHECK_CAF_EPIC_check116='IAM'
|
||||
check116(){
|
||||
# "Ensure IAM policies are attached only to groups or roles (Scored)"
|
||||
LIST_USERS=$($AWSCLI iam list-users --query 'Users[*].UserName' --output text $PROFILE_OPT --region $REGION)
|
||||
C116_NUM_USERS=0
|
||||
for user in $LIST_USERS;do
|
||||
USER_POLICY=$($AWSCLI iam list-attached-user-policies --output text $PROFILE_OPT --region $REGION --user-name $user)
|
||||
if [[ $USER_POLICY ]]; then
|
||||
textFail "$REGION: $user has managed policy directly attached" "$REGION" "$user"
|
||||
C116_NUM_USERS=$(expr $C116_NUM_USERS + 1)
|
||||
fi
|
||||
USER_POLICY=$($AWSCLI iam list-user-policies --output text $PROFILE_OPT --region $REGION --user-name $user)
|
||||
if [[ $USER_POLICY ]]; then
|
||||
textFail "$REGION: $user has inline policy directly attached" "$REGION" "$user"
|
||||
C116_NUM_USERS=$(expr $C116_NUM_USERS + 1)
|
||||
fi
|
||||
done
|
||||
if [[ $C116_NUM_USERS -eq 0 ]]; then
|
||||
textPass "$REGION: No policies attached to users" "$REGION" "$user"
|
||||
if [[ "${LIST_USERS}" ]]
|
||||
then
|
||||
for user in $LIST_USERS;do
|
||||
USER_ATTACHED_POLICY=$($AWSCLI iam list-attached-user-policies --output text $PROFILE_OPT --region $REGION --user-name $user)
|
||||
USER_INLINE_POLICY=$($AWSCLI iam list-user-policies --output text $PROFILE_OPT --region $REGION --user-name $user)
|
||||
if [[ $USER_ATTACHED_POLICY ]] || [[ $USER_INLINE_POLICY ]]
|
||||
then
|
||||
if [[ $USER_ATTACHED_POLICY ]]
|
||||
then
|
||||
textFail "$REGION: $user has managed policy directly attached" "$REGION" "$user"
|
||||
fi
|
||||
if [[ $USER_INLINE_POLICY ]]
|
||||
then
|
||||
textFail "$REGION: $user has inline policy directly attached" "$REGION" "$user"
|
||||
fi
|
||||
else
|
||||
textPass "$REGION: No policies attached to user $user" "$REGION" "$user"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textPass "$REGION: No users found" "$REGION" "No users found"
|
||||
fi
|
||||
}
|
||||
|
||||
+16
-4
@@ -13,7 +13,7 @@
|
||||
|
||||
CHECK_ID_check117="1.17"
|
||||
CHECK_TITLE_check117="[check117] Maintain current contact details"
|
||||
CHECK_SCORED_check117="NOT_SCORED"
|
||||
CHECK_SCORED_check117="SCORED"
|
||||
CHECK_CIS_LEVEL_check117="LEVEL1"
|
||||
CHECK_SEVERITY_check117="Medium"
|
||||
CHECK_ASFF_TYPE_check117="Software and Configuration Checks/Industry and Regulatory Standards/CIS AWS Foundations Benchmark"
|
||||
@@ -25,7 +25,19 @@ CHECK_DOC_check117='https://docs.aws.amazon.com/awsaccountbilling/latest/aboutv2
|
||||
CHECK_CAF_EPIC_check117='IAM'
|
||||
|
||||
check117(){
|
||||
# "Maintain current contact details (Scored)"
|
||||
# No command available
|
||||
textInfo "No command available for check 1.17. See section 1.17 on the CIS Benchmark guide for details."
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks." "${REGION}" "root"
|
||||
else
|
||||
# "Maintain current contact details (Scored)"
|
||||
GET_CONTACT_DETAILS=$($AWSCLI account get-contact-information --output text $PROFILE_OPT --region "${REGION}" 2>&1)
|
||||
if grep -E -q 'AccessDenied|UnauthorizedOperation|AuthorizationError' <<< "${GET_CONTACT_DETAILS}"; then
|
||||
textInfo "${REGION}: Access Denied trying to get account contact information" "${REGION}"
|
||||
else
|
||||
if [[ ${GET_CONTACT_DETAILS} ]];then
|
||||
textPass "${REGION}: Account has contact information. Perhaps check for freshness of these details." "${REGION}" "root"
|
||||
else
|
||||
textFail "${REGION}: Unable to get account contact details. See section 1.17 on the CIS Benchmark guide for details." "${REGION}" "root"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
+16
-4
@@ -13,7 +13,7 @@
|
||||
|
||||
CHECK_ID_check118="1.18"
|
||||
CHECK_TITLE_check118="[check118] Ensure security contact information is registered"
|
||||
CHECK_SCORED_check118="NOT_SCORED"
|
||||
CHECK_SCORED_check118="SCORED"
|
||||
CHECK_CIS_LEVEL_check118="LEVEL1"
|
||||
CHECK_SEVERITY_check118="Medium"
|
||||
CHECK_ASFF_TYPE_check118="Software and Configuration Checks/Industry and Regulatory Standards/CIS AWS Foundations Benchmark"
|
||||
@@ -25,7 +25,19 @@ CHECK_DOC_check118='https://docs.aws.amazon.com/awsaccountbilling/latest/aboutv2
|
||||
CHECK_CAF_EPIC_check118='IAM'
|
||||
|
||||
check118(){
|
||||
# "Ensure security contact information is registered (Scored)"
|
||||
# No command available
|
||||
textInfo "No command available for check 1.18. See section 1.18 on the CIS Benchmark guide for details."
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks." "${REGION}" "root"
|
||||
else
|
||||
# "Ensure security contact information is registered (Scored)"
|
||||
GET_SECURITY_CONTACT_DETAILS=$("${AWSCLI}" account get-alternate-contact --alternate-contact-type SECURITY --output text ${PROFILE_OPT} --region "${REGION}" 2>&1)
|
||||
if grep -E -q 'AccessDenied|UnauthorizedOperation|AuthorizationError' <<< "${GET_SECURITY_CONTACT_DETAILS}"; then
|
||||
textInfo "${REGION}: Access Denied trying to get account contact information" "${REGION}"
|
||||
else
|
||||
if grep "SECURITY" <<< "${GET_SECURITY_CONTACT_DETAILS}"; then
|
||||
textPass "${REGION}: Account has security contact information. Perhaps check for freshness of these details." "${REGION}" "root"
|
||||
else
|
||||
textFail "${REGION}: Account has not security contact information, or it was unable to capture. See section 1.18 on the CIS Benchmark guide for details." "${REGION}" "root"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
+9
-4
@@ -21,15 +21,20 @@ CHECK_ASFF_RESOURCE_TYPE_check119="AwsEc2Instance"
|
||||
CHECK_ALTERNATE_check119="check119"
|
||||
CHECK_SERVICENAME_check119="ec2"
|
||||
CHECK_RISK_check119='AWS access from within AWS instances can be done by either encoding AWS keys into AWS API calls or by assigning the instance to a role which has an appropriate permissions policy for the required access. AWS IAM roles reduce the risks associated with sharing and rotating credentials that can be used outside of AWS itself. If credentials are compromised; they can be used from outside of the AWS account.'
|
||||
CHECK_REMEDIATION_check119='IAM roles can only be associated at the launch of an instance. To remediate an instance to add it to a role you must create or re-launch a new instance. (Check for external dependencies on its current private ip or public addresses).'
|
||||
CHECK_REMEDIATION_check119='Create an IAM instance role if necessary and attach it to the corresponding EC2 instance.'
|
||||
CHECK_DOC_check119='http://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use_switch-role-ec2.html'
|
||||
CHECK_CAF_EPIC_check119='IAM'
|
||||
|
||||
check119(){
|
||||
for regx in $REGIONS; do
|
||||
EC2_DATA=$($AWSCLI ec2 describe-instances $PROFILE_OPT --region $regx --query 'Reservations[].Instances[].[InstanceId, IamInstanceProfile.Arn, State.Name]' --output json)
|
||||
EC2_DATA=$(echo $EC2_DATA | jq '.[]|{InstanceId: .[0], ProfileArn: .[1], StateName: .[2]}')
|
||||
INSTANCE_LIST=$(echo $EC2_DATA | jq -r '.InstanceId')
|
||||
EC2_DATA=$($AWSCLI ec2 describe-instances $PROFILE_OPT --region $regx --query 'Reservations[].Instances[].[InstanceId, IamInstanceProfile.Arn, State.Name]' --output json 2>&1)
|
||||
if [[ $(echo "$EC2_DATA" | grep UnauthorizedOperation) ]]; then
|
||||
textInfo "$regx: Unauthorized Operation error trying to describe instances" "$regx"
|
||||
continue
|
||||
else
|
||||
EC2_DATA=$(echo $EC2_DATA | jq '.[]|{InstanceId: .[0], ProfileArn: .[1], StateName: .[2]}')
|
||||
INSTANCE_LIST=$(echo $EC2_DATA | jq -r '.InstanceId')
|
||||
fi
|
||||
if [[ $INSTANCE_LIST ]]; then
|
||||
for instance in $INSTANCE_LIST; do
|
||||
STATE_NAME=$(echo $EC2_DATA | jq -r --arg i "$instance" 'select(.InstanceId==$i)|.StateName')
|
||||
|
||||
+1
-1
@@ -22,7 +22,7 @@ CHECK_ALTERNATE_check102="check12"
|
||||
CHECK_ASFF_COMPLIANCE_TYPE_check12="ens-op.acc.5.aws.iam.1"
|
||||
CHECK_SERVICENAME_check12="iam"
|
||||
CHECK_RISK_check12='Unauthorized access to this critical account if password is not secure or it is disclosed in any way.'
|
||||
CHECK_REMEDIATION_check12='Enable MFA for root account. MFA is a simple best practice that adds an extra layer of protection on top of your user name and password. Recommended to use hardware keys over virtual MFA.'
|
||||
CHECK_REMEDIATION_check12='Enable MFA for all IAM users that have a console password. MFA is a simple best practice that adds an extra layer of protection on top of your user name and password. Recommended to use hardware keys over virtual MFA.'
|
||||
CHECK_DOC_check12='https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_mfa_enable_virtual.html'
|
||||
CHECK_CAF_EPIC_check12='IAM'
|
||||
|
||||
|
||||
+1
-1
@@ -23,7 +23,7 @@ CHECK_ASFF_COMPLIANCE_TYPE_check120="ens-op.acc.1.aws.iam.4"
|
||||
CHECK_SERVICENAME_check120="iam"
|
||||
CHECK_RISK_check120='AWS provides a support center that can be used for incident notification and response; as well as technical support and customer services. Create an IAM Role to allow authorized users to manage incidents with AWS Support.'
|
||||
CHECK_REMEDIATION_check120='Create an IAM role for managing incidents with AWS.'
|
||||
CHECK_DOC_check120='https://docs.aws.amazon.com/awssupport/latest/user/using-service-linked-roles-sup.html'
|
||||
CHECK_DOC_check120='https://docs.aws.amazon.com/awssupport/latest/user/accessing-support.html'
|
||||
CHECK_CAF_EPIC_check120='IAM'
|
||||
|
||||
check120(){
|
||||
|
||||
+7
-7
@@ -30,21 +30,21 @@ check122(){
|
||||
LIST_CUSTOM_POLICIES=$($AWSCLI iam list-policies --output text $PROFILE_OPT --region $REGION --scope Local --query 'Policies[*].[Arn,DefaultVersionId]' | grep -v -e '^None$' | awk -F '\t' '{print $1","$2"\n"}')
|
||||
if [[ $LIST_CUSTOM_POLICIES ]]; then
|
||||
for policy in $LIST_CUSTOM_POLICIES; do
|
||||
POLICY_ARN=$(echo $policy | awk -F ',' '{print $1}')
|
||||
POLICY_VERSION=$(echo $policy | awk -F ',' '{print $2}')
|
||||
POLICY_WITH_FULL=$($AWSCLI iam get-policy-version --output text --policy-arn $POLICY_ARN --version-id $POLICY_VERSION --query "[PolicyVersion.Document.Statement] | [] | [?Action!=null] | [?Effect == 'Allow' && Resource == '*' && Action == '*']" $PROFILE_OPT --region $REGION)
|
||||
POLICY_ARN=$(awk 'BEGIN{FS=OFS=","}{NF--; print}' <<< "${policy}")
|
||||
POLICY_VERSION=$(awk -F ',' '{print $(NF)}' <<< "${policy}")
|
||||
POLICY_WITH_FULL=$($AWSCLI iam get-policy-version --output text --policy-arn $POLICY_ARN --version-id $POLICY_VERSION --query "[PolicyVersion.Document.Statement] | [] | [?Action!=null] | [?Effect == 'Allow' && Resource == '*' && contains(Action, '*')]" $PROFILE_OPT --region $REGION)
|
||||
if [[ $POLICY_WITH_FULL ]]; then
|
||||
POLICIES_ALLOW_LIST="$POLICIES_ALLOW_LIST $POLICY_ARN"
|
||||
else
|
||||
textPass "$REGION: Policy ${policy//,/[comma]} that does not allow full \"*:*\" administrative privileges" "${REGION}" "${policy}"
|
||||
fi
|
||||
done
|
||||
if [[ $POLICIES_ALLOW_LIST ]]; then
|
||||
for policy in $POLICIES_ALLOW_LIST; do
|
||||
textFail "$REGION: Policy $policy allows \"*:*\"" "$REGION" "$policy"
|
||||
textFail "$REGION: Policy ${policy//,/[comma]} allows \"*:*\"" "${REGION}" "${policy}"
|
||||
done
|
||||
else
|
||||
textPass "$REGION: No custom policy found that allow full \"*:*\" administrative privileges" "$REGION" "$policy"
|
||||
fi
|
||||
else
|
||||
textPass "$REGION: No custom policies found" "$REGION" "$policy"
|
||||
textPass "$REGION: No custom policies found" "$REGION"
|
||||
fi
|
||||
}
|
||||
|
||||
+31
-33
@@ -27,42 +27,40 @@ CHECK_DOC_check21='https://docs.aws.amazon.com/awscloudtrail/latest/userguide/cl
|
||||
CHECK_CAF_EPIC_check21='Logging and Monitoring'
|
||||
|
||||
check21(){
|
||||
trail_count=0
|
||||
# "Ensure CloudTrail is enabled in all regions (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, HomeRegion:HomeRegion, Multiregion:IsMultiRegionTrail, ARN:TrailARN}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
|
||||
MULTIREGION_TRAIL_STATUS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $TRAIL_REGION --query 'trailList[*].IsMultiRegionTrail' --output text --trail-name-list $trail)
|
||||
if [[ "$MULTIREGION_TRAIL_STATUS" == 'False' ]];then
|
||||
textFail "$regx: Trail $trail is not enabled for all regions" "$regx" "$trail"
|
||||
else
|
||||
TRAIL_ON_OFF_STATUS=$($AWSCLI cloudtrail get-trail-status $PROFILE_OPT --region $TRAIL_REGION --name $trail --query IsLogging --output text)
|
||||
if [[ "$TRAIL_ON_OFF_STATUS" == 'False' ]];then
|
||||
textFail "$regx: Trail $trail is configured for all regions but it is OFF" "$regx" "$trail"
|
||||
else
|
||||
textPass "$regx: Trail $trail is enabled for all regions" "$regx" "$trail"
|
||||
fi
|
||||
fi
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_ARN TRAIL_HOME_REGION IS_MULTIREGION TRAIL_NAME
|
||||
do
|
||||
TRAIL_ON_OFF_STATUS=$(${AWSCLI} cloudtrail get-trail-status ${PROFILE_OPT} --region ${regx} --name ${TRAIL_ARN} --query IsLogging --output text)
|
||||
if [[ "$TRAIL_ON_OFF_STATUS" == "False" ]]
|
||||
then
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textFail "$regx: Trail ${TRAIL_NAME} is multiregion configured from region "${TRAIL_HOME_REGION}" but it is not logging" "${regx}" "${TRAIL_NAME}"
|
||||
else
|
||||
textFail "$regx: Trail ${TRAIL_NAME} is not a multiregion trail and it is not logging" "${regx}" "${TRAIL_NAME}"
|
||||
fi
|
||||
elif [[ "$TRAIL_ON_OFF_STATUS" == "True" ]]
|
||||
then
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textPass "$regx: Trail ${TRAIL_NAME} is multiregion configured from region "${TRAIL_HOME_REGION}" and it is logging" "${regx}" "${TRAIL_NAME}"
|
||||
else
|
||||
textFail "$regx: Trail ${TRAIL_NAME} is not a multiregion trail and it is logging" "${regx}" "${TRAIL_NAME}"
|
||||
fi
|
||||
fi
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textFail "$regx: No CloudTrail trails were found for the region" "${regx}" "No trails found"
|
||||
fi
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
if [[ $FILTERREGION ]]; then
|
||||
textFail "$regx: No CloudTrail trails were found in the filtered region" "$regx" "$trail"
|
||||
else
|
||||
textFail "$regx: No CloudTrail trails were found in the account" "$regx" "$trail"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
}
|
||||
|
||||
+31
-25
@@ -27,34 +27,40 @@ CHECK_DOC_check22='http://docs.aws.amazon.com/awscloudtrail/latest/userguide/clo
|
||||
CHECK_CAF_EPIC_check22='Logging and Monitoring'
|
||||
|
||||
check22(){
|
||||
trail_count=0
|
||||
# "Ensure CloudTrail log file validation is enabled (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
continue
|
||||
for regx in $REGIONS
|
||||
do
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, HomeRegion:HomeRegion, Multiregion:IsMultiRegionTrail, LogFileValidation:LogFileValidationEnabled}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
|
||||
LOGFILEVALIDATION_TRAIL_STATUS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $TRAIL_REGION --query 'trailList[*].LogFileValidationEnabled' --output text --trail-name-list $trail)
|
||||
if [[ "$LOGFILEVALIDATION_TRAIL_STATUS" == 'False' ]];then
|
||||
textFail "$regx: Trail $trail log file validation disabled" "$regx" "$trail"
|
||||
else
|
||||
textPass "$regx: Trail $trail log file validation enabled" "$regx" "$trail"
|
||||
fi
|
||||
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_HOME_REGION LOG_FILE_VALIDATION IS_MULTIREGION TRAIL_NAME
|
||||
do
|
||||
if [[ "${LOG_FILE_VALIDATION}" == "True" ]]
|
||||
then
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textPass "$regx: Multiregion trail ${TRAIL_NAME} configured from region ${TRAIL_HOME_REGION} log file validation enabled" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textPass "$regx: Single region trail ${TRAIL_NAME} log file validation enabled" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
else
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textFail "$regx: Multiregion trail ${TRAIL_NAME} configured from region ${TRAIL_HOME_REGION} log file validation disabled" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Single region trail ${TRAIL_NAME} log file validation disabled" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
fi
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textPass "$regx: No trails found in the region" "$regx"
|
||||
fi
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
textFail "$REGION: No CloudTrail trails were found in the account" "$REGION" "$trail"
|
||||
fi
|
||||
}
|
||||
|
||||
+53
-55
@@ -27,68 +27,66 @@ CHECK_DOC_check23='https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_po
|
||||
CHECK_CAF_EPIC_check23='Logging and Monitoring'
|
||||
|
||||
check23(){
|
||||
trail_count=0
|
||||
# "Ensure the S3 bucket CloudTrail logs to is not publicly accessible (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
for regx in $REGIONS
|
||||
do
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, HomeRegion:HomeRegion, Multiregion:IsMultiRegionTrail, BucketName:S3BucketName}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_BUCKET TRAIL_HOME_REGION IS_MULTIREGION TRAIL_NAME
|
||||
do
|
||||
if [[ ! "${TRAIL_BUCKET}" ]]
|
||||
then
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textFail "$regx: Multiregion trail ${TRAIL_NAME} configured from region ${TRAIL_HOME_REGION} does not publish to S3" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Single region trail ${TRAIL_NAME} does not publish to S3" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
continue
|
||||
fi
|
||||
|
||||
CLOUDTRAILBUCKET=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $TRAIL_REGION --query 'trailList[*].[S3BucketName]' --output text --trail-name-list $trail)
|
||||
if [[ -z $CLOUDTRAILBUCKET ]]; then
|
||||
textFail "Trail $trail in $TRAIL_REGION does not publish to S3"
|
||||
continue
|
||||
fi
|
||||
BUCKET_LOCATION=$($AWSCLI s3api get-bucket-location $PROFILE_OPT --region $regx --bucket $TRAIL_BUCKET --output text 2>&1)
|
||||
if [[ $(echo "$BUCKET_LOCATION" | grep AccessDenied) ]]
|
||||
then
|
||||
textInfo "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} Access Denied getting bucket location for bucket $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
continue
|
||||
fi
|
||||
if [[ $(echo "$BUCKET_LOCATION" | grep NoSuchBucket) ]]
|
||||
then
|
||||
textInfo "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} S3 logging bucket $TRAIL_BUCKET does not exist" "$regx" "$TRAIL_NAME"
|
||||
continue
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "None" ]]; then
|
||||
BUCKET_LOCATION="us-east-1"
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "EU" ]]; then
|
||||
BUCKET_LOCATION="eu-west-1"
|
||||
fi
|
||||
|
||||
CLOUDTRAIL_ACCOUNT_ID=$(echo $trail | awk -F: '{ print $5 }')
|
||||
if [ "$CLOUDTRAIL_ACCOUNT_ID" != "$ACCOUNT_NUM" ]; then
|
||||
textInfo "Trail $trail in $TRAIL_REGION S3 logging bucket $CLOUDTRAILBUCKET is not in current account"
|
||||
continue
|
||||
fi
|
||||
CLOUDTRAILBUCKET_HASALLPERMISIONS=$($AWSCLI s3api get-bucket-acl --bucket $TRAIL_BUCKET $PROFILE_OPT --region $BUCKET_LOCATION --query 'Grants[?Grantee.URI==`http://acs.amazonaws.com/groups/global/AllUsers`]' --output text 2>&1)
|
||||
if [[ $(echo "$CLOUDTRAILBUCKET_HASALLPERMISIONS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} Access Denied getting bucket acl for bucket $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
continue
|
||||
fi
|
||||
|
||||
#
|
||||
# LOCATION - requests referencing buckets created after March 20, 2019
|
||||
# must be made to S3 endpoints in the same region as the bucket was
|
||||
# created.
|
||||
#
|
||||
BUCKET_LOCATION=$($AWSCLI s3api get-bucket-location $PROFILE_OPT --region $regx --bucket $CLOUDTRAILBUCKET --output text 2>&1)
|
||||
if [[ $(echo "$BUCKET_LOCATION" | grep AccessDenied) ]]; then
|
||||
textFail "Trail $trail in $TRAIL_REGION Access Denied getting bucket location for $CLOUDTRAILBUCKET"
|
||||
continue
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "None" ]]; then
|
||||
BUCKET_LOCATION="us-east-1"
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "EU" ]]; then
|
||||
BUCKET_LOCATION="eu-west-1"
|
||||
fi
|
||||
|
||||
CLOUDTRAILBUCKET_HASALLPERMISIONS=$($AWSCLI s3api get-bucket-acl --bucket $CLOUDTRAILBUCKET $PROFILE_OPT --region $BUCKET_LOCATION --query 'Grants[?Grantee.URI==`http://acs.amazonaws.com/groups/global/AllUsers`]' --output text 2>&1)
|
||||
if [[ $(echo "$CLOUDTRAILBUCKET_HASALLPERMISIONS" | grep AccessDenied) ]]; then
|
||||
textInfo "Trail $trail in $TRAIL_REGION Access Denied getting bucket acl for $CLOUDTRAILBUCKET"
|
||||
continue
|
||||
fi
|
||||
|
||||
if [[ -z $CLOUDTRAILBUCKET_HASALLPERMISIONS ]]; then
|
||||
textPass "Trail $trail in $TRAIL_REGION S3 logging bucket $CLOUDTRAILBUCKET is not publicly accessible"
|
||||
else
|
||||
textFail "Trail $trail in $TRAIL_REGION S3 logging bucket $CLOUDTRAILBUCKET is publicly accessible"
|
||||
fi
|
||||
if [[ ! $CLOUDTRAILBUCKET_HASALLPERMISIONS ]]; then
|
||||
textPass "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} S3 logging bucket $TRAIL_BUCKET is not publicly accessible" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} S3 logging bucket $TRAIL_BUCKET is publicly accessible" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textPass "$regx: No trails found in the region" "$regx"
|
||||
fi
|
||||
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
textFail "$REGION: No CloudTrail trails were found in the account" "$REGION" "$trail"
|
||||
fi
|
||||
|
||||
}
|
||||
|
||||
+22
-28
@@ -27,40 +27,34 @@ CHECK_DOC_check24='https://docs.aws.amazon.com/awscloudtrail/latest/userguide/se
|
||||
CHECK_CAF_EPIC_check24='Logging and Monitoring'
|
||||
|
||||
check24(){
|
||||
trail_count=0
|
||||
# "Ensure CloudTrail trails are integrated with CloudWatch Logs (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, HomeRegion:HomeRegion, ARN:TrailARN}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
|
||||
LATESTDELIVERY_TIMESTAMP=$($AWSCLI cloudtrail get-trail-status --name $trail $PROFILE_OPT --region $TRAIL_REGION --query 'LatestCloudWatchLogsDeliveryTime' --output text|grep -v None)
|
||||
if [[ ! $LATESTDELIVERY_TIMESTAMP ]];then
|
||||
textFail "$TRAIL_REGION: $trail trail is not logging in the last 24h or not configured (it is in $TRAIL_REGION)" "$TRAIL_REGION" "$trail"
|
||||
else
|
||||
LATESTDELIVERY_DATE=$(timestamp_to_date $LATESTDELIVERY_TIMESTAMP)
|
||||
HOWOLDER=$(how_older_from_today $LATESTDELIVERY_DATE)
|
||||
if [ $HOWOLDER -gt "1" ];then
|
||||
textFail "$TRAIL_REGION: $trail trail is not logging in the last 24h or not configured" "$TRAIL_REGION" "$trail"
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_ARN TRAIL_HOME_REGION TRAIL_NAME
|
||||
do
|
||||
LATESTDELIVERY_TIMESTAMP=$(${AWSCLI} cloudtrail get-trail-status ${PROFILE_OPT} --region ${regx} --name ${TRAIL_ARN} --query LatestCloudWatchLogsDeliveryTime --output text|grep -v None)
|
||||
if [[ ! $LATESTDELIVERY_TIMESTAMP ]];then
|
||||
textFail "$regx: $TRAIL_NAME trail is not logging in the last 24h or not configured (its home region is $TRAIL_HOME_REGION)" "$regx" "$trail"
|
||||
else
|
||||
textPass "$TRAIL_REGION: $trail trail has been logging during the last 24h" "$TRAIL_REGION" "$trail"
|
||||
LATESTDELIVERY_DATE=$(timestamp_to_date $LATESTDELIVERY_TIMESTAMP)
|
||||
HOWOLDER=$(how_older_from_today $LATESTDELIVERY_DATE)
|
||||
if [ $HOWOLDER -gt "1" ];then
|
||||
textFail "$regx: $TRAIL_NAME trail is not logging in the last 24h or not configured" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textPass "$regx: $TRAIL_NAME trail has been logging during the last 24h" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textFail "$regx: No CloudTrail trails were found for the region" "${regx}" "No trails found"
|
||||
fi
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
textFail "$REGION: No CloudTrail trails were found in the account" "$REGION" "$trail"
|
||||
fi
|
||||
}
|
||||
|
||||
+1
-1
@@ -31,7 +31,7 @@ check25(){
|
||||
CHECK_AWSCONFIG_RECORDING=$($AWSCLI configservice describe-configuration-recorder-status $PROFILE_OPT --region $regx --query 'ConfigurationRecordersStatus[*].recording' --output text 2>&1)
|
||||
CHECK_AWSCONFIG_STATUS=$($AWSCLI configservice describe-configuration-recorder-status $PROFILE_OPT --region $regx --query 'ConfigurationRecordersStatus[*].lastStatus' --output text 2>&1)
|
||||
if [[ $(echo "$CHECK_AWSCONFIG_STATUS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe configuration recorder status" "$regx" "recorder"
|
||||
textInfo "$regx: Access Denied trying to describe configuration recorder status" "$regx" "recorder"
|
||||
continue
|
||||
fi
|
||||
if [[ $CHECK_AWSCONFIG_RECORDING == "True" ]]; then
|
||||
|
||||
+48
-54
@@ -26,68 +26,62 @@ CHECK_DOC_check26='https://docs.aws.amazon.com/AmazonS3/latest/dev/security-best
|
||||
CHECK_CAF_EPIC_check26='Logging and Monitoring'
|
||||
|
||||
check26(){
|
||||
trail_count=0
|
||||
# "Ensure S3 bucket access logging is enabled on the CloudTrail S3 bucket (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
|
||||
for regx in $REGIONS
|
||||
do
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, HomeRegion:HomeRegion, Multiregion:IsMultiRegionTrail, BucketName:S3BucketName}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_BUCKET TRAIL_HOME_REGION IS_MULTIREGION TRAIL_NAME
|
||||
do
|
||||
if [[ ! "${TRAIL_BUCKET}" ]]
|
||||
then
|
||||
if [[ "${IS_MULTIREGION}" == "True" ]]
|
||||
then
|
||||
textFail "$regx: Multiregion trail ${TRAIL_NAME} configured from region ${TRAIL_HOME_REGION} does not publish to S3" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Single region trail ${TRAIL_NAME} does not publish to S3" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
continue
|
||||
fi
|
||||
|
||||
CLOUDTRAILBUCKET=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $TRAIL_REGION --query 'trailList[*].[S3BucketName]' --output text --trail-name-list $trail)
|
||||
if [[ -z $CLOUDTRAILBUCKET ]]; then
|
||||
textFail "$regx: Trail $trail does not publish to S3" "$TRAIL_REGION" "$trail"
|
||||
continue
|
||||
fi
|
||||
BUCKET_LOCATION=$($AWSCLI s3api get-bucket-location $PROFILE_OPT --region $regx --bucket $TRAIL_BUCKET --output text 2>&1)
|
||||
if [[ $(echo "$BUCKET_LOCATION" | grep AccessDenied) ]]
|
||||
then
|
||||
textInfo "$regx: Trail ${TRAIL_NAME} with home region ${TRAIL_HOME_REGION} Access Denied getting bucket location for bucket $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
continue
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "None" ]]; then
|
||||
BUCKET_LOCATION="us-east-1"
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "EU" ]]; then
|
||||
BUCKET_LOCATION="eu-west-1"
|
||||
fi
|
||||
|
||||
CLOUDTRAIL_ACCOUNT_ID=$(echo $trail | awk -F: '{ print $5 }')
|
||||
if [ "$CLOUDTRAIL_ACCOUNT_ID" != "$ACCOUNT_NUM" ]; then
|
||||
textInfo "$regx: Trail $trail S3 logging bucket $CLOUDTRAILBUCKET is not in current account" "$TRAIL_REGION" "$trail"
|
||||
continue
|
||||
fi
|
||||
CLOUDTRAILBUCKET_LOGENABLED=$($AWSCLI s3api get-bucket-logging --bucket $TRAIL_BUCKET $PROFILE_OPT --region $BUCKET_LOCATION --query 'LoggingEnabled.TargetBucket' --output text 2>&1)
|
||||
if [[ $(echo "$CLOUDTRAILBUCKET_LOGENABLED" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Trail $TRAIL_NAME Access Denied getting bucket logging for $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
continue
|
||||
fi
|
||||
|
||||
#
|
||||
# LOCATION - requests referencing buckets created after March 20, 2019
|
||||
# must be made to S3 endpoints in the same region as the bucket was
|
||||
# created.
|
||||
#
|
||||
BUCKET_LOCATION=$($AWSCLI s3api get-bucket-location $PROFILE_OPT --region $regx --bucket $CLOUDTRAILBUCKET --output text 2>&1)
|
||||
if [[ $(echo "$BUCKET_LOCATION" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Trail $trail Access Denied getting bucket location for $CLOUDTRAILBUCKET" "$TRAIL_REGION" "$trail"
|
||||
continue
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "None" ]]; then
|
||||
BUCKET_LOCATION="us-east-1"
|
||||
fi
|
||||
if [[ $BUCKET_LOCATION == "EU" ]]; then
|
||||
BUCKET_LOCATION="eu-west-1"
|
||||
fi
|
||||
if [[ $CLOUDTRAILBUCKET_LOGENABLED != "None" ]]; then
|
||||
textPass "$regx: Trail $TRAIL_NAME S3 bucket access logging is enabled for $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Trail $TRAIL_NAME S3 bucket access logging is not enabled for $TRAIL_BUCKET" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
|
||||
CLOUDTRAILBUCKET_LOGENABLED=$($AWSCLI s3api get-bucket-logging --bucket $CLOUDTRAILBUCKET $PROFILE_OPT --region $BUCKET_LOCATION --query 'LoggingEnabled.TargetBucket' --output text 2>&1)
|
||||
if [[ $(echo "$CLOUDTRAILBUCKET_LOGENABLED" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Trail $trail Access Denied getting bucket logging for $CLOUDTRAILBUCKET" "$TRAIL_REGION" "$trail"
|
||||
continue
|
||||
fi
|
||||
|
||||
if [[ $CLOUDTRAILBUCKET_LOGENABLED != "None" ]]; then
|
||||
textPass "$regx: Trail $trail S3 bucket access logging is enabled for $CLOUDTRAILBUCKET" "$TRAIL_REGION" "$trail"
|
||||
else
|
||||
textFail "$regx: Trail $trail S3 bucket access logging is not enabled for $CLOUDTRAILBUCKET" "$TRAIL_REGION" "$trail"
|
||||
fi
|
||||
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textPass "$regx: No trails found in the region" "$regx"
|
||||
fi
|
||||
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
textFail "$REGION: No CloudTrail trails were found in the account" "$REGION" "$trail"
|
||||
fi
|
||||
}
|
||||
|
||||
+18
-23
@@ -27,33 +27,28 @@ CHECK_DOC_check27='https://docs.aws.amazon.com/awscloudtrail/latest/userguide/en
|
||||
CHECK_CAF_EPIC_check27='Logging and Monitoring'
|
||||
|
||||
check27(){
|
||||
trail_count=0
|
||||
# "Ensure CloudTrail logs are encrypted at rest using KMS CMKs (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
TRAILS_AND_REGIONS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:TrailARN, HomeRegion:HomeRegion}' --output text 2>&1 | tr " " ',')
|
||||
if [[ $(echo "$TRAILS_AND_REGIONS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe trails" "$regx" "$trail"
|
||||
TRAILS_DETAILS=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $regx --query 'trailList[*].{Name:Name, KeyID:KmsKeyId}' --output text 2>&1)
|
||||
if [[ $(echo "$TRAILS_DETAILS" | grep AccessDenied) ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe trails" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $TRAILS_AND_REGIONS ]]; then
|
||||
for reg_trail in $TRAILS_AND_REGIONS; do
|
||||
TRAIL_REGION=$(echo $reg_trail | cut -d',' -f1)
|
||||
if [ $TRAIL_REGION != $regx ]; then # Only report trails once in home region
|
||||
continue
|
||||
fi
|
||||
trail=$(echo $reg_trail | cut -d',' -f2)
|
||||
trail_count=$((trail_count + 1))
|
||||
|
||||
KMSKEYID=$($AWSCLI cloudtrail describe-trails $PROFILE_OPT --region $TRAIL_REGION --query 'trailList[*].KmsKeyId' --output text --trail-name-list $trail)
|
||||
if [[ "$KMSKEYID" ]];then
|
||||
textPass "$regx: Trail $trail has encryption enabled" "$regx" "$trail"
|
||||
else
|
||||
textFail "$regx: Trail $trail has encryption disabled" "$regx" "$trail"
|
||||
fi
|
||||
if [[ $TRAILS_DETAILS ]]
|
||||
then
|
||||
for REGION_TRAIL in "${TRAILS_DETAILS}"
|
||||
do
|
||||
while read -r TRAIL_KEY_ID TRAIL_NAME
|
||||
do
|
||||
if [[ "${TRAIL_KEY_ID}" != "None" ]]
|
||||
then
|
||||
textPass "$regx: Trail $TRAIL_NAME has encryption enabled" "$regx" "$TRAIL_NAME"
|
||||
else
|
||||
textFail "$regx: Trail $TRAIL_NAME has encryption disabled" "$regx" "$TRAIL_NAME"
|
||||
fi
|
||||
done <<< "${REGION_TRAIL}"
|
||||
done
|
||||
else
|
||||
textPass "$regx: No CloudTrail trails were found for the region" "${regx}" "No trails found"
|
||||
fi
|
||||
done
|
||||
if [[ $trail_count == 0 ]]; then
|
||||
textFail "$REGION: No CloudTrail trails were found in the account" "$REGION" "$trail"
|
||||
fi
|
||||
}
|
||||
|
||||
+3
-3
@@ -30,7 +30,7 @@ check28(){
|
||||
for regx in $REGIONS; do
|
||||
CHECK_KMS_KEYLIST=$($AWSCLI kms list-keys $PROFILE_OPT --region $regx --output text --query 'Keys[*].KeyId' --output text 2>&1)
|
||||
if [[ $(echo "$CHECK_KMS_KEYLIST" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to list keys" "$regx" "$key"
|
||||
textInfo "$regx: Access Denied trying to list keys" "$regx" "$key"
|
||||
continue
|
||||
fi
|
||||
if [[ $CHECK_KMS_KEYLIST ]]; then
|
||||
@@ -38,7 +38,7 @@ check28(){
|
||||
for key in $CHECK_KMS_KEYLIST; do
|
||||
KMSDETAILS=$($AWSCLI kms describe-key --key-id $key $PROFILE_OPT --region $regx --query 'KeyMetadata.{key:KeyId,man:KeyManager,origin:Origin,spec:CustomerMasterKeySpec,state:KeyState}' --output text 2>&1 | grep SYMMETRIC)
|
||||
if [[ $(echo "$KMSDETAILS" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Key $key Access Denied describing key" "$regx" "$key"
|
||||
textInfo "$regx: Access Denied describing key $key" "$regx" "$key"
|
||||
continue
|
||||
fi
|
||||
|
||||
@@ -60,7 +60,7 @@ check28(){
|
||||
else
|
||||
CHECK_KMS_KEY_ROTATION=$($AWSCLI kms get-key-rotation-status --key-id $key $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$CHECK_KMS_KEY_ROTATION" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Key $key Access Denied getting key rotation status" "$regx" "$key"
|
||||
textInfo "$regx: Access Denied getting key rotation status for $key " "$regx" "$key"
|
||||
continue
|
||||
fi
|
||||
if [[ "$CHECK_KMS_KEY_ROTATION" == "True" ]];then
|
||||
|
||||
+4
-4
@@ -30,14 +30,14 @@ check29(){
|
||||
# "Ensure VPC Flow Logging is Enabled in all VPCs (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
AVAILABLE_VPC=$($AWSCLI ec2 describe-vpcs $PROFILE_OPT --region $regx --query 'Vpcs[?State==`available`].VpcId' --output text 2>&1)
|
||||
if [[ $(echo "$AVAILABLE_VPC" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: Access Denied trying to describe VPCs" "$regx" "$vpcx"
|
||||
if [[ $(echo "$AVAILABLE_VPC" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe VPCs" "$regx" "$vpcx"
|
||||
continue
|
||||
fi
|
||||
for vpcx in $AVAILABLE_VPC; do
|
||||
CHECK_FL=$($AWSCLI ec2 describe-flow-logs $PROFILE_OPT --region $regx --filter Name="resource-id",Values="${vpcx}" --query 'FlowLogs[?FlowLogStatus==`ACTIVE`].FlowLogId' --output text 2>&1)
|
||||
if [[ $(echo "$CHECK_FL" | grep AccessDenied) ]]; then
|
||||
textFail "$regx: VPC $vpcx Access Denied trying to describe flow logs" "$regx" "$vpcx"
|
||||
if [[ $(echo "$CHECK_FL" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe flow logs in VPC $vpcx" "$regx" "$vpcx"
|
||||
continue
|
||||
fi
|
||||
if [[ $CHECK_FL ]]; then
|
||||
|
||||
+5
-1
@@ -52,5 +52,9 @@ CHECK_DOC_check33='https://docs.aws.amazon.com/awscloudtrail/latest/userguide/cl
|
||||
CHECK_CAF_EPIC_check33='Logging and Monitoring'
|
||||
|
||||
check33(){
|
||||
check3x '\$\.userIdentity\.type\s*=\s*"Root".+\$\.userIdentity\.invokedBy NOT EXISTS.+\$\.eventType\s*!=\s*"AwsServiceEvent"'
|
||||
if [[ "${REGION}" == "us-gov-west-1" || "${REGION}" == "us-gov-east-1" ]]; then
|
||||
textInfo "${REGION}: This is an AWS GovCloud account and there is no root account to perform checks."
|
||||
else
|
||||
check3x '\$\.userIdentity\.type\s*=\s*"Root".+\$\.userIdentity\.invokedBy NOT EXISTS.+\$\.eventType\s*!=\s*"AwsServiceEvent"'
|
||||
fi
|
||||
}
|
||||
|
||||
+5
-1
@@ -29,7 +29,11 @@ CHECK_CAF_EPIC_check41='Infrastructure Security'
|
||||
check41(){
|
||||
# "Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to port 22 (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort<=`22` && ToPort>=`22`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$("${AWSCLI}" ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort<=`22` && ToPort>=`22`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`)) && (IpProtocol==`tcp`)]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region "${regx}" --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0" "$regx" "$SG"
|
||||
|
||||
+5
-1
@@ -29,7 +29,11 @@ CHECK_CAF_EPIC_check42='Infrastructure Security'
|
||||
check42(){
|
||||
# "Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to port 3389 (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort<=`3389` && ToPort>=`3389`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$("${AWSCLI}" ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort<=`3389` && ToPort>=`3389`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`)) && (IpProtocol==`tcp`) ]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region "${regx}" --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0" "$regx" "$SG"
|
||||
|
||||
+5
-1
@@ -29,7 +29,11 @@ CHECK_CAF_EPIC_check43='Infrastructure Security'
|
||||
check43(){
|
||||
# "Ensure the default security group of every VPC restricts all traffic (Scored)"
|
||||
for regx in $REGIONS; do
|
||||
CHECK_SGDEFAULT_IDS=$($AWSCLI ec2 describe-security-groups $PROFILE_OPT --region $regx --filters Name=group-name,Values='default' --query 'SecurityGroups[*].GroupId[]' --output text)
|
||||
CHECK_SGDEFAULT_IDS=$($AWSCLI ec2 describe-security-groups $PROFILE_OPT --region $regx --filters Name=group-name,Values='default' --query 'SecurityGroups[*].GroupId[]' --output text 2>&1)
|
||||
if [[ $(echo "$CHECK_SGDEFAULT_IDS" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
for CHECK_SGDEFAULT_ID in $CHECK_SGDEFAULT_IDS; do
|
||||
CHECK_SGDEFAULT_ID_OPEN=$($AWSCLI ec2 describe-security-groups $PROFILE_OPT --region $regx --group-ids $CHECK_SGDEFAULT_ID --query 'SecurityGroups[*].{IpPermissions:IpPermissions,IpPermissionsEgress:IpPermissionsEgress,GroupId:GroupId}' --output text |egrep '\s0.0.0.0|\:\:\/0')
|
||||
if [[ $CHECK_SGDEFAULT_ID_OPEN ]];then
|
||||
|
||||
+5
-1
@@ -28,7 +28,11 @@ CHECK_CAF_EPIC_check44='Infrastructure Security'
|
||||
check44(){
|
||||
# "Ensure routing tables for VPC peering are \"least access\" (Not Scored)"
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_VPCS_PEERING_CONNECTIONS=$($AWSCLI ec2 describe-vpc-peering-connections --output text $PROFILE_OPT --region $regx --query 'VpcPeeringConnections[*].VpcPeeringConnectionId'| sort | paste -s -d" " -)
|
||||
LIST_OF_VPCS_PEERING_CONNECTIONS=$($AWSCLI ec2 describe-vpc-peering-connections --output text $PROFILE_OPT --region $regx --query 'VpcPeeringConnections[*].VpcPeeringConnectionId' 2>&1| sort | paste -s -d" " - )
|
||||
if [[ $(echo "$LIST_OF_VPCS_PEERING_CONNECTIONS" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe vpc peering connections" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_VPCS_PEERING_CONNECTIONS ]];then
|
||||
textInfo "$regx: $LIST_OF_VPCS_PEERING_CONNECTIONS - review routing tables" "$regx" "$LIST_OF_VPCS_PEERING_CONNECTIONS"
|
||||
#LIST_OF_VPCS=$($AWSCLI ec2 describe-vpcs $PROFILE_OPT --region $regx --query 'Vpcs[*].VpcId' --output text)
|
||||
|
||||
+5
-1
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_check45='Infrastructure Security'
|
||||
|
||||
check45(){
|
||||
for regx in $REGIONS; do
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?(((!PortRange) || (PortRange.From<=`22` && PortRange.To>=`22`)) && ((CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`)))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text)
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?(((!PortRange) || (PortRange.From<=`22` && PortRange.To>=`22`)) && ((CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`)))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$NACL_LIST" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe vpc network acls" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $NACL_LIST ]];then
|
||||
for NACL in $NACL_LIST;do
|
||||
textInfo "$regx: Found Network ACL: $NACL open to 0.0.0.0/0 for SSH port 22" "$regx" "$NACL"
|
||||
|
||||
+5
-1
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_check46='Infrastructure Security'
|
||||
|
||||
check46(){
|
||||
for regx in $REGIONS; do
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?(((!PortRange) || (PortRange.From<=`3389` && PortRange.To>=`3389`)) && ((CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`)))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text)
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?(((!PortRange) || (PortRange.From<=`3389` && PortRange.To>=`3389`)) && ((CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`)))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$NACL_LIST" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe vpc network acls" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $NACL_LIST ]];then
|
||||
for NACL in $NACL_LIST;do
|
||||
textInfo "$regx: Found Network ACL: $NACL open to 0.0.0.0/0 for Microsoft RDP port 3389" "$regx" "$NACL"
|
||||
|
||||
+30
-25
@@ -21,8 +21,8 @@ CHECK_ALTERNATE_check71="extra71"
|
||||
CHECK_ALTERNATE_check701="extra71"
|
||||
CHECK_ASFF_COMPLIANCE_TYPE_extra71="ens-op.exp.10.aws.trail.2"
|
||||
CHECK_SERVICENAME_extra71="iam"
|
||||
CHECK_RISK_extra71='Policy "may" allow Anonymous users to perform actions.'
|
||||
CHECK_REMEDIATION_extra71='Ensure this repository and its contents should be publicly accessible.'
|
||||
CHECK_RISK_extra71='Any user with AdministratorAccess is allowed to perform any action on an AWS account, so it needs to have a multi factor authentication enabled to avoid impersonation through a potential credentials leak'
|
||||
CHECK_REMEDIATION_extra71='Enable MFA for users belonging to groups with AdministratorAccess policies'
|
||||
CHECK_DOC_extra71='https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_mfa_enable_virtual.html'
|
||||
CHECK_CAF_EPIC_extra71='Infrastructure Security'
|
||||
|
||||
@@ -30,27 +30,32 @@ extra71(){
|
||||
# "Ensure users of groups with AdministratorAccess policy have MFA tokens enabled "
|
||||
ADMIN_GROUPS=''
|
||||
AWS_GROUPS=$($AWSCLI $PROFILE_OPT iam list-groups --output text --region $REGION --query 'Groups[].GroupName')
|
||||
for grp in $AWS_GROUPS; do
|
||||
# aws --profile onlinetraining iam list-attached-group-policies --group-name Administrators --query 'AttachedPolicies[].PolicyArn' | grep 'arn:aws:iam::aws:policy/AdministratorAccess'
|
||||
# list-attached-group-policies
|
||||
CHECK_ADMIN_GROUP=$($AWSCLI $PROFILE_OPT --region $REGION iam list-attached-group-policies --group-name $grp --output json --query 'AttachedPolicies[].PolicyArn' | grep "arn:${AWS_PARTITION}:iam::aws:policy/AdministratorAccess")
|
||||
if [[ $CHECK_ADMIN_GROUP ]]; then
|
||||
ADMIN_GROUPS="$ADMIN_GROUPS $grp"
|
||||
textInfo "$REGION: $grp group provides administrative access" "$REGION" "$grp"
|
||||
ADMIN_USERS=$($AWSCLI $PROFILE_OPT iam get-group --region $REGION --group-name $grp --output json --query 'Users[].UserName' | grep '"' | cut -d'"' -f2 )
|
||||
for auser in $ADMIN_USERS; do
|
||||
# users in group are Administrators
|
||||
# users
|
||||
# check for user MFA device in credential report
|
||||
USER_MFA_ENABLED=$( cat $TEMP_REPORT_FILE | grep "^$auser," | cut -d',' -f8)
|
||||
if [[ "true" == $USER_MFA_ENABLED ]]; then
|
||||
textPass "$REGION: $auser / MFA Enabled / admin via group $grp" "$REGION" "$grp"
|
||||
else
|
||||
textFail "$REGION: $auser / MFA DISABLED / admin via group $grp" "$REGION" "$grp"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$REGION: $grp group provides non-administrative access" "$REGION" "$grp"
|
||||
fi
|
||||
done
|
||||
if [[ ${AWS_GROUPS} ]]
|
||||
then
|
||||
for grp in $AWS_GROUPS; do
|
||||
# aws --profile onlinetraining iam list-attached-group-policies --group-name Administrators --query 'AttachedPolicies[].PolicyArn' | grep 'arn:aws:iam::aws:policy/AdministratorAccess'
|
||||
# list-attached-group-policies
|
||||
CHECK_ADMIN_GROUP=$($AWSCLI $PROFILE_OPT --region $REGION iam list-attached-group-policies --group-name $grp --output json --query 'AttachedPolicies[].PolicyArn' | grep "arn:${AWS_PARTITION}:iam::aws:policy/AdministratorAccess")
|
||||
if [[ $CHECK_ADMIN_GROUP ]]; then
|
||||
ADMIN_GROUPS="$ADMIN_GROUPS $grp"
|
||||
textInfo "$REGION: $grp group provides administrative access" "$REGION" "$grp"
|
||||
ADMIN_USERS=$($AWSCLI $PROFILE_OPT iam get-group --region $REGION --group-name $grp --output json --query 'Users[].UserName' | grep '"' | cut -d'"' -f2 )
|
||||
for auser in $ADMIN_USERS; do
|
||||
# users in group are Administrators
|
||||
# users
|
||||
# check for user MFA device in credential report
|
||||
USER_MFA_ENABLED=$( cat $TEMP_REPORT_FILE | grep "^$auser," | cut -d',' -f8)
|
||||
if [[ "true" == $USER_MFA_ENABLED ]]; then
|
||||
textPass "$REGION: $auser / MFA Enabled / admin via group $grp" "$REGION" "$grp"
|
||||
else
|
||||
textFail "$REGION: $auser / MFA DISABLED / admin via group $grp" "$REGION" "$grp"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$REGION: $grp group provides non-administrative access" "$REGION" "$grp"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textPass "$REGION: There is no IAM groups" "$REGION"
|
||||
fi
|
||||
}
|
||||
|
||||
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_extra710='Infrastructure Security'
|
||||
extra710(){
|
||||
# "Check for internet facing EC2 Instances "
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_PUBLIC_INSTANCES=$($AWSCLI ec2 describe-instances $PROFILE_OPT --region $regx --query 'Reservations[*].Instances[?PublicIpAddress].[InstanceId,PublicIpAddress]' --output text)
|
||||
LIST_OF_PUBLIC_INSTANCES=$($AWSCLI ec2 describe-instances $PROFILE_OPT --region $regx --query 'Reservations[*].Instances[?PublicIpAddress].[InstanceId,PublicIpAddress]' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_PUBLIC_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_PUBLIC_INSTANCES ]];then
|
||||
while read -r instance;do
|
||||
INSTANCE_ID=$(echo $instance | awk '{ print $1; }')
|
||||
|
||||
@@ -68,8 +68,7 @@ extra7100(){
|
||||
|
||||
done
|
||||
if [[ $PERMISSIVE_POLICIES_LIST ]]; then
|
||||
textInfo "STS AssumeRole Policies should only include the complete ARNs for the Roles that the user needs"
|
||||
textInfo "Learn more: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use_permissions-to-switch.html#roles-usingrole-createpolicy"
|
||||
textInfo "STS AssumeRole Policies should only include the complete ARNs for the Roles that the user needs. Learn more: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use_permissions-to-switch.html#roles-usingrole-createpolicy" "$REGION"
|
||||
for policy in $PERMISSIVE_POLICIES_LIST; do
|
||||
textFail "$REGION: Policy $policy allows permissive STS Role assumption" "$REGION" "$policy"
|
||||
done
|
||||
|
||||
+17
-9
@@ -25,19 +25,27 @@ CHECK_DOC_extra7101='https://docs.aws.amazon.com/elasticsearch-service/latest/de
|
||||
CHECK_CAF_EPIC_extra7101='Logging and Monitoring'
|
||||
|
||||
extra7101(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_DOMAINS=$($AWSCLI es list-domain-names $PROFILE_OPT --region $regx --query DomainNames --output text)
|
||||
if [[ $LIST_OF_DOMAINS ]]; then
|
||||
for domain in $LIST_OF_DOMAINS;do
|
||||
AUDIT_LOGS_ENABLED=$($AWSCLI es describe-elasticsearch-domain-config --domain-name $domain $PROFILE_OPT --region $regx --query DomainConfig.LogPublishingOptions.Options.AUDIT_LOGS.Enabled --output text |grep -v ^None|grep -v ^False)
|
||||
if [[ $AUDIT_LOGS_ENABLED ]];then
|
||||
textPass "$regx: Amazon ES domain $domain AUDIT_LOGS enabled" "$regx" "$domain"
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_OF_DOMAINS=$("${AWSCLI}" es list-domain-names ${PROFILE_OPT} --region "${regx}" --query 'DomainNames[].DomainName' --output text 2>&1)
|
||||
if [[ $(echo "${LIST_OF_DOMAINS}" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "${regx}: Access Denied trying to list domain names" "${regx}"
|
||||
continue
|
||||
fi
|
||||
if [[ "${LIST_OF_DOMAINS}" ]]; then
|
||||
for domain in ${LIST_OF_DOMAINS}; do
|
||||
AUDIT_LOGS_ENABLED=$("${AWSCLI}" es describe-elasticsearch-domain-config --domain-name "${domain}" ${PROFILE_OPT} --region "${regx}" --query 'DomainConfig.LogPublishingOptions.Options.AUDIT_LOGS.Enabled' --output text 2>&1)
|
||||
if [[ $(echo "${AUDIT_LOGS_ENABLED}" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "${regx}: Access Denied trying to get ES domain config for ${domain}" "${regx}"
|
||||
continue
|
||||
fi
|
||||
if [[ $(tr '[:upper:]' '[:lower:]' <<< "${AUDIT_LOGS_ENABLED}") == "true" ]]; then
|
||||
textPass "${regx}: Amazon ES domain ${domain} AUDIT_LOGS enabled" "${regx}" "${domain}"
|
||||
else
|
||||
textFail "$regx: Amazon ES domain $domain AUDIT_LOGS disabled!" "$regx" "$domain"
|
||||
textFail "${regx}: Amazon ES domain ${domain} AUDIT_LOGS disabled!" "${regx}" "${domain}"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: No Amazon ES domain found" "$regx"
|
||||
textInfo "${regx}: No Amazon ES domain found" "${regx}"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
+24
-20
@@ -23,7 +23,7 @@ CHECK_REMEDIATION_extra7102='Check Identified IPs; consider changing them to pri
|
||||
CHECK_DOC_extra7102='https://www.shodan.io/'
|
||||
CHECK_CAF_EPIC_extra7102='Infrastructure Security'
|
||||
|
||||
# Watch out, always use Shodan API key, if you use `curl https://www.shodan.io/host/{ip}` massively
|
||||
# Watch out, always use Shodan API key, if you use `curl https://www.shodan.io/host/{ip}` massively
|
||||
# your IP will be banned by Shodan
|
||||
|
||||
# This is the right way to do so
|
||||
@@ -32,27 +32,31 @@ CHECK_CAF_EPIC_extra7102='Infrastructure Security'
|
||||
# Each finding will be saved in prowler/output folder for further review.
|
||||
|
||||
extra7102(){
|
||||
if [[ ! $SHODAN_API_KEY ]]; then
|
||||
textInfo "[extra7102] Requires a Shodan API key to work. Use -N <shodan_api_key>"
|
||||
else
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_EIP=$($AWSCLI $PROFILE_OPT --region $regx ec2 describe-network-interfaces --query 'NetworkInterfaces[*].Association.PublicIp' --output text)
|
||||
if [[ $LIST_OF_EIP ]]; then
|
||||
for ip in $LIST_OF_EIP;do
|
||||
SHODAN_QUERY=$(curl -ks https://api.shodan.io/shodan/host/$ip?key=$SHODAN_API_KEY)
|
||||
# Shodan has a request rate limit of 1 request/second.
|
||||
sleep 1
|
||||
if [[ $SHODAN_QUERY == *"No information available for that IP"* ]]; then
|
||||
textPass "$regx: IP $ip is not listed in Shodan" "$regx"
|
||||
else
|
||||
echo $SHODAN_QUERY > $OUTPUT_DIR/shodan-output-$ip.json
|
||||
IP_SHODAN_INFO=$(cat $OUTPUT_DIR/shodan-output-$ip.json | jq -r '. | { ports: .ports, org: .org, country: .country_name }| @text' | tr -d \"\{\}\}\]\[ | tr , '\ ' )
|
||||
textFail "$regx: IP $ip is listed in Shodan with data $IP_SHODAN_INFO. More info https://www.shodan.io/host/$ip and $OUTPUT_DIR/shodan-output-$ip.json" "$regx" "$ip"
|
||||
fi
|
||||
done
|
||||
if [[ ! $SHODAN_API_KEY ]]; then
|
||||
textInfo "$regx: Requires a Shodan API key to work. Use -N <shodan_api_key>" "$regx"
|
||||
else
|
||||
textInfo "$regx: No Public or Elastic IPs found" "$regx"
|
||||
LIST_OF_EIP=$($AWSCLI $PROFILE_OPT --region $regx ec2 describe-network-interfaces --query 'NetworkInterfaces[*].Association.PublicIp' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_EIP" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe network interfaces" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_EIP ]]; then
|
||||
for ip in $LIST_OF_EIP;do
|
||||
SHODAN_QUERY=$(curl -ks https://api.shodan.io/shodan/host/$ip?key=$SHODAN_API_KEY)
|
||||
# Shodan has a request rate limit of 1 request/second.
|
||||
sleep 1
|
||||
if [[ $SHODAN_QUERY == *"No information available for that IP"* ]]; then
|
||||
textPass "$regx: IP $ip is not listed in Shodan" "$regx"
|
||||
else
|
||||
echo $SHODAN_QUERY > $OUTPUT_DIR/shodan-output-$ip.json
|
||||
IP_SHODAN_INFO=$(cat $OUTPUT_DIR/shodan-output-$ip.json | jq -r '. | { ports: .ports, org: .org, country: .country_name }| @text' | tr -d \"\{\}\}\]\[ | tr , '\ ' )
|
||||
textFail "$regx: IP $ip is listed in Shodan with data $IP_SHODAN_INFO. More info https://www.shodan.io/host/$ip and $OUTPUT_DIR/shodan-output-$ip.json" "$regx" "$ip"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: No Public or Elastic IPs found" "$regx"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
fi
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7103='IAM'
|
||||
|
||||
extra7103(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text)
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list notebook instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_INSTANCES ]];then
|
||||
for nb_instance in $LIST_SM_NB_INSTANCES; do
|
||||
SM_NB_ROOTACCESS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-notebook-instance --notebook-instance-name $nb_instance --query 'RootAccess' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7104='Infrastructure Security'
|
||||
|
||||
extra7104(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text)
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list notebook instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_INSTANCES ]];then
|
||||
for nb_instance in $LIST_SM_NB_INSTANCES; do
|
||||
SM_NB_SUBNETID=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-notebook-instance --notebook-instance-name $nb_instance --query 'SubnetId' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7105='Infrastructure Security'
|
||||
|
||||
extra7105(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_MODELS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-models --query 'Models[*].ModelName' --output text)
|
||||
LIST_SM_NB_MODELS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-models --query 'Models[*].ModelName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_MODELS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list models" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_MODELS ]];then
|
||||
for nb_model_name in $LIST_SM_NB_MODELS; do
|
||||
SM_NB_NETWORKISOLATION=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-model --model-name $nb_model_name --query 'EnableNetworkIsolation' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7106='Infrastructure Security'
|
||||
|
||||
extra7106(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_MODELS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-models --query 'Models[*].ModelName' --output text)
|
||||
LIST_SM_NB_MODELS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-models --query 'Models[*].ModelName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_MODELS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list models" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_MODELS ]];then
|
||||
for nb_model_name in $LIST_SM_NB_MODELS; do
|
||||
SM_NB_VPCCONFIG=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-model --model-name $nb_model_name --query 'VpcConfig.Subnets' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7107='Data Protection'
|
||||
|
||||
extra7107(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text)
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_JOBS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list training jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_JOBS ]];then
|
||||
for nb_job_name in $LIST_SM_NB_JOBS; do
|
||||
SM_NB_INTERCONTAINERENCRYPTION=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-training-job --training-job-name $nb_job_name --query 'EnableInterContainerTrafficEncryption' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7108='Data Protection'
|
||||
|
||||
extra7108(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text)
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_JOBS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list training jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_JOBS ]];then
|
||||
for nb_job_name in $LIST_SM_NB_JOBS; do
|
||||
SM_JOB_KMSENCRYPTION=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-training-job --training-job-name $nb_job_name --query 'ResourceConfig.VolumeKmsKeyId' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7109='Infrastructure Security'
|
||||
|
||||
extra7109(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text)
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_JOBS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list training jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_JOBS ]];then
|
||||
for nb_job_name in $LIST_SM_NB_JOBS; do
|
||||
SM_NB_NETWORKISOLATION=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-training-job --training-job-name $nb_job_name --query 'EnableNetworkIsolation' --output text)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra711='Data Protection'
|
||||
extra711(){
|
||||
# "Check for Publicly Accessible Redshift Clusters "
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_PUBLIC_REDSHIFT_CLUSTERS=$($AWSCLI redshift describe-clusters $PROFILE_OPT --region $regx --query 'Clusters[?PubliclyAccessible == `true`].[ClusterIdentifier,Endpoint.Address]' --output text)
|
||||
LIST_OF_PUBLIC_REDSHIFT_CLUSTERS=$($AWSCLI redshift describe-clusters $PROFILE_OPT --region $regx --query 'Clusters[?PubliclyAccessible == `true`].[ClusterIdentifier,Endpoint.Address]' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_PUBLIC_REDSHIFT_CLUSTERS" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe clusters" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_PUBLIC_REDSHIFT_CLUSTERS ]];then
|
||||
while read -r cluster;do
|
||||
CLUSTER_ID=$(echo $cluster | awk '{ print $1; }')
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7110='Infrastructure Security'
|
||||
|
||||
extra7110(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text)
|
||||
LIST_SM_NB_JOBS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-training-jobs --query 'TrainingJobSummaries[*].TrainingJobName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_JOBS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list training jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_JOBS ]];then
|
||||
for nb_job_name in $LIST_SM_NB_JOBS; do
|
||||
SM_NB_SUBNETS=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-training-job --training-job-name $nb_job_name --query 'VpcConfig.Subnets' --output text)
|
||||
|
||||
+16
-8
@@ -1,5 +1,5 @@
|
||||
#!/usr/bin/env bash
|
||||
|
||||
|
||||
# Prowler - the handy cloud security tool (copyright 2020) by Toni de la Fuente
|
||||
#
|
||||
# Licensed under the Apache License, Version 2.0 (the "License"); you may not
|
||||
@@ -26,18 +26,26 @@ CHECK_CAF_EPIC_extra7111='Infrastructure Security'
|
||||
|
||||
extra7111(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text)
|
||||
if [[ $LIST_SM_NB_INSTANCES ]];then
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list notebook instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_INSTANCES ]];then
|
||||
for nb_instance in $LIST_SM_NB_INSTANCES; do
|
||||
SM_NB_DIRECTINET=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-notebook-instance --notebook-instance-name $nb_instance --query 'DirectInternetAccess' --output text)
|
||||
SM_NB_DIRECTINET=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-notebook-instance --notebook-instance-name $nb_instance --query 'DirectInternetAccess' --output text 2>&1)
|
||||
if [[ $(echo "$SM_NB_DIRECTINET" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe notebook instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ "${SM_NB_DIRECTINET}" == "Enabled" ]]; then
|
||||
textFail "${regx}: Sagemaker Notebook instance $nb_instance has direct internet access enabled" "${regx}" "$nb_instance"
|
||||
else
|
||||
textPass "${regx}: Sagemaker Notebook instance $nb_instance has direct internet access disabled" "${regx}" "$nb_instance"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
else
|
||||
else
|
||||
textInfo "${regx}: No Sagemaker Notebook instances found" "${regx}"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7112='Data Protection'
|
||||
|
||||
extra7112(){
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text)
|
||||
LIST_SM_NB_INSTANCES=$($AWSCLI $PROFILE_OPT --region $regx sagemaker list-notebook-instances --query 'NotebookInstances[*].NotebookInstanceName' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SM_NB_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list notebook instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SM_NB_INSTANCES ]];then
|
||||
for nb_instance in $LIST_SM_NB_INSTANCES; do
|
||||
SM_NB_KMSKEY=$($AWSCLI $PROFILE_OPT --region $regx sagemaker describe-notebook-instance --notebook-instance-name $nb_instance --query 'KmsKeyId' --output text)
|
||||
|
||||
@@ -37,7 +37,11 @@ CHECK_CAF_EPIC_extra7113='Data Protection'
|
||||
|
||||
extra7113(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text)
|
||||
LIST_OF_RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_RDS_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe DB instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_RDS_INSTANCES ]];then
|
||||
for rdsinstance in $LIST_OF_RDS_INSTANCES; do
|
||||
IS_DELETIONPROTECTION=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --db-instance-identifier $rdsinstance --query 'DBInstances[*].DeletionProtection' --output text)
|
||||
@@ -48,7 +52,7 @@ extra7113(){
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: No RDS instances found" "$regx" "$rdsinstance"
|
||||
textInfo "$regx: No RDS instances found" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7114='Data Protection'
|
||||
|
||||
extra7114(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json)
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json 2>&1)
|
||||
if [[ $(echo "$LIST_EP_SC" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get dev endpoints" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_EP_SC != '[]' ]]; then
|
||||
for ep in $(echo "${LIST_EP_SC}"| jq -r '.[] | @base64');do
|
||||
ENDPOINT_NAME=$(echo $ep | base64 --decode | jq -r '.Name')
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7115='Data Protection'
|
||||
|
||||
extra7115(){
|
||||
for regx in $REGIONS; do
|
||||
CONNECTION_LIST=$($AWSCLI glue get-connections $PROFILE_OPT --region $regx --output json --query 'ConnectionList[*].{Name:Name,SSL:ConnectionProperties.JDBC_ENFORCE_SSL}')
|
||||
CONNECTION_LIST=$($AWSCLI glue get-connections $PROFILE_OPT --region $regx --output json --query 'ConnectionList[*].{Name:Name,SSL:ConnectionProperties.JDBC_ENFORCE_SSL}' 2>&1)
|
||||
if [[ $(echo "$CONNECTION_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get connections" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $CONNECTION_LIST != '[]' ]]; then
|
||||
for connection in $(echo "${CONNECTION_LIST}" | jq -r '.[] | @base64'); do
|
||||
CONNECTION_NAME=$(echo $connection | base64 --decode | jq -r '.Name' )
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7116='Data Protection'
|
||||
|
||||
extra7116(){
|
||||
for regx in $REGIONS; do
|
||||
TABLE_LIST=$($AWSCLI glue search-tables --max-results 1 $PROFILE_OPT --region $regx --output text --query 'TableList[*]' )
|
||||
TABLE_LIST=$($AWSCLI glue search-tables --max-results 1 $PROFILE_OPT --region $regx --output text --query 'TableList[*]' 2>&1)
|
||||
if [[ $(echo "$TABLE_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to search tables" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ ! -z $TABLE_LIST ]]; then
|
||||
METADATA_ENCRYPTED=$($AWSCLI glue get-data-catalog-encryption-settings $PROFILE_OPT --region $regx --output text --query "DataCatalogEncryptionSettings.EncryptionAtRest.CatalogEncryptionMode")
|
||||
if [[ "$METADATA_ENCRYPTED" == "DISABLED" ]]; then
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7117='Data Protection'
|
||||
|
||||
extra7117(){
|
||||
for regx in $REGIONS; do
|
||||
CONNECTION_LIST=$($AWSCLI glue get-connections $PROFILE_OPT --region $regx --output text --query 'ConnectionList[*]')
|
||||
CONNECTION_LIST=$($AWSCLI glue get-connections $PROFILE_OPT --region $regx --output text --query 'ConnectionList[*]' 2>&1)
|
||||
if [[ $(echo "$CONNECTION_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get connections" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ ! -z $CONNECTION_LIST ]]; then
|
||||
METADATA_ENCRYPTED=$($AWSCLI glue get-data-catalog-encryption-settings $PROFILE_OPT --region $regx --output text --query "DataCatalogEncryptionSettings.ConnectionPasswordEncryption.ReturnConnectionPasswordEncrypted")
|
||||
if [[ "$METADATA_ENCRYPTED" == "False" ]]; then
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7118='Data Protection'
|
||||
|
||||
extra7118(){
|
||||
for regx in $REGIONS; do
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration,JobEncryption:DefaultArguments."--encryption-type"}')
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration,JobEncryption:DefaultArguments."--encryption-type"}' 2>&1)
|
||||
if [[ $(echo "$JOB_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $JOB_LIST != '[]' ]]; then
|
||||
for job in $(echo "${JOB_LIST}" | jq -r '.[] | @base64'); do
|
||||
JOB_NAME=$(echo $job | base64 --decode | jq -r '.Name')
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7119='Logging and Monitoring'
|
||||
|
||||
extra7119(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json)
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json 2>&1)
|
||||
if [[ $(echo "$LIST_EP_SC" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get dev endpoints" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_EP_SC != '[]' ]]; then
|
||||
for ep in $(echo "${LIST_EP_SC}"| jq -r '.[] | @base64');do
|
||||
ENDPOINT_NAME=$(echo $ep | base64 --decode | jq -r '.Name')
|
||||
|
||||
+19
-10
@@ -23,13 +23,22 @@ CHECK_REMEDIATION_extra712='Enable Amazon Macie and create appropriate jobs to d
|
||||
CHECK_DOC_extra712='https://docs.aws.amazon.com/macie/latest/user/getting-started.html'
|
||||
CHECK_CAF_EPIC_extra712='Data Protection'
|
||||
|
||||
extra712(){
|
||||
# "No API commands available to check if Macie is enabled,"
|
||||
# "just looking if IAM Macie related permissions exist. "
|
||||
MACIE_IAM_ROLES_CREATED=$($AWSCLI iam list-roles $PROFILE_OPT --query 'Roles[*].Arn'|grep AWSMacieServiceCustomer|wc -l)
|
||||
if [[ $MACIE_IAM_ROLES_CREATED -eq 2 ]];then
|
||||
textPass "$REGION: Macie related IAM roles exist so it might be enabled. Check it out manually" "$REGION"
|
||||
else
|
||||
textFail "$REGION: No Macie related IAM roles found. It is most likely not to be enabled" "$REGION"
|
||||
fi
|
||||
}
|
||||
extra712(){
|
||||
# Macie supports get-macie-session which tells the current status, if not Disabled.
|
||||
# Capturing the STDOUT can help determine when Disabled.
|
||||
for region in $REGIONS; do
|
||||
MACIE_STATUS=$($AWSCLI macie2 get-macie-session ${PROFILE_OPT} --region "$region" --query status --output text 2>&1)
|
||||
if [[ "$MACIE_STATUS" == "ENABLED" ]]; then
|
||||
textPass "$region: Macie is enabled." "$region"
|
||||
|
||||
elif [[ "$MACIE_STATUS" == "PAUSED" ]]; then
|
||||
textFail "$region: Macie is currently in a SUSPENDED state." "$region"
|
||||
|
||||
elif grep -q -E 'Macie is not enabled' <<< "${MACIE_STATUS}"; then
|
||||
textFail "$region: Macie is not enabled." "$region"
|
||||
|
||||
elif grep -q -E 'AccessDenied|UnauthorizedOperation|AuthorizationError' <<< "${MACIE_STATUS}"; then
|
||||
textInfo "$region: Access Denied trying to get AWS Macie information." "$region"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7120='Logging and Monitoring'
|
||||
|
||||
extra7120(){
|
||||
for regx in $REGIONS; do
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration}')
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration}' 2>&1)
|
||||
if [[ $(echo "$JOB_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $JOB_LIST != '[]' ]]; then
|
||||
for job in $(echo "${JOB_LIST}" | jq -r '.[] | @base64'); do
|
||||
JOB_NAME=$(echo $job | base64 --decode | jq -r '.Name')
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7121='Data Protection'
|
||||
|
||||
extra7121(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json)
|
||||
LIST_EP_SC=$($AWSCLI glue get-dev-endpoints $PROFILE_OPT --region $regx --query 'DevEndpoints[*].{Name:EndpointName,Security:SecurityConfiguration}' --output json 2>&1)
|
||||
if [[ $(echo "$LIST_EP_SC" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get dev endpoints" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_EP_SC != '[]' ]]; then
|
||||
for ep in $(echo "${LIST_EP_SC}"| jq -r '.[] | @base64');do
|
||||
ENDPOINT_NAME=$(echo $ep | base64 --decode | jq -r '.Name')
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7122='Data Protection'
|
||||
|
||||
extra7122(){
|
||||
for regx in $REGIONS; do
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration}')
|
||||
JOB_LIST=$($AWSCLI glue get-jobs $PROFILE_OPT --region $regx --output json --query 'Jobs[*].{Name:Name,SecurityConfiguration:SecurityConfiguration}' 2>&1)
|
||||
if [[ $(echo "$JOB_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to get jobs" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $JOB_LIST != '[]' ]]; then
|
||||
for job in $(echo "${JOB_LIST}" | jq -r '.[] | @base64'); do
|
||||
JOB_NAME=$(echo $job | base64 --decode | jq -r '.Name')
|
||||
|
||||
@@ -33,6 +33,6 @@ extra7123(){
|
||||
textFail "User $user has 2 active access keys" "$REGION" "$user"
|
||||
done
|
||||
else
|
||||
textPass "No users with 2 active access keys"
|
||||
textPass "No users with 2 active access keys" "$REGION"
|
||||
fi
|
||||
}
|
||||
}
|
||||
|
||||
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_extra7124='Infrastructure Security'
|
||||
extra7124(){
|
||||
for regx in $REGIONS; do
|
||||
# Filters running instances only
|
||||
LIST_EC2_INSTANCES=$($AWSCLI ec2 describe-instances $PROFILE_OPT --query 'Reservations[*].Instances[*].[InstanceId]' --filters Name=instance-state-name,Values=running --region $regx --output text)
|
||||
LIST_EC2_INSTANCES=$($AWSCLI ec2 describe-instances $PROFILE_OPT --query 'Reservations[*].Instances[*].[InstanceId]' --filters Name=instance-state-name,Values=running --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$LIST_EC2_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_EC2_INSTANCES ]]; then
|
||||
LIST_SSM_MANAGED_INSTANCES=$($AWSCLI ssm describe-instance-information $PROFILE_OPT --query "InstanceInformationList[].InstanceId" --region $regx | jq -r '.[]')
|
||||
LIST_EC2_UNMANAGED=$(echo ${LIST_SSM_MANAGED_INSTANCES[@]} ${LIST_EC2_INSTANCES[@]} | tr ' ' '\n' | sort | uniq -u)
|
||||
|
||||
@@ -31,15 +31,15 @@ extra7125(){
|
||||
for user in $LIST_USERS; do
|
||||
# Would be virtual if sms-mfa or mfa, hardware is u2f or different.
|
||||
MFA_TYPE=$($AWSCLI iam list-mfa-devices --user-name $user $PROFILE_OPT --region $REGION --query MFADevices[].SerialNumber --output text | awk -F':' '{ print $6 }'| awk -F'/' '{ print $1 }')
|
||||
if [[ $MFA_TYPE == "mfa" || $MFA_TYPE == "sms-mfa" ]]; then
|
||||
textInfo "User $user has virtual MFA enabled"
|
||||
elif [[ $MFA_TYPE == "" ]]; then
|
||||
if [[ $MFA_TYPE == "mfa" || $MFA_TYPE == "sms-mfa" ]]; then
|
||||
textInfo "User $user has virtual MFA enabled" "$REGION" "$user"
|
||||
elif [[ $MFA_TYPE == "" ]]; then
|
||||
textFail "User $user has not hardware MFA enabled" "$REGION" "$user"
|
||||
else
|
||||
else
|
||||
textPass "User $user has hardware MFA enabled" "$REGION" "$user"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textPass "No users found"
|
||||
textPass "No users found" "$REGION"
|
||||
fi
|
||||
}
|
||||
}
|
||||
|
||||
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_extra7127='Infrastructure Security'
|
||||
|
||||
extra7127(){
|
||||
for regx in $REGIONS; do
|
||||
NON_COMPLIANT_SSM_MANAGED_INSTANCES=$($AWSCLI ssm list-resource-compliance-summaries $PROFILE_OPT --region $regx --filters Key=Status,Values=NON_COMPLIANT --query ResourceComplianceSummaryItems[].ResourceId --output text)
|
||||
NON_COMPLIANT_SSM_MANAGED_INSTANCES=$($AWSCLI ssm list-resource-compliance-summaries $PROFILE_OPT --region $regx --filters Key=Status,Values=NON_COMPLIANT --query ResourceComplianceSummaryItems[].ResourceId --output text 2>&1)
|
||||
if [[ $(echo "$NON_COMPLIANT_SSM_MANAGED_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list resource compliance summaries" "$regx"
|
||||
continue
|
||||
fi
|
||||
COMPLIANT_SSM_MANAGED_INSTANCES=$($AWSCLI ssm list-resource-compliance-summaries $PROFILE_OPT --region $regx --filters Key=Status,Values=COMPLIANT --query ResourceComplianceSummaryItems[].ResourceId --output text)
|
||||
if [[ $NON_COMPLIANT_SSM_MANAGED_INSTANCES || $COMPLIANT_SSM_MANAGED_INSTANCES ]]; then
|
||||
if [[ $NON_COMPLIANT_SSM_MANAGED_INSTANCES ]]; then
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7128='Data Protection'
|
||||
|
||||
extra7128(){
|
||||
for regx in $REGIONS; do
|
||||
DDB_TABLES_LIST=$($AWSCLI dynamodb list-tables $PROFILE_OPT --region $regx --output text --query TableNames)
|
||||
DDB_TABLES_LIST=$($AWSCLI dynamodb list-tables $PROFILE_OPT --region $regx --output text --query TableNames 2>&1)
|
||||
if [[ $(echo "$DDB_TABLES_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list tables" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $DDB_TABLES_LIST ]]; then
|
||||
for table in $DDB_TABLES_LIST; do
|
||||
DDB_TABLE_WITH_KMS=$($AWSCLI dynamodb describe-table --table-name $table $PROFILE_OPT --region $regx --query Table.SSEDescription.SSEType --output text)
|
||||
|
||||
@@ -29,7 +29,11 @@ PARALLEL_REGIONS="50"
|
||||
extra7129(){
|
||||
for regx in $REGIONS; do
|
||||
# (
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[?Scheme == `internet-facing` && Type == `application`].[LoadBalancerName]' --output text)
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[?Scheme == `internet-facing` && Type == `application`].[LoadBalancerName]' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_ELBSV2" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe load balancers" "$regx"
|
||||
continue
|
||||
fi
|
||||
LIST_OF_WAFV2_WEBACL_ARN=$($AWSCLI wafv2 list-web-acls $PROFILE_OPT --region=$regx --scope=REGIONAL --query WebACLs[*].ARN --output text)
|
||||
LIST_OF_WAFV1_WEBACL_WEBACLID=$($AWSCLI waf-regional list-web-acls $PROFILE_OPT --region $regx --query WebACLs[*].[WebACLId] --output text)
|
||||
|
||||
|
||||
@@ -44,7 +44,7 @@ extra713(){
|
||||
fi
|
||||
else
|
||||
# if list-detectors return any error
|
||||
textInfo "$regx: GuardDuty not checked" "$regx"
|
||||
textInfo "$regx: GuardDuty not checked or Access Denied trying to get detector" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7130='Data Protection'
|
||||
|
||||
extra7130(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_SNS=$($AWSCLI sns list-topics $PROFILE_OPT --region $regx --query 'Topics[*].TopicArn' --output text)
|
||||
LIST_SNS=$($AWSCLI sns list-topics $PROFILE_OPT --region $regx --query 'Topics[*].TopicArn' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_SNS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list topics" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_SNS ]];then
|
||||
for topic in $LIST_SNS; do
|
||||
SHORT_TOPIC=$(echo $topic | awk -F ":" '{print $NF}')
|
||||
|
||||
@@ -18,15 +18,19 @@ CHECK_SEVERITY_extra7131="Low"
|
||||
CHECK_ASFF_RESOURCE_TYPE_extra7131="AwsRdsDbInstance"
|
||||
CHECK_ALTERNATE_check7131="extra7131"
|
||||
CHECK_SERVICENAME_extra7131="rds"
|
||||
CHECK_RISK_extra7131='Auto Minor Version Upgrade is a feature that you can enable to have your database automatically upgraded when a new minor database engine version is available. Minor version upgrades often patch security vulnerabilities and fix bugs; and therefor should be applied.'
|
||||
CHECK_REMEDIATION_extra7131='Enable auto minor version upgrade for all databases and environments.'
|
||||
CHECK_RISK_extra7131='Auto Minor Version Upgrade is a feature that you can enable to have your relational database automatically upgraded when a new minor database engine version is available. Minor version upgrades often patch security vulnerabilities and fix bugs; and therefor should be applied.'
|
||||
CHECK_REMEDIATION_extra7131='Enable auto minor version upgrade for all relational databases and environments.'
|
||||
CHECK_DOC_extra7131='https://aws.amazon.com/blogs/database/best-practices-for-upgrading-amazon-rds-to-major-and-minor-versions-of-postgresql/'
|
||||
CHECK_CAF_EPIC_extra7131='Infrastructure Security'
|
||||
|
||||
extra7131(){
|
||||
for regx in $REGIONS; do
|
||||
# LIST_OF_RDS_PUBLIC_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query 'DBInstances[?PubliclyAccessible==`true` && DBInstanceStatus==`"available"`].[DBInstanceIdentifier,Endpoint.Address]' --output text)
|
||||
LIST_OF_RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query 'DBInstances[*].[DBInstanceIdentifier,AutoMinorVersionUpgrade]' --output text)
|
||||
LIST_OF_RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].[DBInstanceIdentifier,AutoMinorVersionUpgrade]" --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_RDS_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe DB instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_RDS_INSTANCES ]];then
|
||||
while read -r rds_instance;do
|
||||
RDS_NAME=$(echo $rds_instance | awk '{ print $1; }')
|
||||
|
||||
@@ -25,19 +25,23 @@ CHECK_CAF_EPIC_extra7132='Logging and Monitoring'
|
||||
|
||||
extra7132(){
|
||||
for regx in $REGIONS; do
|
||||
RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text)
|
||||
RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text 2>&1)
|
||||
if [[ $(echo "$RDS_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe DB instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $RDS_INSTANCES ]];then
|
||||
for rdsinstance in ${RDS_INSTANCES}; do
|
||||
RDS_NAME="$rdsinstance"
|
||||
MONITORING_FLAG=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --db-instance-identifier $rdsinstance --query 'DBInstances[*].[EnhancedMonitoringResourceArn]' --output text)
|
||||
if [[ $MONITORING_FLAG == "None" ]];then
|
||||
textFail "$regx: RDS instance: $RDS_NAME has enhanced monitoring disabled!" "$rex" "$RDS_NAME"
|
||||
if [[ $MONITORING_FLAG == "None" ]];then
|
||||
textFail "$regx: RDS instance: $RDS_NAME has enhanced monitoring disabled!" "$regx" "$RDS_NAME"
|
||||
else
|
||||
textPass "$regx: RDS instance: $RDS_NAME has enhanced monitoring enabled." "$regx" "$RDS_NAME"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: no RDS instances found" "$regx" "$RDS_NAME"
|
||||
textInfo "$regx: no RDS instances found" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7133='Data Protection'
|
||||
|
||||
extra7133(){
|
||||
for regx in $REGIONS; do
|
||||
RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text)
|
||||
RDS_INSTANCES=$($AWSCLI rds describe-db-instances $PROFILE_OPT --region $regx --query "DBInstances[?Engine != 'docdb'].DBInstanceIdentifier" --output text 2>&1)
|
||||
if [[ $(echo "$RDS_INSTANCES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe DB instances" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $RDS_INSTANCES ]];then
|
||||
for rdsinstance in ${RDS_INSTANCES}; do
|
||||
RDS_NAME="$rdsinstance"
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7134='Infrastructure Security'
|
||||
|
||||
extra7134(){
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`20` && ToPort==`21`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`20` && ToPort==`21`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`)) && (IpProtocol==`tcp`)]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0 for FTP ports" "$regx" "$SG"
|
||||
@@ -34,4 +38,4 @@ extra7134(){
|
||||
textPass "$regx: No Security Groups found with any port open to 0.0.0.0/0 for FTP ports" "$regx" "$SG"
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7135='Infrastructure Security'
|
||||
|
||||
extra7135(){
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`9092` && ToPort==`9092`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`9092` && ToPort==`9092`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`)) && (IpProtocol==`tcp`)]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0 for Kafka ports" "$regx" "$SG"
|
||||
@@ -34,4 +38,4 @@ extra7135(){
|
||||
textPass "$regx: No Security Groups found with any port open to 0.0.0.0/0 for Kafka ports" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
@@ -11,7 +11,7 @@
|
||||
# CONDITIONS OF ANY KIND, either express or implied. See the License for the
|
||||
# specific language governing permissions and limitations under the License.
|
||||
CHECK_ID_extra7136="7.136"
|
||||
CHECK_TITLE_extra7136="[extra7136] Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to Telnet port 23 "
|
||||
CHECK_TITLE_extra7136="[extra7136] Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to Telnet port 23"
|
||||
CHECK_SCORED_extra7136="NOT_SCORED"
|
||||
CHECK_CIS_LEVEL_extra7136="EXTRA"
|
||||
CHECK_SEVERITY_extra7136="High"
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7136='Infrastructure Security'
|
||||
|
||||
extra7136(){
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`23` && ToPort==`23`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`23` && ToPort==`23`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`)) && (IpProtocol==`tcp`)]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0 for Telnet ports" "$regx" "$SG"
|
||||
@@ -34,4 +38,4 @@ extra7136(){
|
||||
textPass "$regx: No Security Groups found with any port open to 0.0.0.0/0 for Telnet ports" "$regx" "$SG"
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
@@ -11,7 +11,7 @@
|
||||
# CONDITIONS OF ANY KIND, either express or implied. See the License for the
|
||||
# specific language governing permissions and limitations under the License.
|
||||
CHECK_ID_extra7137="7.137"
|
||||
CHECK_TITLE_extra7137="[extra7137] Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to Windows SQL Server ports 1433 or 1434 "
|
||||
CHECK_TITLE_extra7137="[extra7137] Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to Windows SQL Server ports 1433 or 1434"
|
||||
CHECK_SCORED_extra7137="NOT_SCORED"
|
||||
CHECK_CIS_LEVEL_extra7137="EXTRA"
|
||||
CHECK_SEVERITY_extra7137="High"
|
||||
@@ -25,7 +25,11 @@ CHECK_CAF_EPIC_extra7137='Infrastructure Security'
|
||||
|
||||
extra7137(){
|
||||
for regx in $REGIONS; do
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`1433` && ToPort==`1434`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text)
|
||||
SG_LIST=$($AWSCLI ec2 describe-security-groups --query 'SecurityGroups[?length(IpPermissions[?((FromPort==null && ToPort==null) || (FromPort==`1433` && ToPort==`1434`)) && (contains(IpRanges[].CidrIp, `0.0.0.0/0`) || contains(Ipv6Ranges[].CidrIpv6, `::/0`))]) > `0`].{GroupId:GroupId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$SG_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe security groups" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SG_LIST ]];then
|
||||
for SG in $SG_LIST;do
|
||||
textFail "$regx: Found Security Group: $SG open to 0.0.0.0/0 for Microsoft SQL Server ports" "$regx" "$SG"
|
||||
@@ -34,4 +38,4 @@ extra7137(){
|
||||
textPass "$regx: No Security Groups found with any port open to 0.0.0.0/0 for Microsoft SQL Server ports" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7138='Infrastructure Security'
|
||||
|
||||
extra7138(){
|
||||
for regx in $REGIONS; do
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?((!PortRange) && (CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text)
|
||||
NACL_LIST=$($AWSCLI ec2 describe-network-acls --query 'NetworkAcls[?Entries[?((!PortRange) && (CidrBlock == `0.0.0.0/0`) && (Egress == `false`) && (RuleAction == `allow`))]].{NetworkAclId:NetworkAclId}' $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$NACL_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe network acls" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $NACL_LIST ]];then
|
||||
for NACL in $NACL_LIST;do
|
||||
textInfo "$regx: Found Network ACL: $NACL open to 0.0.0.0/0 for any port" "$regx" "$NACL"
|
||||
|
||||
@@ -25,7 +25,11 @@ extra7139(){
|
||||
|
||||
for regx in $REGIONS; do
|
||||
DETECTORS_LIST=""
|
||||
DETECTORS_LIST=$($AWSCLI guardduty list-detectors --query DetectorIds $PROFILE_OPT --region $regx --output text)
|
||||
DETECTORS_LIST=$($AWSCLI guardduty list-detectors --query DetectorIds $PROFILE_OPT --region $regx --output text 2>&1)
|
||||
if [[ $(echo "$DETECTORS_LIST" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list detectors" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $DETECTORS_LIST ]];then
|
||||
for DETECTOR in $DETECTORS_LIST;do
|
||||
FINDINGS_COUNT=""
|
||||
|
||||
@@ -28,8 +28,9 @@ extra714(){
|
||||
LIST_OF_DISTRIBUTIONS=$($AWSCLI cloudfront list-distributions $PROFILE_OPT --query 'DistributionList.Items[].Id' --output text | grep -v "^None")
|
||||
if [[ $LIST_OF_DISTRIBUTIONS ]]; then
|
||||
for dist in $LIST_OF_DISTRIBUTIONS; do
|
||||
LOG_ENABLED=$($AWSCLI cloudfront get-distribution $PROFILE_OPT --id "$dist" --query 'Distribution.DistributionConfig.Logging.Enabled' | grep true)
|
||||
if [[ $LOG_ENABLED ]]; then
|
||||
LOG_ENABLED=$($AWSCLI cloudfront get-distribution $PROFILE_OPT --id "$dist" --query 'Distribution.DistributionConfig.Logging.Enabled' --output text | grep True)
|
||||
LOG_ENABLED_REALTIME=$($AWSCLI cloudfront get-distribution $PROFILE_OPT --id "$dist" --query 'Distribution.DistributionConfig.DefaultCacheBehavior.RealtimeLogConfigArn' --output text | grep -i arn)
|
||||
if [[ $LOG_ENABLED || $LOG_ENABLED_REALTIME ]]; then
|
||||
textPass "$REGION: CloudFront distribution $dist has logging enabled" "$REGION" "$dist"
|
||||
else
|
||||
textFail "$REGION: CloudFront distribution $dist has logging disabled" "$REGION" "$dist"
|
||||
|
||||
@@ -24,7 +24,11 @@ CHECK_CAF_EPIC_extra7140='Data Protection'
|
||||
extra7140(){
|
||||
|
||||
for regx in $REGIONS; do
|
||||
SSM_DOCS=$($AWSCLI $PROFILE_OPT --region $regx ssm list-documents --filters Key=Owner,Values=Self --query DocumentIdentifiers[].Name --output text)
|
||||
SSM_DOCS=$($AWSCLI $PROFILE_OPT --region $regx ssm list-documents --filters Key=Owner,Values=Self --query DocumentIdentifiers[].Name --output text 2>&1)
|
||||
if [[ $(echo "$SSM_DOCS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list documents" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $SSM_DOCS ]];then
|
||||
for ssmdoc in $SSM_DOCS; do
|
||||
SSM_DOC_SHARED_ALL=$($AWSCLI $PROFILE_OPT --region $regx ssm describe-document-permission --name "$ssmdoc" --permission-type "Share" --query AccountIds[] --output text | grep all)
|
||||
|
||||
+35
-22
@@ -24,32 +24,45 @@ CHECK_DOC_extra7141='https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGu
|
||||
CHECK_CAF_EPIC_extra7141='IAM'
|
||||
|
||||
extra7141(){
|
||||
SECRETS_TEMP_FOLDER="$PROWLER_DIR/secrets-$ACCOUNT_NUM"
|
||||
if [[ ! -d $SECRETS_TEMP_FOLDER ]]; then
|
||||
SECRETS_TEMP_FOLDER="$PROWLER_DIR/secrets-$ACCOUNT_NUM-$PROWLER_START_TIME"
|
||||
if [[ ! -d "${SECRETS_TEMP_FOLDER}" ]]; then
|
||||
# this folder is deleted once this check is finished
|
||||
mkdir $SECRETS_TEMP_FOLDER
|
||||
mkdir "${SECRETS_TEMP_FOLDER}"
|
||||
fi
|
||||
|
||||
for regx in $REGIONS; do
|
||||
SSM_DOCS=$($AWSCLI $PROFILE_OPT --region $regx ssm list-documents --filters Key=Owner,Values=Self --query DocumentIdentifiers[].Name --output text)
|
||||
if [[ $SSM_DOCS ]];then
|
||||
for ssmdoc in $SSM_DOCS; do
|
||||
SSM_DOC_FILE="$SECRETS_TEMP_FOLDER/extra7141-$ssmdoc-$regx-content.txt"
|
||||
$AWSCLI $PROFILE_OPT --region $regx ssm get-document --name $ssmdoc --output text --document-format JSON > $SSM_DOC_FILE
|
||||
FINDINGS=$(secretsDetector file $SSM_DOC_FILE)
|
||||
if [[ $FINDINGS -eq 0 ]]; then
|
||||
textPass "$regx: No secrets found in SSM Document $ssmdoc" "$regx" "$ssmdoc"
|
||||
# delete file if nothing interesting is there
|
||||
rm -f $SSM_DOC_FILE
|
||||
else
|
||||
textFail "$regx: Potential secret found SSM Document $ssmdoc" "$regx" "$ssmdoc"
|
||||
# delete file to not leave trace, user must look at the CFN Stack
|
||||
rm -f $SSM_DOC_FILE
|
||||
fi
|
||||
done
|
||||
for regx in ${REGIONS}; do
|
||||
CHECK_DETECT_SECRETS_INSTALLATION=$(secretsDetector)
|
||||
if [[ $? -eq 241 ]]; then
|
||||
textInfo "$regx: python library detect-secrets not found. Make sure it is installed correctly." "$regx"
|
||||
else
|
||||
textInfo "$regx: No SSM Document found." "$regx"
|
||||
SSM_DOCS=$("${AWSCLI}" ${PROFILE_OPT} --region "${regx}" ssm list-documents --filters 'Key=Owner,Values=Self' --query 'DocumentIdentifiers[].Name' --output text 2>&1)
|
||||
if [[ $(echo "${SSM_DOCS}" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "${regx}: Access Denied trying to list documents" "${regx}"
|
||||
continue
|
||||
fi
|
||||
if [[ ${SSM_DOCS} ]];then
|
||||
for ssmdoc in ${SSM_DOCS}; do
|
||||
SSM_DOC_FILE="${SECRETS_TEMP_FOLDER}/extra7141-${ssmdoc}-${regx}-content.txt"
|
||||
"${AWSCLI}" ${PROFILE_OPT} --region "${regx}" ssm get-document --name "${ssmdoc}" --output text --document-format JSON > "${SSM_DOC_FILE}" 2>&1
|
||||
if [[ $(grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError' "${SSM_DOC_FILE}") ]]; then
|
||||
textInfo "${regx}: Access Denied trying to get document" "${regx}"
|
||||
continue
|
||||
fi
|
||||
FINDINGS=$(secretsDetector file "${SSM_DOC_FILE}")
|
||||
if [[ "${FINDINGS}" -eq 0 ]]; then
|
||||
textPass "${regx}: No secrets found in SSM Document ${ssmdoc}" "${regx}" "${ssmdoc}"
|
||||
# delete file if nothing interesting is there
|
||||
rm -f "${SSM_DOC_FILE}"
|
||||
else
|
||||
textFail "${regx}: Potential secret found SSM Document ${ssmdoc}" "${regx}" "${ssmdoc}"
|
||||
# delete file to not leave trace, user must look at the CFN Stack
|
||||
rm -f "${SSM_DOC_FILE}"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "${regx}: No SSM Document found." "${regx}"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
rm -rf $SECRETS_TEMP_FOLDER
|
||||
rm -rf "${SECRETS_TEMP_FOLDER}"
|
||||
}
|
||||
|
||||
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_extra7142='Data Protection'
|
||||
|
||||
extra7142(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[?Type == `application`].[LoadBalancerArn]' --output text)
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[?Type == `application`].[LoadBalancerArn]' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_ELBSV2" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe load balancers" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_ELBSV2 ]];then
|
||||
for alb in $LIST_OF_ELBSV2;do
|
||||
CHECK_IF_DROP_INVALID_HEADER_FIELDS=$($AWSCLI elbv2 describe-load-balancer-attributes $PROFILE_OPT --region $regx --load-balancer-arn $alb --query 'Attributes[6]' --output text|grep -i true)
|
||||
@@ -37,8 +41,8 @@ extra7142(){
|
||||
textFail "$regx: Application Load Balancer $alb is not dropping invalid header fields" "$regx" "$alb"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: no ALBs found"
|
||||
else
|
||||
textInfo "$regx: no ALBs found" "$regx"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7143='Data Protection'
|
||||
extra7143(){
|
||||
# "Check if EFS have policies which allow access to everyone (Not Scored) (Not part of CIS benchmark)"
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_EFS_IDS=$($AWSCLI efs describe-file-systems $PROFILE_OPT --region $regx --query FileSystems[*].FileSystemId --output text|xargs -n1)
|
||||
LIST_OF_EFS_IDS=$($AWSCLI efs describe-file-systems $PROFILE_OPT --region $regx --query FileSystems[*].FileSystemId --output text 2>&1|xargs -n1 )
|
||||
if [[ $(echo "$LIST_OF_EFS_IDS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe file systems" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_EFS_IDS ]]; then
|
||||
for efsId in $LIST_OF_EFS_IDS;do
|
||||
EFS_POLICY_STATEMENTS=$($AWSCLI efs $PROFILE_OPT describe-file-system-policy --region $regx --file-system-id $efsId --output json --query Policy 2>&1)
|
||||
|
||||
@@ -18,8 +18,8 @@ CHECK_SEVERITY_extra7144="Medium"
|
||||
CHECK_ASFF_RESOURCE_TYPE_extra7144="AwsCloudWatch"
|
||||
CHECK_ALTERNATE_check7144="extra7144"
|
||||
CHECK_SERVICENAME_extra7144="cloudwatch"
|
||||
CHECK_RISK_extra7144=''
|
||||
CHECK_REMEDIATION_extra7144=''
|
||||
CHECK_RISK_extra7144='Cross-Account access to CloudWatch could increase the risk of compromising information between accounts'
|
||||
CHECK_REMEDIATION_extra7144='Grant usage permission on a per-resource basis to enforce least privilege and Zero Trust principles'
|
||||
CHECK_DOC_extra7144='https://docs.aws.amazon.com/AmazonCloudWatch/latest/monitoring/Cross-Account-Cross-Region.html'
|
||||
CHECK_CAF_EPIC_extra7144='Logging and Monitoring'
|
||||
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7145='IAM'
|
||||
extra7145(){
|
||||
# "Check if lambda functions have policies which allow access to every aws account (Not Scored) (Not part of CIS benchmark)"
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_LAMBDA_FUNCTIONS=$($AWSCLI lambda list-functions $PROFILE_OPT --region $regx --query Functions[*].FunctionName --output text)
|
||||
LIST_OF_LAMBDA_FUNCTIONS=$($AWSCLI lambda list-functions $PROFILE_OPT --region $regx --query Functions[*].FunctionName --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_LAMBDA_FUNCTIONS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list functions" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_LAMBDA_FUNCTIONS ]]; then
|
||||
for lambdaFunction in $LIST_OF_LAMBDA_FUNCTIONS;do
|
||||
FUNCTION_POLICY_STATEMENTS=$($AWSCLI lambda $PROFILE_OPT get-policy --region $regx --function-name $lambdaFunction --output json --query Policy 2>&1)
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7146='Infrastructure Security'
|
||||
extra7146(){
|
||||
# "Check if there is any unassigned elastic ip (Not Scored) (Not part of CIS benchmark)"
|
||||
for regx in $REGIONS; do
|
||||
ELASTIC_IP_ADDRESSES=$($AWSCLI ec2 describe-addresses $PROFILE_OPT --region $regx --query Addresses --output json)
|
||||
ELASTIC_IP_ADDRESSES=$($AWSCLI ec2 describe-addresses $PROFILE_OPT --region $regx --query Addresses --output json 2>&1)
|
||||
if [[ $(echo "$ELASTIC_IP_ADDRESSES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe addresses" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $ELASTIC_IP_ADDRESSES != [] ]]; then
|
||||
LIST_OF_ASSOCIATED_IPS=$(echo $ELASTIC_IP_ADDRESSES | jq -r '.[] | select(.AssociationId!=null) | .PublicIp')
|
||||
LIST_OF_UNASSOCIATED_IPS=$(echo $ELASTIC_IP_ADDRESSES | jq -r '.[] | select(.AssociationId==null) | .PublicIp')
|
||||
|
||||
+18
-9
@@ -16,7 +16,7 @@ CHECK_SCORED_extra7147="NOT_SCORED"
|
||||
CHECK_CIS_LEVEL_extra7147="EXTRA"
|
||||
CHECK_SEVERITY_extra7147="Critical"
|
||||
CHECK_ASFF_RESOURCE_TYPE_extra7147="AwsGlacierVault"
|
||||
CHECK_ALTERNATE_check7147="extra7142"
|
||||
CHECK_ALTERNATE_check7147="extra7147"
|
||||
CHECK_SERVICENAME_extra7147="glacier"
|
||||
CHECK_RISK_extra7147='Vaults accessible to everyone could expose sensitive data to bad actors'
|
||||
CHECK_REMEDIATION_extra7147='Ensure vault policy does not have principle as *'
|
||||
@@ -25,23 +25,32 @@ CHECK_CAF_EPIC_extra7147='Data Protection'
|
||||
|
||||
extra7147(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_VAULTS=$($AWSCLI glacier list-vaults $PROFILE_OPT --region $regx --account-id $ACCOUNT_NUM --query VaultList[*].VaultName --output text|xargs -n1)
|
||||
LIST_OF_VAULTS=$($AWSCLI glacier list-vaults ${PROFILE_OPT} --region "${regx}" --account-id "${ACCOUNT_NUM}" --query VaultList[*].VaultName --output text 2>&1|xargs -n1)
|
||||
if grep -q -E 'AccessDenied|UnauthorizedOperation|AuthorizationError' <<< "$LIST_OF_VAULTS"; then
|
||||
textInfo "$regx: Access Denied trying to list vaults" "${regx}"
|
||||
continue
|
||||
fi
|
||||
# Check for unsupported regions
|
||||
if grep -q -E 'error' <<< "${LIST_OF_VAULTS}"; then
|
||||
textInfo "$regx: An error occurred when calling the ListVaults operation - check if this region is supported" "${regx}"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_VAULTS ]]; then
|
||||
for vault in $LIST_OF_VAULTS;do
|
||||
VAULT_POLICY_STATEMENTS=$($AWSCLI glacier $PROFILE_OPT get-vault-access-policy --region $regx --account-id $ACCOUNT_NUM --vault-name $vault --output json --query policy.Policy 2>&1)
|
||||
VAULT_POLICY_STATEMENTS=$($AWSCLI glacier ${PROFILE_OPT} get-vault-access-policy --region "${regx}" --account-id "${ACCOUNT_NUM}" --vault-name "${vault}" --output json --query policy.Policy 2>&1)
|
||||
if [[ $VAULT_POLICY_STATEMENTS == *GetVaultAccessPolicy* ]]; then
|
||||
textInfo "$regx: Vault $vault doesn't have any policy" "$regx" "$vault"
|
||||
textInfo "${regx}: Vault $vault doesn't have any policy" "${regx}" "$vault"
|
||||
else
|
||||
VAULT_POLICY_BAD_STATEMENTS=$(echo $VAULT_POLICY_STATEMENTS | jq '. | fromjson' | jq '.Statement[] | select(.Effect=="Allow") | select(.Principal=="*" or .Principal.AWS=="*" or .Principal.CanonicalUser=="*")')
|
||||
VAULT_POLICY_BAD_STATEMENTS=$(jq '. | fromjson' <<< "${VAULT_POLICY_STATEMENTS}" | jq '.Statement[] | select(.Effect=="Allow") | select(.Principal=="*" or .Principal.AWS=="*" or .Principal.CanonicalUser=="*")')
|
||||
if [[ $VAULT_POLICY_BAD_STATEMENTS != "" ]]; then
|
||||
textFail "$regx: Vault $vault has policy which allows access to everyone" "$regx" "$vault"
|
||||
textFail "${regx}: Vault $vault has policy which allows access to everyone" "${regx}" "$vault"
|
||||
else
|
||||
textPass "$regx: Vault $vault has policy which does not allow access to everyone" "$regx" "$vault"
|
||||
textPass "${regx}: Vault $vault has policy which does not allow access to everyone" "${regx}" "$vault"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
else
|
||||
textInfo "$regx: No Glacier vaults found" "$regx"
|
||||
textInfo "${regx}: No Glacier vaults found" "${regx}"
|
||||
fi
|
||||
done
|
||||
}
|
||||
}
|
||||
|
||||
+10
-2
@@ -25,11 +25,19 @@ CHECK_CAF_EPIC_extra7148='Data Protection'
|
||||
|
||||
extra7148() {
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_EFS_SYSTEMS=$($AWSCLI efs describe-file-systems $PROFILE_OPT --region $regx --query 'FileSystems[*].FileSystemId' --output text)
|
||||
LIST_OF_EFS_SYSTEMS=$($AWSCLI efs describe-file-systems $PROFILE_OPT --region $regx --query 'FileSystems[*].FileSystemId' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_EFS_SYSTEMS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe file systems" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_EFS_SYSTEMS ]]; then
|
||||
for filesystem in $LIST_OF_EFS_SYSTEMS; do
|
||||
# if retention is 0 then is disabled
|
||||
BACKUP_POLICY=$($AWSCLI efs describe-backup-policy $PROFILE_OPT --region $regx --file-system-id $filesystem --query BackupPolicy --output text)
|
||||
BACKUP_POLICY=$($AWSCLI efs describe-backup-policy $PROFILE_OPT --region $regx --file-system-id $filesystem --query BackupPolicy --output text 2>&1)
|
||||
if [[ $(echo "$BACKUP_POLICY" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe backup policy" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $BACKUP_POLICY == "DISABLED" ]]; then
|
||||
textFail "$regx: File system $filesystem does not have backup enabled!" "$regx" "$filesystem"
|
||||
else
|
||||
|
||||
@@ -26,12 +26,16 @@ CHECK_CAF_EPIC_extra7149='Data Protection'
|
||||
extra7149() {
|
||||
# "Check if Redshift cluster has audit logging enabled "
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_REDSHIFT_CLUSTERS=$($AWSCLI redshift describe-clusters $PROFILE_OPT --region $regx --query 'Clusters[*].ClusterIdentifier' --output text)
|
||||
LIST_OF_REDSHIFT_CLUSTERS=$($AWSCLI redshift describe-clusters $PROFILE_OPT --region $regx --query 'Clusters[*].ClusterIdentifier' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_REDSHIFT_CLUSTERS" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe clusters" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_REDSHIFT_CLUSTERS ]]; then
|
||||
for redshiftcluster in $LIST_OF_REDSHIFT_CLUSTERS; do
|
||||
REDSHIFT_SNAPSHOT_ENABLED=$($AWSCLI redshift describe-cluster-snapshots $PROFILE_OPT --region $regx --cluster-identifier $redshiftcluster --snapshot-type automated)
|
||||
if [[ $REDSHIFT_SNAPSHOT_ENABLED ]]; then
|
||||
textPass "$regx: Redshift cluster $redshiftcluster has automated snapshots $REDSHIFT_SNAPSHOT_ENABLED" "$regx" "$redshiftcluster"
|
||||
textPass "$regx: Redshift cluster $redshiftcluster has automated snapshots." "$regx" "$redshiftcluster"
|
||||
else
|
||||
textFail "$regx: Redshift cluster $redshiftcluster has automated snapshots disabled!" "$regx" "$redshiftcluster"
|
||||
fi
|
||||
|
||||
+26
-16
@@ -24,25 +24,35 @@ CHECK_DOC_extra715='https://docs.aws.amazon.com/elasticsearch-service/latest/dev
|
||||
CHECK_CAF_EPIC_extra715='Logging and Monitoring'
|
||||
|
||||
extra715(){
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_DOMAINS=$($AWSCLI es list-domain-names $PROFILE_OPT --region $regx --query DomainNames --output text)
|
||||
if [[ $LIST_OF_DOMAINS ]]; then
|
||||
for domain in $LIST_OF_DOMAINS;do
|
||||
SEARCH_SLOWLOG_ENABLED=$($AWSCLI es describe-elasticsearch-domain-config --domain-name $domain $PROFILE_OPT --region $regx --query DomainConfig.LogPublishingOptions.Options.SEARCH_SLOW_LOGS.Enabled --output text |grep -v ^None|grep -v ^False)
|
||||
if [[ $SEARCH_SLOWLOG_ENABLED ]];then
|
||||
textPass "$regx: Amazon ES domain $domain SEARCH_SLOW_LOGS enabled" "$regx" "$domain"
|
||||
else
|
||||
textFail "$regx: Amazon ES domain $domain SEARCH_SLOW_LOGS disabled!" "$regx" "$domain"
|
||||
fi
|
||||
INDEX_SLOWLOG_ENABLED=$($AWSCLI es describe-elasticsearch-domain-config --domain-name $domain $PROFILE_OPT --region $regx --query DomainConfig.LogPublishingOptions.Options.INDEX_SLOW_LOGS.Enabled --output text |grep -v ^None|grep -v ^False)
|
||||
if [[ $INDEX_SLOWLOG_ENABLED ]];then
|
||||
textPass "$regx: Amazon ES domain $domain INDEX_SLOW_LOGS enabled" "$regx" "$domain"
|
||||
else
|
||||
textFail "$regx: Amazon ES domain $domain INDEX_SLOW_LOGS disabled!" "$regx" "$domain"
|
||||
for regx in ${REGIONS}; do
|
||||
LIST_OF_DOMAINS=$("${AWSCLI}" es list-domain-names ${PROFILE_OPT} --region "${regx}" --query 'DomainNames[].DomainName' --output text 2>&1)
|
||||
if [[ $(echo "${LIST_OF_DOMAINS}" | grep -E 'AccessDenied|UnauthorizedOperation') ]]; then
|
||||
textInfo "${regx}: Access Denied trying to list domain names" "${regx}"
|
||||
continue
|
||||
fi
|
||||
if [[ "${LIST_OF_DOMAINS}" ]]; then
|
||||
for domain in ${LIST_OF_DOMAINS}; do
|
||||
SLOWLOG_ENABLED=$("${AWSCLI}" es describe-elasticsearch-domain-config --domain-name "${domain}" ${PROFILE_OPT} --region "${regx}" --query 'DomainConfig.LogPublishingOptions.Options.[SEARCH_SLOW_LOGS.Enabled, INDEX_SLOW_LOGS.Enabled]' --output text 2>&1)
|
||||
if [[ $(echo "${SLOWLOG_ENABLED}" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "${regx}: Access Denied trying to get ES domain config for ${domain}" "${regx}"
|
||||
continue
|
||||
fi
|
||||
read -r SEARCH_SLOWLOG_ENABLED INDEX_SLOWLOG_ENABLED <<< "${SLOWLOG_ENABLED}" && {
|
||||
if [[ $(tr '[:upper:]' '[:lower:]' <<< "${SEARCH_SLOWLOG_ENABLED}") == "true" ]]; then
|
||||
textPass "${regx}: Amazon ES domain ${domain} SEARCH_SLOW_LOGS enabled" "${regx}" "${domain}"
|
||||
else
|
||||
textFail "${regx}: Amazon ES domain ${domain} SEARCH_SLOW_LOGS disabled!" "${regx}" "${domain}"
|
||||
fi
|
||||
|
||||
if [[ $(tr '[:upper:]' '[:lower:]' <<< "${INDEX_SLOWLOG_ENABLED}") == "true" ]]; then
|
||||
textPass "${regx}: Amazon ES domain ${domain} INDEX_SLOW_LOGS enabled" "${regx}" "${domain}"
|
||||
else
|
||||
textFail "${regx}: Amazon ES domain ${domain} INDEX_SLOW_LOGS disabled!" "${regx}" "${domain}"
|
||||
fi
|
||||
}
|
||||
done
|
||||
else
|
||||
textInfo "$regx: No Amazon ES domain found" "$regx"
|
||||
textInfo "${regx}: No Amazon ES domain found" "${regx}"
|
||||
fi
|
||||
done
|
||||
}
|
||||
|
||||
@@ -26,7 +26,11 @@ CHECK_CAF_EPIC_extra7150='Data Protection'
|
||||
extra7150(){
|
||||
# "Check if Elastic Load Balancers have delete protection enabled."
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[*].LoadBalancerArn' --output text|xargs -n1)
|
||||
LIST_OF_ELBSV2=$($AWSCLI elbv2 describe-load-balancers $PROFILE_OPT --region $regx --query 'LoadBalancers[*].LoadBalancerArn' --output text 2>&1|xargs -n1 )
|
||||
if [[ $(echo "$LIST_OF_ELBSV2" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to describe load balancers" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_ELBSV2 ]]; then
|
||||
for elb in $LIST_OF_ELBSV2; do
|
||||
CHECK_DELETION_PROTECTION_ENABLED=$($AWSCLI elbv2 describe-load-balancer-attributes $PROFILE_OPT --region $regx --load-balancer-arn $elb --query Attributes[*] --output text|grep "deletion_protection.enabled"|grep true )
|
||||
|
||||
@@ -27,7 +27,11 @@ CHECK_CAF_EPIC_extra7151='Data Protection'
|
||||
extra7151(){
|
||||
# "Check if DynamoDB tables point-in-time recovery (PITR) is enabled"
|
||||
for regx in $REGIONS; do
|
||||
LIST_OF_DYNAMODB_TABLES=$($AWSCLI dynamodb list-tables $PROFILE_OPT --region $regx --query 'TableNames[*]' --output text)
|
||||
LIST_OF_DYNAMODB_TABLES=$($AWSCLI dynamodb list-tables $PROFILE_OPT --region $regx --query 'TableNames[*]' --output text 2>&1)
|
||||
if [[ $(echo "$LIST_OF_DYNAMODB_TABLES" | grep -E 'AccessDenied|UnauthorizedOperation|AuthorizationError') ]]; then
|
||||
textInfo "$regx: Access Denied trying to list tables" "$regx"
|
||||
continue
|
||||
fi
|
||||
if [[ $LIST_OF_DYNAMODB_TABLES ]]; then
|
||||
for dynamodb_table in $LIST_OF_DYNAMODB_TABLES; do
|
||||
POINT_IN_TIME_RECOVERY_ENABLED=$($AWSCLI dynamodb describe-continuous-backups $PROFILE_OPT --region $regx --table-name $dynamodb_table | jq '.[].PointInTimeRecoveryDescription | select(.PointInTimeRecoveryStatus=="ENABLED") | .PointInTimeRecoveryStatus')
|
||||
|
||||
@@ -23,31 +23,32 @@
|
||||
# --tech-privacy
|
||||
|
||||
CHECK_ID_extra7152="7.152"
|
||||
CHECK_TITLE_extra7152="[extra7152] Enable Privacy Protection for for a Route53 Domain"
|
||||
CHECK_TITLE_extra7152="[extra7152] Enable Privacy Protection for for a Route53 Domain (us-east-1 only)"
|
||||
CHECK_SCORED_extra7152="NOT_SCORED"
|
||||
CHECK_CIS_LEVEL_extra7152="EXTRA"
|
||||
CHECK_SEVERITY_extra7152="Medium"
|
||||
CHECK_ASFF_RESOURCE_TYPE_extra7152="AwsRoute53Domain"
|
||||
CHECK_ALTERNATE_check7152="extra7152"
|
||||
CHECK_SERVICENAME_extra7152="route53"
|
||||
CHECK_RISK_extra7152='Without privacy protection enabled, ones personal information is published to the public WHOIS database'
|
||||
CHECK_RISK_extra7152='Without privacy protection enabled; ones personal information is published to the public WHOIS database'
|
||||
CHECK_REMEDIATION_extra7152='Ensure default Privacy is enabled'
|
||||
CHECK_DOC_extra7152='https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/domain-privacy-protection.html'
|
||||
CHECK_CAF_EPIC_extra7152='Data Protection'
|
||||
|
||||
extra7152(){
|
||||
echo "Route53 is a global service, looking for domains in US-EAST-1"
|
||||
# Route53 is a global service, looking for domains in US-EAST-1
|
||||
# this is also valid for GovCloud https://docs.aws.amazon.com/govcloud-us/latest/UserGuide/setting-up-route53.html
|
||||
DOMAIN_NAMES=$($AWSCLI route53domains list-domains $PROFILE_OPT --region us-east-1 --query 'Domains[*].DomainName' --output text )
|
||||
if [[ $DOMAIN_NAMES ]];then
|
||||
for domain_name in $DOMAIN_NAMES;do
|
||||
DOMAIN_DETAIL=$($AWSCLI route53domains get-domain-detail $PROFILE_OPT --region us-east-1 --query 'AdminPrivacy' --domain-name $domain_name)
|
||||
if [[ $DOMAIN_DETAIL == false ]]; then
|
||||
textFail "$regx: Contact information public for: $domain_name" "$regx" "$domain_name"
|
||||
textFail "us-east-1: Contact information public for: $domain_name" "us-east-1" "$domain_name"
|
||||
else
|
||||
textPass "$regx: All contact information is private for: $domain_name" "$regx" "$domain_name"
|
||||
textPass "us-east-1: All contact information is private for: $domain_name" "us-east-1" "$domain_name"
|
||||
fi
|
||||
done
|
||||
else
|
||||
textPass "$regx: No Domain Names found" "$regx"
|
||||
textInfo "us-east-1: No Domain Names found" "us-east-1"
|
||||
fi
|
||||
}
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user